IJNSA 01
Classification of Source Code Vulnerabilities and Analysis of Detection Methods: Evaluation, Comparison, and Proposed
Approaches
Nin Ho Le Viet 1,2 , Chieu Ta Quang 2 , Cuong Nguyen Van 3 and Tuan Nguyen Kim 3 , 1Duy Tan University, Vietnam,
2Thuyloi University, Vietnam, 3Phenikaa University, Vietnam
ABSTRACT
Source code vulnerabilities are an important cause leading to many information security incidents in modern software systems. Due to the diversity of causes and technical characteristics, source code vulnerability detection is difficult to be effectively addressed by a single method. This paper focuses on classifying, evaluating, and comparing source code vulnerability detection methods in order to provide a systematic view of this problem. The first contribution of the paper is to develop a classification approach for source code vulnerabilities based on causes and technical characteristics, thereby clarifying the nature of each vulnerability group. Next, the paper analyzes and evaluates common detection method categories, including static analysis, dynamic analysis, and machine learning and deep learning based methods, with consideration of the application scope and characteristic limitations of each approach. On that basis, the paper conducts an overall comparison among the methods to indicate that there does not exist a single technique that can effectively detect every type of source code vulnerability. Finally, the paper proposes a combined approach to leverage the advantages of different methods in source code vulnerability detection. The results and analyses in the paper are expected to support researchers and software engineers in evaluating, selecting, and orienting the development of vulnerability detection solutions in the future.
KEYWORDS
Source code vulnerabilities, Software security, Vulnerability detection, Static and dynamic analysis, Machine learning
1. INTRODUCTION
In modern information systems, software plays a central role in delivering services across critical domains such as e-government, finance, healthcare, cloud computing, and artificial intelligence. As software systems become larger and more interconnected, source code vulnerabilities have remained a major root cause of security incidents, leading to system compromise, data leakage, and service disruption. In practice, vulnerabilities may arise from diverse causes and manifest in different technical forms, ranging from memory management errors such as buffer overflow [1], out-of-bounds access [2], and use-after-free [3], to input handling flaws such as SQL injection [4], command injection [5], and format string vulnerabilities [6]. Many vulnerabilities, especially those depending on program logic and context, may not trigger immediate runtime failures and only appear under specific execution scenarios, which makes detection particularly difficult.
Static analysis inspects programs without execution, leveraging syntactic rules and program analysis techniques to identify suspicious patterns early in the development process. While widely adopted, static analysis often suffers from high false positives and limited capability in handling context-dependent vulnerabilities. Dynamic analysis and fuzzing, in contrast, focus on runtime behaviors and input-driven testing to uncover vulnerabilities that only manifest during execution. Although such techniques can provide stronger evidence of exploitability, their effectiveness depends heavily on test coverage and the diversity of generated inputs. More recently, machine learning and deep learning based methods have been proposed to exploit statistical and structural features of source code for automated vulnerability detection [7]. These learning-based approaches reduce reliance on handcrafted rules, yet their performance still depends on the quality of training data, feature representation, and generalization capability.
Despite notable progress, source code vulnerability detection remains a complex problem in which no single technique can reliably detect all vulnerability types across real-world settings. Many existing works focus on improving individual detection methods or reporting performance on limited vulnerability sets, while the relationship between vulnerability characteristics and method suitability is often not made explicit. As a result, selecting appropriate detection techniques for complex, multi-language software systems remains challenging. This observation motivates the need for a systematic perspective that (i) Clarifies vulnerability categories, (ii) Analyzes detection methods under consistent criteria, and (iii) Supports hybrid-oriented thinking, where complementary methods can be combined to mitigate individual limitations.
To address this need, this paper adopts a structured and analytical viewpoint on source code vulnerability detection. Rather than proposing a single algorithm and claiming universal superiority, the paper focuses on organizing the problem space and providing a coherent comparison that supports both research understanding and practical decision making. The main contributions of this paper are threefold:
(i) Vulnerability classification by causes and technical characteristics: The paper develops a classification approach that groups vulnerabilities according to their causes and technical manifestations, thereby clarifying the nature and detection challenges of each group, including memory-related vulnerabilities[8] and input handling vulnerabilities [9].
