IJNSA 05
AI-ENHANCED NETWORK TRAFFIC ANALYSIS FOR PREVENTING FRAUD PAYMENT IN BANKS
Balavardhan Reddy and Amir Ahmed Ansari
School of Computer and Information Science, University of the Cumberlands, KY, USA
Department of Information Technology, Indiana Wesleyan University, IN, USA
ABSTRACT
The expansion in the use of digital banking, mobile payment services, and online financial services has put tremendous pressure on banking networks, making them vulnerable to sophisticated payment fraud schemes. The inflexibility of rule-based systems in detecting sophisticated payment fraud has led to the need for smarter solutions to detect payment fraud in banking networks. This study presents a framework for artificial intelligence-based network traffic analysis to detect payment fraud in banking networks. The proposed framework utilizes artificial intelligence to process vast amounts of data regarding network activities in real-time to detect payment fraud in banking networks. The study presents artificial intelligence-based network traffic analysis to detect payment fraud in banking networks. The proposed framework utilizes artificial intelligence to process vast amounts of data regarding network activities in real-time to detect payment fraud in banking networks. The proposed framework has been found to improve the accuracy of payment fraud detection in banking networks compared to rule-based systems. The proposed framework has been found to improve the accuracy of payment fraud detection in banking networks compared to rule-based systems.
KEYWORDS
In the digital finance domain, AI is responsible for intelligent network traffic analysis, which increases payment fraud detection and improves banking cybersecurity. Machine learning is the basis for anomaly detection, providing financial security and improving digital banking fraud prevention.
1. INTRODUCTION
The rapid evolution of digital technology has completely revolutionized the field of banking, where the flow of money is not only secure but has also become fast and easy through online portals. Anyone can perform many financial tasks, such as transferring funds, paying bills, and shopping online, anywhere, anytime. However, as the world becomes increasingly dependent on electronic payment systems, the scope for cybercriminals also widens, and payment scams have risen significantly [1]. Scammers target banks through phishing attacks, malware, account takeover, identity theft, and transaction manipulation.
The conventional bank fraud detection systems rely on conventional rule-based systems that rely on fixed thresholds to detect fraudulent transactions. Although such systems may offer basic security protection, they do not recognize advanced, intelligent, and continually changing types of fraudulent activities that masquerade as legitimate customer behavior [2]. As the number of transactions grows exponentially, it becomes extremely challenging to monitor such transactions in real time through conventional systems.
Artificial Intelligence (AI) has proven to be a significant force in helping banks detect fraud by looking through large amounts of network traffic, transactions, and patterns of user behavior to detect anomalies that may indicate fraud. Looking through the network traffic is an added layer of protection that monitors the movement of the data through the system, looking for unusual patterns of movement in the banking system. The combination of AI and network traffic analysis can create a powerful system that can detect fraudulent payment activity in a timely fashion [3].
2. BACKGROUND AND RELATED WORK
As the number of people adopting digital banking services increases, our financial transactions have not only become quicker and easier, but the chances of payment fraud have also increased in the same proportion. This has led to the detection of payment fraud as the primary focus of banking cybersecurity research [4]. Everywhere, people are using different techniques to detect payment frauds effectively in the field of banking cybersecurity research. Recently, Artificial Intelligence has become a buzzword in the field of cybersecurity research, as it can scan all the data available in a more effective manner and detect hidden patterns and anomalies. In this section, we will be discussing the source of payment frauds, how payment frauds can be detected using artificial intelligence, and how payment frauds can be detected by analyzing network traffic.
Unlike using transactional information alone, this research is advancing the field by proposing a multi-layered solution that includes artificial intelligence and network traffic monitoring. It addresses a gap in the present literature by showing how monitoring internal network communication (“how the network talks to itself”) can identify signs of frauds like unusual IP addresses and session lengths before a transaction is even made. Unlike the rigid rules-based systems commonly found in banking systems, this is a more dynamic solution.
2.1. Payment Fraud in Banking Systems
Payment fraud occurs when cybercriminals perpetrate illegal or unauthorized financial transactions for the purpose of obtaining money illegally [5]. In recent times, with the increasing use of online banking, credit cards, and electronic wallets, cybercriminals have developed more sophisticated schemes of deception to evade the watchful eye of the bank’s security systems. Common banking frauds include the misuse of credit cards, the theft of an individual’s identity, the hijacking of an individual’s account, payment scams through phishing, etc. These are often the result of vulnerabilities in the way we prove who we are or the way people generally behave. Traditional anti-fraud systems use rule-based systems that monitor specific indicators of fraud such as transaction limits or unusual source locations. However, these systems are not very effective against sophisticated fraud schemes, as the schemes themselves are constantly evolving.