(ii) Evaluation and comparison of major detection method categories: The paper analyzes representative method groups, static analysis, dynamic analysis/fuzzing [10], and learning-based approaches [11], and compares them using consistent qualitative criteria, highlighting their strengths, limitations, and applicability boundaries across vulnerability types.
(iii) Hybrid-oriented direction and proposed approach discussion: Based on the comparative findings, the paper discusses a combined approach that leverages complementary advantages of different techniques, aligning with recent hybridoriented research trends [12]. The experimental part is used to illustrate feasibility and to support the evaluation and comparison statements, rather than aiming at large-scale optimization or state-of-the-art claims.
2. SOURCE CODE VULNERABILITY CLASSIFICATION
Source code vulnerabilities appear in diverse forms due to differences in causes, technical characteristics, and exploitation contexts. Since each type exhibits distinct structural and behavioral properties, treating vulnerabilities as a homogeneous group limits effective analysis and evaluation of detection methods. Vulnerability classification clarifies the relationship between vulnerability characteristics and detection capabilities, providing a structured basis for comparing different approaches. It therefore serves as a foundational step for the analytical and comparative discussions presented in this paper.
2.1. Classification Based on Causes and Technical Characteristics
Classifying source code vulnerabilities by their causes and technical characteristics is a common approach in software security research. This perspective clarifies the relationship between code structure, runtime behavior, and exploitability, allowing vulnerabilities to be grouped into several main categories as follows: Memory management related vulnerabilities [13]: Memory management vulnerabilities occur when a program performs unsafe operations on memory regions, leading to data overwriting or unauthorized memory access. Common forms Include buffer overflow, out-of-bounds access, and use-after-free. This group of vulnerabilities is frequently encountered in programming languages that allow manual memory management, such as C and C++. The following example illustrates a buffer overflow case caused by the lack of input length control:
void copy(char *input) {
char buf[16];
strcpy(buf, input);}
In the above code snippet, if the input data exceeds the size of buf, adjacent memory regions may be overwritten. Detecting this type of vulnerability becomes difficult when the program contains multiple conditional branches or depends on dynamic input data, making it challenging for conventional testing techniques to achieve sufficient coverage.
2.2. Classification Based on Stages in The Software Development Life Cycle
In addition to cause-based classification, source code vulnerabilities can be analyzed according to the stage of the software development life cycle at which they arise. This perspective helps link vulnerabilities to appropriate detection methods and supports more effective method selection and evaluation.
Design-level vulnerabilities [17]:
Design-level vulnerabilities emerge at the early stages of the software development life cycle, when system architecture, authorization models, or business process flows are defined. Vulnerabilities in this group are typically related to inadequately designed authentication and authorization mechanisms, improper functional separation, or the lack of security constraints at the architectural level. Since they exist before concrete source code is implemented, design-level vulnerabilities are often difficult to identify through pure source code inspection. Detecting vulnerabilities at the design level requires analyzing system architecture and initial
security assumptions, rather than relying solely on program syntax or structure. If not identified early, these vulnerabilities may propagate into the implementation stage and become more difficult to remediate in later phases of the software life cycle.
Implementation-level vulnerabilities [18]:
Implementation-level vulnerabilities arise during the programming phase, when designs are translated into concrete source code. This group includes common issues such as unsafe memory management, insufficient input validation, errors in condition checking, and improper use of APIs and libraries. It is the most extensively studied group of vulnerabilities and is often directly related to the structure and content of source code. Because they occur at the implementation level, these vulnerabilities can be detected through source code inspection techniques or by observing program execution behavior. However, the effectiveness of detection strongly depends on the characteristics of each vulnerability type, as
well as the coverage capability of the applied method.