2.2. AI-Based Fraud Detection
In recent times, Artificial Intelligence has proven to play an integral role in the early detection of fraud in the financial system. By studying past transactions, Artificial Intelligence algorithms are capable of detecting patterns that distinguish genuine from fraudulent transactions. Some of the most commonly used techniques for the same purpose include Random Forest, Support Vector Machines, Logistic Regression, and Neural Networks [6]. These techniques enable the early identification of suspect indicators such as high transaction rates, unusual spending habits, or unexplained login activity. Deep learning techniques also assist in this regard by identifying complex relationships that exist in numerous data attributes. Artificial Intelligence systems continue to learn from new data, allowing them to improve over time.
2.3. Network Traffic Analysis for Fraud Detection
Network traffic analysis is the lookout for unusual patterns of communication that the bank’s systems exhibit, such as unusual patterns of movement of data, unusual login attempts, and so forth [7]. Fraudsters always leave telltale signs of unusual activity, such as many failed login attempts, unusual IP address activity, unusual lengths of time spent in a session, or a flurry of rapid-fire transactions. By examining the network traffic, the bank can detect unusual patterns of activity that could be indicative of fraud before the transaction is processed. The inclusion of AI in the detection of such patterns can significantly enhance the bank’s ability to reduce the financial loss that it suffers as a result of payment fraud.
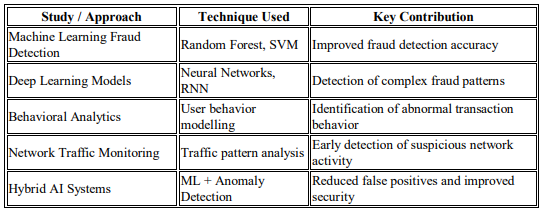
Table 1. Summary of Related Research in AI-Based Fraud Detection
3. RESEARCH OBJECTIVES
As digital payment systems increase in complexity, banks need to rely on cutting-edge technology to prevent and detect fraudulent activities [8]. The traditional methods of security fail to detect sophisticated methods of fraudulent activities because they are based on rigid rules and surveillance transaction. Thus, this study proposes that an artificial intelligence-based network traffic analysis framework should be developed to detect fraudulent activities in banking networks. The proposed approach integrates artificial intelligence and network surveillance to identify unusual patterns in transaction data, user behavior, and communication flow in banking networks.
The focus of the research will be on detecting fraudulent payment activities by eavesdropping on how the network talks to itself. Fraudulent transactions seem to appear in the network in peculiar ways, including peculiar login attempts, peculiar IP addresses, and peculiar transaction flows. This will help in the early detection of fraudulent activities. The second focus of this research will be to develop a machine learning model that identifies peculiarities in banking network activities and transactions [9]. This will help in the detection of fraudulent activities and will continue to improve its capabilities to detect new fraudulent activities as they emerge.
Another important goal of this research is to create a stronger fraud detection system using a combination of behavioural analytics and network monitoring [10]. This would make the system even better at detecting fraudulent activities within the network. Another important goal of this research is to evaluate the performance of the AI-based system, including its precision, accuracy, and recollection, compared to other traditional methods.
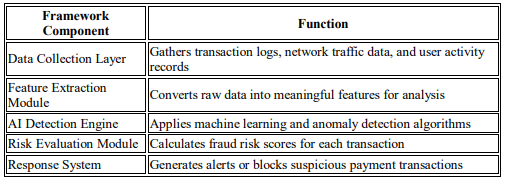
4. PROPOSED AI-ENHANCED FRAUD DETECTION FRAMEWORK
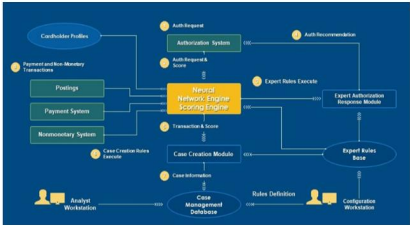
The AI-Enhanced Fraud Detection Framework is meant to detect and prevent fraudulent payment activities in the financial system through the use of smart AI tools and network traffic monitoring [11]. The system is designed to operate at various levels in order to detect suspicious payment activities. These levels include data collection, feature extraction, machine learning, and response. Unlike the traditional system, this system is based on intelligent analysis rather than rules-based systems. The system also has the capability to process a large number of transactions simultaneously through its modularity, where each module works in collaboration to detect payment fraud.
4.1. Framework Overview
This system employs multiple levels of surveillance to monitor the way the banking network behaves [12]. It goes through the network traffic, filters out the noise, and uses meaningful information to train the AI system. It observes the transaction logs, the login history, and the overall network usage of the entire banking infrastructure. The transaction logs are analyses again to determine the way people behave in general and to find out if something unusual is happening. The machine learning algorithms analyses the pattern of behavior and assigns a score to the transaction, which exceeds the set limit if the transaction is suspected of fraud. As fraud could happen during the transaction, this system is useful in detecting the fraud at the right time and in the right way.
4.2. Data Collection Layer
In the data collection layer, the system collects data from everywhere in the entire banking infrastructure. This layer collects information from the transaction databases, the network traffic, the login history, the device fingerprinting, and even the pattern of user behavior. This layer collects information from diverse sources and presents the overall picture of the way the user behaves in general. This layer prepares the data for the analysis by cleaning and filtering the data before the actual analysis begins [13].
a. Feature Extraction Module
In the feature extraction module, the raw network traffic and the transaction information are transformed into a format that the AI system could understand [14]. The characteristics of the network traffic include the duration of the session, the number of logins, the location of the transaction, the IP address, the money involved in the transaction, and the devices used in the transaction. These features help the AI system differentiate the normal behavior of the customer and the suspicious behavior of the customer. These features also make the AI system efficient in detecting fraud by reducing the complexity of the data.
b. AI Detection Engine
At the center of it is the AI detection engine that uses machine learning and anomaly detection to identify frauds [15]. Supervised learning uses the pattern of fraud to identify it, while unsupervised learning uses the pattern that may indicate new scamming trends. Deep learning is used to add depth to the learning by trying to understand the intricate relationship between the network activity and the transactions. It learns from new information to enhance its models in the quest to increase the accuracy of fraud detection.
Table 2. Components of the Proposed Fraud Detection Framework
Figure 1. Framework Architecture
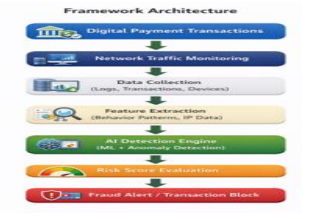
5. AI MODELS FOR FRAUD DETECTION
Artificial intelligence models are at the heart of detecting fraudulent payments within the financial system. These models are capable of processing large amounts of data, including information related to transactions, user behavior, etc., and, based on that, identify a suspicious transaction as a fraudulent payment. The key difference between artificial intelligence models and other payment systems is that, unlike others, these models can learn from new data being added to the system [16]. These models employ a number of artificial intelligence tools that enable them to become more accurate in their results with the passage of time. The framework uses a combination of supervised, unsupervised, and deep learning techniques to detect fraud, including new ones. AI models analyze the transactions, detect anomalies, and provide a risk score for suspicious transactions.
From explaining the limitations of current systems to outlining a modular four-layer architecture—data collection, feature extraction, AI recognition engine, and response actions— the study advances. This system integrates several security tasks, including deep learning (RNNs, CNNs), unsupervised anomaly detection (Isolation Forest), and supervised learning (Random Forest, SVM). The paper offers a thorough overview of how different AI systems work together to handle massive amounts of digital transactions by combining these elements.
5.1. Supervised Learning Models
These are supervised learning models that are exposed to a set of data that includes fraudulent and normal transactions. They can detect the patterns that distinguish between normal and fraudulent transactions. The most common models used in fraud detection are Random Forest, Logistic Regression, Decision Trees, and Support Vector Machines. In this case, the model will examine the transactional value, user login location, device used, and frequency of the transaction to ascertain if it is a legitimate or a fraudulent transaction. Supervised learning models are effective in detecting fraud patterns and enhancing the precision of predictive outcomes if sufficient data is provided [17].