Vulnerabilities in cloud services and microservices architectures [22]:
In cloud and microservices environments, vulnerabilities may arise not only within individual services but also from their interactions. Inconsistent authentication or authorization assumptions across components can create weaknesses that are difficult to detect. For example:
@app.route(“/internal/data”)
def get_data():
return sensitive_data
While this code may appear safe in isolation, it can become vulnerable when exposed beyond its intended scope within a distributed system. Detecting such issues requires considering deployment architecture, communication flows, and configuration settings rather than evaluating services independently.
These examples show that vulnerability risk and detection requirements depend heavily on deployment context, emphasizing the need to select and combine appropriate detection methods in modern systems.
3. VULNERABILITY DETECTION METHODS
3.1. Static Analysis (SAST)
Static Application Security Testing (SAST) [24] is a widely used approach that analyzes source or intermediate code without execution, relying on predefined rules and vulnerability patterns to Overall, SAST is well suited for structure-related vulnerabilities such as memory errors and unsafe API usage, but limited for context-dependent flaws, highlighting the need for complementary methods.
3.2. Dynamic Analysis (DAST, Fuzzing)
Dynamic Application Security Testing (DAST) [25] is a group of vulnerability detection methods based on observing program behavior during execution. Unlike static analysis, DAST does not directly inspect source code structure but instead focuses on evaluating program responses to different inputs and usage scenarios. This approach is particularly suitable for vulnerabilities that only manifest when the program is executed under specific conditions. detect weaknesses early in development.
3.3. Machine Learning-based Vulnerability Detection
Traditional machine learning approaches for source code vulnerability detection [28] aim to overcome the limitations of rule-based analysis by learning from labeled source code data. Instead of relying solely on predefined patterns, these models distinguish between secure and vulnerable code through data-driven training, enabling better adaptation to diverse vulnerabilities encountered in practice.
3.5. LLM-based/Hybrid Approaches
LLM-based approaches [38] and hybrid models [39] aim to leverage large-scale semantic reasoning capabilities while addressing the limitations of individual detection methods. Rather than treating vulnerability detection purely as a classification task, these approaches integrate multiple techniques within a unified pipeline.
Representative source-code-oriented models include CodeLLaMA [40], StarCoder [41], and GPT-4 [42]. CodeLLaMA is suitable for research due to its specialization and independent deployment capability; StarCoder provides an open-source multilingual alternative; GPT-4 serves as a reasoning benchmark despite cost and reproducibility limitations.
LLM-based methods utilize pre-trained models to analyze and reason about code, either directly or through task-specific fine-tuning. In hybrid systems, LLMs are typically integrated with static analysis, dynamic analysis, or machine learning. Alerts generated by SAST or ML models can be further examined by LLMs to reassess severity and reduce false positives. Unlike earlier deep learning models, LLMs capture syntax, semantics, and global context simultaneously. For example, suspicious access-control code identified by static analysis can be re-evaluated by an LLM to determine whether it represents a genuine vulnerability or a legitimate usage pattern.
The main advantage of LLM-based and hybrid approaches lies in their semantic reasoning capability, particularly for logic and context-dependent vulnerabilities. However, high computational cost, deployment complexity, and stability concerns limit their standalone use. Therefore, LLMs are most effective as complementary components within a broader detection architecture rather than as full replacements for traditional methods.
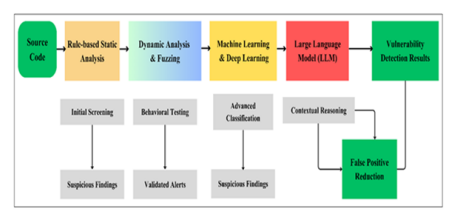
3.6. Proposed Source Code Vulnerability Detection Architecture
The analyses in Sections 3.1-3.5 indicate that each detection method is effective only within certain scopes. Static analysis provides early detection but often generates high false positives; dynamic analysis and fuzzing validate runtime behavior but depend on test coverage; machine learning and deep learning improve detection of complex patterns but rely on data quality and
computational resources; large language models offer strong semantic reasoning but face challenges in stability and deployment efficiency. These limitations suggest that no single method can fully satisfy practical detection requirements.