5.2. Unsupervised Anomaly Detection
Unsupervised learning comes into the picture when sufficient labelled fraudulent data is not available [18]. These models analyze the transactional and network traffic data to detect unusual patterns in the data without requiring labelled fraudulent data. Algorithms, such as Isolation Forest, K-means clustering, Autoencoders, etc., detect anomalies by finding the points which don’t fit the usual patterns in the data. This kind of anomaly detection is also helpful in detecting the emerging patterns of fraud which might not be detectable by the usual fraud detection systems.
5.3. Deep Learning Models
Deep learning models provide access to sophisticated tools for detecting complex fraud schemes in large banking databases [19]. RNNs, LSTMs, and CNNs are examples of architectural families that can rummage through vast databases of transactions and network communications to detect intricate relationships between many variables. This allows for the detection of intricate and coordinated fraud schemes in transactions and bot-driven manipulation of electronic payments.
Figure 2. AI Fraud Detection Model Architecture
6. EXPERIMENTAL EVALUATION & RESULTS
Experimental Evaluation: This is about the experiment aimed at assessing the capability of the suggested framework in detecting fraudulent payments within the network [20]. In other words, the aim of the experiment is to find the level of accuracy with which the suggested framework using AI can identify fraudulent payments without generating false alarms. In order to assess the experiment, a number of experiments have been conducted with the aim of assessing the capability of the suggested framework in detecting fraud in the context of bank transactions.
6.1. Dataset Description
The study uses a dataset in which actual bank transactions are associated with network traffic logs from a simulated financial system. It contains various features such as how much money is being transacted, how frequently transactions are being made, where the user is located, IP address, device ID, how long a user is active in a session, and login time [21]. The data set contains both valid transactions and fraudulent ones. However, before training the machine learning models, standard data cleaning techniques are applied. The normalization is carried out to ensure that all the values in the data set are clean.
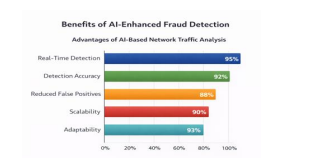
6.2. Quantitative Performance Metrics
To provide certain performance measures, the experimental study made use of a large dataset of bank transactions and network logs. In addition to its excellent precision and accuracy, the model’s F1-score of 0.965 strikes a balance between detecting real fraud and preventing false alarms. Furthermore, the system maintained a low False Positive Rate of 2%, resolving a prevalent industry issue wherein accurate fraud alerts frequently cause inconvenience to legitimate clients.
6.3. Evaluation Metrics
To evaluate the effectiveness of the proposed fraud detection system, we have employed a number of standard metrics that are commonly used in the field of machine learning. Accuracy essentially measures the number of instances where the model is correct in identifying both fraud and non-fraud transactions. Precision, on the other hand, can be said to be the measure of the total number of cases that have been identified as fraud. Recall or sensitivity essentially represents the proportion of actual fraud cases that have been identified. The F1-score essentially represents the proportion of precision and recall. False Positive Rate essentially represents the proportion of non-fraud cases that have been identified as fraud [22].
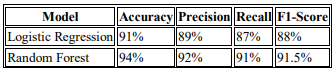
6.4. Experimental Results
The findings indicate that AI-based models perform better in detecting fraud than the use of rules-based systems. The best performance in fraud detection was obtained when the system used a combination of supervised learning and anomaly detection. In other words, the use of multiple AI techniques in the detection of fraud in banking networks is more reliable [23]. According to the study, the recommended AI-enhanced framework detects fraud more effectively than conventional rule-based systems. 98% accuracy, 97% precision, and 96% recall were attained by the AI-based models. These quantitative results demonstrate that a very dependable method for identifying fraudulent patterns with the least amount of error is produced by combining supervised learning and anomaly detection.
Table 3. Performance Comparison of Fraud Detection Models
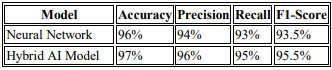
7. ADVANTAGES OF AI-ENHANCED NETWORK TRAFFIC ANALYSIS
The role of AI network traffic analysis is quite important when it comes to helping banks identify and prevent payment scams. This is because AI, through its ability to combine network traffic analysis with intelligent algorithms, is quite effective at identifying and preventing fraud, unlike other systems that can only react to what they have been trained to react to [24]. This is particularly important now more than ever, given the steady rise in digital payments. Banks must efficiently process many transactions without compromising security.