Based on this insight, a hybrid-oriented architecture is proposed, organizing complementary methods into functional layers rather than replacing existing techniques.
As illustrated in Figure 1, the pipeline includes:
(i) Static analysis for early-stage screening and broad coverage;
(ii) Dynamic analysis and fuzzing to validate execution-level vulnerabilities and reduce false positives;
(iii) Machine learning/deep learning models to analyze syntactic and structural patterns, particularly for complex or logic-related vulnerabilities;
(iv) Large language model-based reasoning for semantic reassessment and alert consolidation, helping reduce noise in final results.
Figure 1.Pipeline for source code vulnerability detection combining static analysis, dynamic analysis, machine learning, and large language models
4. EVALUATION AND COMPARISON OF SOURCE CODE VULNERABILITY
DETECTION METHODS
This section evaluates and compares the detection methods discussed in Section 3 to clarify their application scope, strengths, and limitations. The analysis provides a structured perspective on the overall landscape of source code vulnerability detection.
4.1. Evaluation Criteria
The comparison of methods is conducted based on qualitative criteria that reflect common requirements in both research and practical deployment, including: (i) Suitable vulnerability types: the groups of vulnerabilities that a method can effectively detect; (ii) Detection capability: the degree to which target vulnerabilities are correctly identified; (iii) False positives: the tendency to generate alerts that do not correspond to actual vulnerabilities; (iv) Computational and deployment cost: the resources required to operate the method; (v) Scalability: the suitability of the method when applied to large-scale or multilingual systems; and (vi)Context dependence:
5. PROPOSED MODEL AND EXPERIMENTAL EVALUATION
5.1. Hybrid Vulnerability Detection Model Combining ML and LLM
Based on the comparative analysis in Sections 3 and 4, this paper proposes a hybrid source code vulnerability detection model that combines traditional machine learning with a large language model to leverage complementary strengths at different stages of detection. CodeLLaMA-34B is employed at the triage stage to provide semantic and context-aware reasoning for suspicious code fragments.
5.2. Experimental setup
The experiments aim to provide illustrative validation rather than state-of-the-art benchmarking. The hybrid ML-LLM model is evaluated to examine whether semantic triage can reduce false positives while maintaining detection capability. The results should therefore be interpreted as empirical support for the hybrid rationale derived from the comparative analysis.
5.3. Experimental results and analysis
Table 2 presents an overall comparison between SAST, traditional machine learning models, and the proposed hybrid ML-LLM models on the Juliet Test Suite and Big-Vul datasets. Integrating CodeLLaMA-34B at the triage stage significantly reduces the False Positive Rate while preserving detection performance.
6. DISCUSSION
The experimental results in Section 5 provide several key observations regarding the effectiveness of different detection methods and the value of the proposed hybrid approach.
First, rule-based static analysis (SAST) achieves high Recall (above 0.80), reflecting strong coverage and early detection capability. However, its low Precision (≈0.48) and high False Positive Rate (above 0.40) confirm its limitations in handling context-dependent and logic-related vulnerabilities.
Traditional machine learning models, including Random Forest and XGBoost, significantly improve detection quality. The F1-score increases from approximately 0.60 (SAST) to 0.71-0.74, while the False Positive Rate decreases to 0.26-0.30. Nevertheless, relying solely on syntactic and structural features remains insufficient to fully eliminate false positives.
Integrating a large language model at the triage stage further enhances performance. The hybrid models reduce the False Positive Rate by approximately 25-35% compared to standalone ML models, while maintaining or slightly improving the F1-score (0.77-0.79). Using CodeLLaMA-34B improves Precision to above 0.80, demonstrating the benefit of semantic reasoning for distinguishing context-dependent cases.
7. CONCLUSION
This paper presents a systematic perspective on source code vulnerability detection, beginning with a structured classification of vulnerability types and followed by a comparative analysis of major detection approaches. The comparison clarifies the strengths, limitations, and applicability of each method group.
Based on this analysis, a hybrid detection model combining traditional machine learning with a large language model at the triage stage is introduced and evaluated on the Juliet Test Suite and Big-Vul datasets. The results demonstrate that the hybrid approach reduces the false positive rate while maintaining or improving the F1-score, confirming the feasibility of integrating complementary methods.
Although limited to baseline evaluation, the findings support the complementary role of machine learning and large language models in vulnerability detection. Future work may extend the evaluation to more diverse datasets, analyze computational cost in greater depth, and enhance interpretability through Explainable Artificial Intelligence techniques.
REFERENCES
[1] E. Kanaan, S. S. Alam and M. S. Akter, “Survey of Machine Learning Techniques for Detecting Buffer Overflow Vulnerabilities,” Apr. 30 2025, doi:10.13140/RG.2.2.22978.08640.
[2] R. Li, B. Zhang and C. Tang, “Identifying Exploitable Memory Objects for Out-of-Bound Write Vulnerabilities,” *Electronics Letters*, vol. 60, no. 5, pp. 1-4, Feb. 2024, doi:10.1049/ell2.13136.
[3] X. Zhao, H. Qu, J. Yi, J. Wang, M. Tian, and F. Zhao, “A fuzzer for detecting use-after-free vulnerabilities,” Mathematics, vol. 12, no. 21, Art. no. 3431, Nov. 2024, doi:10.3390/math12213431.
[4] L. Aburashed, M. A. Almoush, and W. Alrefai, “SQL injection attack detection using machine learning algorithms,” Semarak International Journal of Machine Learning, vol. 2, no. 1, pp. 112–120, Jun. 2024, doi:10.37934/sijml.2.1.112.
[5] X. Yin, R. Cai, Y. Zhang, L. Li, Q. Yang, and S. Liu, “Accelerating Command Injection Vulnerability Discovery in Embedded Firmware with Static Backtracking Analysis,” in Proceedings of the 12th International Conference on the Internet of Things (IoT ’22), 2023, pp. 65–72, doi: 10.1145/3567445.3567458.
[6] S. Xu, Z. Jiang, and P. Xie, “FormatAEG: A framework for bypassing ASLR defense and automated exploitation of format string vulnerability,” The Computer Journal, vol. 67, no. 12, Oct. 2024, Art.
no. bxae069, doi: 10.1093/comjnl/bxae069.
[7] H. Yang, X. Gu, Z. Cui, et al., “CrossFuzz: Cross-contract fuzzing for smart contract vulnerability detection,” Science of Computer Programming, vol. 233, Jan. 2024, Art. no. 103076, doi: 10.1016/j.scico.2023.103076.
[8] S. Cao, X. Sun, W. Liu et al., “Learning to detect memory-related vulnerabilities,” ACM Transactions on Software Engineering and Methodology, vol. 33, no. 1, pp. 1–37, Jan. 2024.
[9] C. Brandi, G. Perrone, and S. Romano, “Sniping at web applications to discover input-handling vulnerabilities,” Journal of Computer Virology and Hacking Techniques, vol. 20, no. 2, Apr. 2024, pp. 1–18, doi: 10.1007/s11416-024-00518-0.
[10] R. Singh, M. Gupta, and S. M. Patil, “Analysis of web application vulnerabilities using dynamic application security testing,” in Proc. 2024 IEEE 9th International Conference for Convergence in Technology (I2CT), Pune, India, Apr. 2024, doi:10.1109/I2CT61223.2024.10543484.
[11] M. Bresil, P. Prasad, and U. Bukar, “Deep learning-based vulnerability detection solutions in smart contracts: A comparative and meta-analysis of existing approaches,” IEEE Access, vol. 13, pp. 1–24, 2025, doi: 10.1109/ACCESS.2025.3532326.
[12] Q. Yu, “From rule-driven to data-driven: Technological evolution, challenges, and future trends in smart contract vulnerability detection,” Transactions on Computer Science and Intelligent Systems Research, Jul. 2025, doi: 10.62051/c9jgtf18.