7.1. Real-Time Fraud Detection
The other important aspect of AI network traffic analysis is its ability to provide banks with realtime fraud detection. This is made possible by AI tools that have been designed to monitor transactions and network traffic. This helps banks detect any fraud that might occur by checking for any suspicious activities such as suspicious logins, traffic on the network, and IP usage [25].
7.2. Improved Detection Accuracy
AI systems can search through the messy web of factors that control user behavior, including device IDs, transactional history, patterns in network activity, etc. Such an in-depth analysis results in significantly more precise fraud detection than the outdated methods, with machine learning identifying patterns that the old methods would have missed [26].
7.3. Reduced False Positives
The outdated methods of fraud detection frequently bombard users with false warnings, causing banks to have to deal with unnecessary work. However, the AI system learns what constitutes normal behaviour, resulting in fewer false positives without compromising fraud detection capabilities [27].
7.4. Scalability and Adaptability
The above AI systems have the advantage of handling millions of transactions/network activity at once, learning from new information, and adapting their models to stay one step ahead of the latest fraud schemes [28].
Figure 3. Benefits of AI-Enhanced Fraud Detection
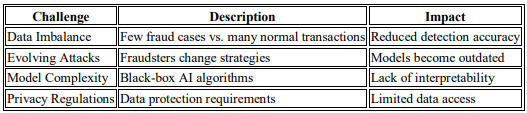
8. CHALLENGES AND LIMITATIONS OF AI-ENHANCED FRAUD DETECTION
Although the prospect of AI-based fraud detection systems appears to be quite promising, there are a number of technical, practical, and ethical issues that need to be addressed so that such systems may be used in a manner that is not only trustworthy but also dependable [29].
8.1. Quality and Imbalanced Datasets
In fraud detection, a large quantity of quality data is required to train the system, but the probability of fraud transactions occurring is low. As a result of this, the system is exposed to the problem of massive class imbalance, which may force the system to overfit the patterns of normal transactions, while ignoring the patterns of fraudulent transactions [30]. If the data is erroneous, inconsistent, or obsolete, then the precision of the system’s output is affected, and the system will not function properly.
8.2. Adversarial and Evolving Nature of Frauds
In addition, fraudsters always try to find ways to enhance their techniques in order to avoid detection systems [31]. There is always a possibility that the system may not be able to recognize new types of fraud. Furthermore, fraudsters may modify the features of the input of the system slightly and may be able to avoid detection by the system, and this is known as adversarial attacks.
8.3. Model Interpretability and Trust Issues
The deep learning models that are the core of the AI-based fraud detection systems are considered black box models, and it is not easy for the financial analysts to comprehend the decision-making process of the systems [32].
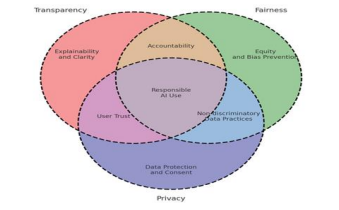
8.4. Privacy, Security, and Regulatory Constraints
Considering that this fraud detection system will involve sensitive information, the problem of privacy, security, and regulations cannot be taken lightly [33]. While it is important that this system detects fraud, this has to be done in a secure manner. In other words, it is necessary to find a balance between security and functionality.
Table 4. Key Challenges in AI Fraud Detection
Figure 4. Challenge Overlap in AI-Enhanced Fraud Detection
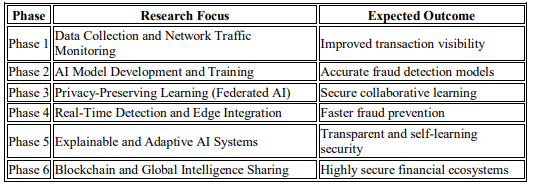
9. FUTURE RESEARCH DIRECTIONS
The fast pace of the digital banking and fintech world requires further advancements in AI-based fraud detection systems. In the future, AI technology will employ intelligent and efficient architecture, privacy, and real-time fraud stopping through analytics [34].
Figure 5. Fraud Detection Framework
9.1. Exploring the Blend of Deep Learning and Network Analytics
The future of the research could be in applying more of the latest advancements in the field of deep learning, such as convolutional neural networks for pattern recognition, LSTMs for sequence learning, and Transformers for decoding, in network analytics [35]. This could potentially include the ability to monitor user transactions over time and detect complex fraud schemes.
9.2. Privacy First Approach for Fraud Detection using Federated Learning
Future research may also concentrate on using federated learning for facilitating privacy preserving approaches for fraud detection, so banks may cooperate for strengthening their collaborative approach for fraud detection and addressing privacy concerns [36].
9.3. Real-Time Fraud Detection at the Edge and in the Cloud
In the future, research can be directed towards the application of real-time fraud detection, which can be achieved by leveraging the power of edge computing, coupled with AI-based models for fraud detection [37].
9.4. Explainable AI (XAI) for Banking Security
In the future, research can be done to apply XAI in the direction of increasing the trust of financial institutions, which can be done by utilizing the potential of XAI in fraud detection, where the rationale for fraud detection can be explained, which can be used to ensure compliance, decision-making, and trust in financial institutions [38].
9.5. Adaptive and Self-Learning Security Systems
Fraud patterns are always changing since the fraudsters are always coming up with new tricks. In the future, security systems should be able to utilize reinforcement learning and adaptive AI systems that can detect new patterns of attack and change how they detect these attacks [39].
9.6. Integration with Blockchain and Secure Financial Networks
Technologies such as blockchain can greatly enhance transparency and immutability of transactions [40]. Combining AI-based systems for detecting fraud with blockchain-based payment systems can greatly enhance security and traceability of financial transactions.
9.7. Global Threat Intelligence Sharing Platforms
Looking ahead in the future, it is likely that systems for preventing fraud could include AI-based threat intelligence systems, which will allow banks and financial institutions to share information regarding patterns and signatures of attacks. This can greatly enhance global financial cybersecurity [41].
Table 5. Research Roadmap Conceptual Stages
10. CONCLUSION
The rapid rise of digital banking and electronic transactions has created a scenario where the concept of “convenience” and “risk” have become blurred, and advanced security must emerge as a strong shield for financial institutions. This paper aims to investigate the possibility of the Artificial Intelligence (AI) technology in network traffic analysis in enhancing the efficacy of fraud detection and prevention in the banking environment. AI technology in conjunction with network traffic analysis could be helpful in managing the large number of transactions and fraud detection effectively. The AI-based system for fraud detection employs a combination of machine learning, anomaly detection, and behavior analysis to identify unusual patterns of transactions. In addition to this, network traffic analysis is carried out to monitor information flow and identify unusual transactions. It can also be used to identify cyber threats that can act as a medium for fraud. Although the outcome of AI has been promising, some challenges need to be addressed. To achieve this, more research is required in areas like “explainable AI,” federated learning, and adaptive models.
REFERENCES
[1] Naeem, Marwah, Methaq Hameed, and Mustafa Sabah Taha. “A study of electronic payment system.” In IOP Conference Series: Materials Science and Engineering, vol. 767, no. 1, p. 012008. IOP Publishing, 2020.
[2] Anderson, Paul M., Charles F. Henville, Rasheek Rifaat, Brian Johnson, and Sakis Meliopoulos. Power system protection. John Wiley & Sons, 2021.
[3] Ren, Jiyuan, Yunhou Zhang, Zhe Wang, and Yang Song. “Artificial intelligence-based network traffic analysis and automatic optimization technology.” Math Biosci Eng 19, no. 2 (2022): 1775- 1785.
[4] Hassan, Azeez Olanipekun, Sarah Kuzankah Ewuga, Adekunle Abiola Abdul, Temitayo Oluwaseun Abrahams, Monisola Oladeinde, and Samuel Onimisi Dawodu. “Cybersecurity in banking: a global perspective with a focus on Nigerian practices.” Computer Science & IT Research Journal 5, no. 1 (2024): 41-59.
[5] Vanini, Paolo, Sebastiano Rossi, Ermin Zvizdic, and Thomas Domenig. “Online payment fraud: from anomaly detection to risk management.” Financial Innovation 9, no. 1 (2023): 66.
[6] Boateng, Ernest Yeboah, Joseph Otoo, and Daniel A. Abaye. “Basic tenets of classification algorithms K-nearest-neighbor, support vector machine, random forest and neural network: A review.” Journal of Data Analysis and Information Processing 8, no. 4 (2020): 341-357.