[13] S. Cao, X. Sun, C. Tao, et al., “MVD: Memory-related vulnerability detection based on flow-sensitive graph neural networks,” in Proc. Int. Conf. on Software Engineering and Knowledge Engineering (SEKE), Redwood City, CA, USA, Mar. 2022, doi:10.1145/3510003.3510219.
[14] S. Cao, B. He, X. Sun, Y. Ouyang, C. Zhang, X. Wu, T. Su, L. Bo, B. Li, C. Ma, J. Li, and T. Wei, “ODDFUZZ: Discovering Java deserialization vulnerabilities via structure-aware directed greybox fuzzing,” arXiv preprint arXiv:2304.04233, 2023.
[15] V. Felmetsger, L. Cavedon, C. Kruegel, and G. Vigna, “Toward Automated Detection of Logic Vulnerabilities in Web Applications,”19th USENIX Security Symposium (USENIX Security 10), Washington, DC, USA, 2010.
[16] Z. Mousavi, C. Islam, M. A. Babar, A. Abuadbba, and K. Moore, “Detecting Misuses of Security APIs: A Systematic Review,” ACM Computing Surveys, vol. 57, no. 12, pp. 1-39, 2025.
[17] Q. Rouland, B. Hamid, and J. Jaskolka, “A model-driven formal methods approach to software architectural security vulnerabilities specification and verification,” J. Syst. Softw., vol. 219, 112219, 2025, doi: 10.1016/j.jss.2024.112219.
[18] S. Rehman and K. Mustafa, “Research on software design level security vulnerabilities, ” ACM SIGSOFT Software Engineering Notes, vol. 34, no. 6, pp. 1-5, Dec. 2009.
[19] I. E. Kezron, “Securing the AI supply chain: Mitigating vulnerabilities in AI model development and deployment,” World Journal of Advanced Research and Reviews, vol. 22, no. 2, pp. 1394-1403, May 2024, doi:10.30574/wjarr.2024.22.2.1394.
[20] K. Lian, L. Zhang, M. Yang, et al., “Careless Retention and Management: Understanding and Detecting Data Retention Denial-of-Service Vulnerabilities in Java Web Containers,” in Proc. USENIX Security Symposium, 2025.
[21] N. Neshenko, E. Bou-Harb, J. Crichigno, G. Kaddoum, and N. Ghani, “Demystifying IoT Security: An Exhaustive Survey on IoT Vulnerabilities and a First Empirical Look on Internet-Scale IoT Exploitations,” IEEE Communications Surveys & Tutorials, vol. 21, no. 3, pp. 2702-2733, 2019, doi:10.1109/COMST.2019.2910750.
[22] S. Duggirala and D. R. P. Singh, “Securing Microservices in the Cloud: Addressing Emerging Threats and Vulnerabilities,” International Journal of Research in Modern Engineering & Emerging Technology, vol. 13, no. 6, 2025, doi:10.63345/ijrmeet.org.v13.i6.16.
[23] K. Karthik, S. Singh, M. Mohana, et al., “Temporal Analysis and Common Weakness Enumeration (CWE) Code Prediction for Software Vulnerabilities Using Machine Learning,” in Proc. 8th Int. Conf. on Computational System and Information Technology for Sustainable Solutions (CSITSS), 2024, doi:10.1109/CSITSS64042.2024.10816791.
[24] V. Farrapo, E. Rodrigues, and J. C. Machado, “Evaluating the Use of Open-Source and Standalone SAST Tools for Detecting Vulnerabilities in C/C++ Projects,” in Proc. Int. Conf. on Software Technologies, 2025, doi:10.5220/001348350003929.
[25] S. Millar, D. Podgurski, P. Miller, et al., “Optimising Vulnerability Triage in DAST with Deep Learning,” in Proc. 15th ACM Workshop on Artificial Intelligence and Security (AISec), co-located with CCS, 2022, pp. 1-12, doi:10.1145/3560830.3563724.
[26] S. Godboley, K. Gupta, and M. Rani Golla, “AV-AFL: A Vulnerability Detection Fuzzing Approach by Proving Non-reachable Vulnerabilities using Sound Static Analyser,” in Proc. Int. Conf. on Software Technologies, 2022, doi:10.5220/001103290003176.
[27] R. Liao, X. Yan, K. Zhu, et al., “Balancing validity and vulnerability: Knowledge driven seed generation via LLMs for deep learning library fuzzing,” Applied Sciences, vol. 15, no. 19, Art. no. 10396, Sep. 2025, doi: 10.3390/app151910396.
[28] S. Bin Hlayil and S. Lida Xu, “Machine learning based vulnerability detection and classification in Internet of Things device security,” Electronics, vol. 12, no. 18, Art. no. 3927, Sep. 2023.
[29] C. Xiong, “Detection of buffer overflow vulnerability in embedded development programs based on SVM algorithm,” in Proc. SPIE, vol. 13069, Art. no. 130690I, Jul. 2025.
[30] C. Singh, V. Vijayalakshmi, and H. Raj, “A machine learning approach for web application vulnerability detection using random forest,” International Journal for Research in Applied Science & Engineering Technology (IJRASET), vol. 10, no. 12, pp. 4837-4843, Dec. 2022, doi: 10.22214/ijraset.2022.48397.
[31] M. Zhang, S. Fu, P. Shi, et al., “An XGBoost based vulnerability analysis of smart grid cascading failures under topology attacks,” in Proc. IEEE Int. Conf. Smart Grid Communications (SmartGridComm), Oct. 2021, pp. 1-6, doi: 10.1109/SMC52423.2021.9658797.
[32] J. Zhu, H. Ge, and R. Luo, “A method to detect vulnerability of Java source code based on AST and graph attention networks,” in Proc. IEEE Int. Conf. on Software Engineering and Service Science (ICSTE), Aug. 2024, pp. 1-6, doi: 10.1109/ICSTE63875.2024.00010.
[33] Y. Wang, J. Zhao, L. Zhu, et al., “Smart contract symbol execution vulnerability detection method based on CFG path pruning,” in Proc. Int. Symposium on Reliable Distributed Systems Workshops (SRDSW), Jul. 2023, pp. 1-6, doi: 10.1145/3594556.3594618.
[34] Y. Wang, J. Zhao, L. Zhu, et al., “Smart contract symbol execution vulnerability detection method based on CFG path pruning,” in Proc. International Symposium on Reliable Distributed Systems Workshops (SRDSW), Jul. 2023, pp. 1-6, doi: 10.1145/3594556.3594618.
[35] Y. He, G. Lin, F. Li, et al., “Enhancing deep learning vulnerability detection through imbalance loss functions: An empirical study,” in Proc. Asia Pacific Symposium on Software Engineering (APSEC), Jul. 2024, pp. 1-8, doi: 10.1145/3671016.3671379.
[36] Y. Cao, Y. Dong, and J. Peng, “Vulnerability detection based on transformer and high quality number embedding,” Concurrency and Computation: Practice and Experience, vol. 36, no. 18, Art. no. e8292, Sep. 2024, doi: 10.1002/cpe.8292.
[37] T. Wu, L. Chen, G. Shi, et al., “Self attention based automated vulnerability detection with effective data representation,” in Proc. IEEE Int. Conf. on Parallel & Distributed Processing with Applications, Big Data & Cloud Computing, Sustainable Computing & Communications, Social Computing & Networking (ISPA/BDCloud/SocialCom/SustainCom), Sep. 2021, pp. 1-8, doi: 10.1109/ISPABDCloud-SocialCom-SustainCom52081.2021.00126.
[38] A. A. Mahyari, “Harnessing the power of LLMs in source code vulnerability detection,” in Proc. IEEE Military Communications Conference (MILCOM), Aug. 2024, pp. 1-6.
[39] D. Wang, J. Chen, X. Hu, et al., “SCVD-SA: A smart contract vulnerability detection method based on hybrid deep learning model and self-attention mechanism,” in Proc. IEEE Int. Conf. on Software Analysis, Evolution and Reengineering (SANER), Mar. 2024, pp. 1-10.