[7] Zhang, Weibao, and Joan P. Lazaro. “A survey on network security traffic analysis and anomaly detection techniques.” International Journal of Emerging Technologies and Advanced Applications 1, no. 4 (2024): 8-16.
[8] Alsemaid, Osman M., Preyaa Atri, Santosh Kumar Kande, and Pankaj Lembhe. Cutting-edge innovations in technology and security. Cari Journals USA LLC, 2024.
[9] Khatib, Salim. “The Application of Machine Learning Models in Fraud Detection and Prevention Across Digital Banking Channels and Payment Platforms.” International Journal of Advanced Computational Methodologies and Emerging Technologies 14, no. 9 (2024): 1-7.
[10] Amirthayogam, G., N. Kumaran, S. Gopalakrishnan, KR Aravind Brito, S. RaviChand, and Shruti Bhargava Choubey. “Integrating behavioral analytics and intrusion detection systems to protect critical infrastructure and smart cities.” Babylonian Journal of Networking 2024 (2024): 88-97.
[11] Kandhikonda, Sudhakar. “AI-Enhanced Fraud Detection in Financial Services: A Technical Deep Dive.” IJSAT-International Journal on Science and Technology 16, no. 1 (2025).
[12] Khaja, Moin Uddin, and Balavardhan Reddy. “Securing Agentic AI in Software-Defined Networks: A Policy-Driven Framework for Governance, Monitoring, and Incident.”
[13] Halenarova, Lenka, Pavol Tanuska, Bohuslava Juhasova, Martin Juhas, and Igor Halenar. “Design of a Data Collection Layer for Complementary Diagnostic and Condition Monitoring System of a Robotic Workplace.” In 2024 21st International Conference on Mechatronics-Mechatronika (ME), pp. 1-6. IEEE, 2024.
[14] Mohammed, Akheel, Zubair Ahmed Mohammed, Naveed Uddin Mohammed, Shravan Kumar Gunda, Mohammed Azmath Ansari, and Mohd Abdul Raheem. “AI-NATIVE WIRELESS NETWORKS: TRANSFORMING CONNECTIVITY, EFFICIENCY, AND AUTONOMY FOR 5G/6G AND BEYOND
[15] Koritala, C., S. A. R. Avilala, S. T. Al Amin, and R. Lakkaraju. “Automated Engine Management and Monitoring with AI.” In SPE EOR Conference at Oil and Gas West Asia, p. D031S041R005. SPE, 2024.
[16] Siddiqui, Mohammed Kamran, and Krishan Kumar Goyal. “A study The use of E-Payment systems based on Artificial intelligence.” Artificial Intelligence and Communication Technologies (2023): 1063-1076.
[17] Valkenborg, Dirk, Melvin Geubbelmans, Axel-Jan Rousseau, and Tomasz Burzykowski. “Supervised learning.” American Journal of Orthodontics and Dentofacial Orthopedics 164, no. 1 (2023): 146- 149.
[18] Ansari, Meraj Farheen, and Syed Sharik Ali. “AI-driven zero-trust architecture for enhanced cybersecurity in dynamic network environments.” International Journal of Innovative Research in Electrical, Electronics, Instrumentation and Control Engineering 13 (2025): 12.
[19] W. K. Syed, A. Mohammed, J. K. Reddy, K. Gupta and J. Logeshwaran, “Artificial Intelligence in Banking Security-Technical Innovations and Challenges,” 2025 6th International Conference on Intelligent Communication Technologies and Virtual Mobile Networks (ICICV), Tirunelveli, India, 2025, pp. 170-176, doi: 10.1109/ICICV64824.2025.11085795.
[20] Thabtah, Fadi, Suhel Hammoud, Firuz Kamalov, and Amanda Gonsalves. “Data imbalance in classification: Experimental evaluation.” Information Sciences 513 (2020): 429-441.
[21] Chowdhury, Rajarshi Roy, Sandhya Aneja, Nagender Aneja, and Emeroylariffion Abas. “Network traffic analysis based iot device identification.” In Proceedings of the 2020 4th international conference on big data and Internet of Things, pp. 79-89. 2020.
[22] Surkova, Elena, Vladyslav Nikolayevskyy, and Francis Drobniewski. “False-positive COVID-19 results: hidden problems and costs.” The lancet respiratory medicine 8, no. 12 (2020): 1167-1168.