[40] S. Sultana, S. Afreen, and N. U. Eisty, “Code vulnerability detection: A comparative analysis of emerging large language models,” arXiv preprint arXiv:2409.10490, Sep. 2024.
[41] R. Li, L. Ben Allal, Y. Zi, et al., “StarCoder: May the source be with you!” arXiv preprint arXiv:2305.06161, Dec. 2023, doi: 10.48550/arXiv.2305.06161.
[42] J. Bae, S. Kwon, and S. Myeong, “Enhancing software code vulnerability detection using GPT-4o and Claude-3.5 Sonnet: A study on prompt engineering techniques,” Electronics, vol. 13, no. 13, Art. no. 2657, Jul. 2024, doi: 10.3390/electronics13132657.
[43] J. Haurogné, N. Basheer, and S. Islam, “Vulnerability detection using BERT based LLM model with transparency obligation practice towards trustworthy AI,” Machine Learning with Applications, vol. 16, Art. no. 100598, Nov. 2024, doi: 10.1016/j.mlwa.2024.100598.
[44] Y. Xia, H. Shao, and X. Deng, “VulCoBERT: A CodeBERT based system for source code vulnerability detection,” in Proc. Int. Conf. on Generative Artificial Intelligence and Information Security (GAIIS), May 2024, pp. 1-6, doi: 10.1145/3665348.3665391.
[45] R. Wang, S. Xu, S. Jiang, et al., “SCL-CVD: Supervised contrastive learning for code vulnerability detection via GraphCodeBERT,” Computers & Security, vol. 141, Art. no. 103994, Jul. 2024.
[46] NSA Center for Assured Software, “NIST SARD: Juliet Test Suite for C C plus plus,” Version 1.3, Oct. 2017. doi: 10.5281/zenodo.4701387. Available: https://doi.org/10.5281/zenodo.4701387
[47] B. Steeves, “Big-Vul: A Large-Scale C/C++ Vulnerability Dataset,” Hugging Face Datasets, 2022.
AUTHORS
Nin Ho Le Viet (First Author)is currently a Lecturer with the Faculty of Information Technology, Duy Tan University, Da Nang, Vietnam. He received the Engineering degree in Information Technology from the University of Science and Technology – the University of Danang in 2011, and the M.Sc. degree in Computer Science from Duy Tan University in 2015. His main research interests include information technology, software, artificial intelligence, and software security. He has co-authored several papers published in international journals indexed by ISI/Scopus and presented his work at national scientific conferences.
Tuan Nguyen Kim (Corresponding Author) received his Engineering degree in Electronics and Informatics from the University of Sciences – Hue University (1995), M.Sc. in IT from Hanoi University of Science and Technology (2003), and Ph.D. in Computer Science from Duy Tan University (2023). He is currently pursuing a second Ph.D. in Information Security at the Vietnam Academy of Cryptography Techniques. He serves as a lecturer at Phenikaa University and formerly held leadership roles at Hue University and Duy Tan University. His research focuses on post-quantum cryptography, secure protocols, and cybersecurity. He has published over 25 SCI/Scopus papers and 10 textbooks.
Cuong Nguyen Van is a researcher and lecturer in Computer Science at the School of Computing, Phenikaa University, Hanoi, Vietnam. He holds an M.Sc. degree in Computer Science, and his research focuses on source code vulnerability detection, cybersecurity, big language models, and data mining. His work centers on applying advanced machine learning and deep learning techniques to improve software security and analyze complex data-driven problems. He is actively involved in academic research and contributes to the development of secure and intelligent computing systems.
Chieu Ta Quang is a lecturer and researcher in the Department of Artificial Intelligence at Thuyloi University. He received his Ph.D. degrees in Computer Science from the University of Tours, France in 2015. His current research focuses on machine learning, deep learning, data analytics and big data. He has also published extensively in SCI/Scopus-indexed journals and international conferences and is the principal investigator or key member of multiple national-level research projects on digital transformation and intelligent systems in water resource management.