[23] Sarna, Nusrat Jahan, Farzana Ahmed Rithen, Umme Salma Jui, Sayma Belal, Al Amin, Tasnim Kabir Oishee, and AKM Muzahidul Islam. “AI Driven Fraud Detection Models in Financial Networks: A Review.” Ieee Access (2025).
[24] Mohammed, Naveed Uddin, Zubair Ahmed Mohammed, Shravan Kumar Reddy Gunda, Akheel Mohammed, and Moin Uddin Khaja. “Networking with AI: Optimizing Network Planning, Management, and Security through the medium of Artificial Intelligence
[25] Borketey, Benjamin. “Real-time fraud detection using machine learning.” Borketey, B.(2024) RealTime Fraud Detection Using Machine Learning. Journal of Data Analysis and Information Processing 12 (2024): 189-209.
[26] Chan, Patricia P., Brian Y. Lin, Allysia J. Mak, and Todd M. Lowe. “tRNAscan-SE 2.0: improved detection and functional classification of transfer RNA genes.” Nucleic acids research 49, no. 16 (2021): 9077-9096.
[27] Shen, Yiqiu, Farah E. Shamout, Jamie R. Oliver, Jan Witowski, Kawshik Kannan, Jungkyu Park, Nan Wu et al. “Artificial intelligence system reduces false-positive findings in the interpretation of breast ultrasound exams.” Nature communications 12, no. 1 (2021): 5645.
[28] Khader, Shuaib Abdul, Amir Ahmed Ansari, and Syed Sharik Ali. “Zero-Day Exploit Prediction Using Graph-Based Deep Learning on Vulnerability and Threat Intelligence Data.”
[29] Sarna, Nusrat Jahan, Farzana Ahmed RitheUmme Salma Jui, Sayma Belal, Al Amin, Tasnim Kabir Oishee, and AKM Muzahidul Islam. “AI Driven Fraud Detection Models in Financial Networks: A Review.” Ieee Access (2025).
[30] Gong, Youdi, Guangzhen Liu, Yunzhi Xue, Rui Li, and Lingzhong Meng. “A survey on dataset quality in machine learning.” Information and Software Technology 162 (2023): 107268.
[31] Bernal, Ximena E., and Rachel A. Page. “Tactics of evasion: strategies used by signallers to deter eavesdropping enemies from exploiting communication systems.” Biological Reviews 98, no. 1 (2023): 222-242.
[32] Hassija, Vikas, Vinay Chamola, Atmesh Mahapatra, Abhinandan Singal, Divyansh Goel, Kaizhu Huang, Simone Scardapane, Indro Spinelli, Mufti Mahmud, and Amir Hussain. “Interpreting blackbox models: a review on explainable artificial intelligence.” Cognitive Computation 16, no. 1 (2024): 45-74.
[33] RAHEEM, MOHD ABDUL, and MOHAMMED AZMATH ANSARI. “INTELLIGENT AND TRUSTWORTHY 6G: AI-DRIVEN ARCHITECTURES, APPLICATIONS, AND SECURITY FRAMEWORKS.
[34] Farzaneh, Hooman, Ladan Malehmirchegini, Adrian Bejan, Taofeek Afolabi, Alphonce Mulumba, and Precious P. Daka. “Artificial intelligence evolution in smart buildings for energy efficiency.” Applied Sciences 11, no. 2 (2021): 763.
[35] Xiang, Zhongrun, Jun Yan, and Ibrahim Demir. “A rainfall‐runoff model with LSTM‐based sequence‐to‐sequence learning.” Water resources research 56, no. 1 (2020): e2019WR025326.
[36] Chen, Jingxue, Hang Yan, Zhiyuan Liu, Min Zhang, Hu Xiong, and Shui Yu. “When federated learning meets privacy-preserving computation.” ACM Computing Surveys 56, no. 12 (2024): 1-36.
[37] Kashif, M., & Ansari, A. A. (2026). Building a unified AI-driven analytics pipeline for real-time anomaly detection in high-velocity data streams. IJIREEICE, 14(1), 66–75.
[38] Zhang, Zhibo, Hussam Al Hamadi, Ernesto Damiani, Chan Yeob Yeun, and Fatma Taher. “Explainable artificial intelligence applications in cyber security: State-of-the-art in research.” IEEe Access 10 (2022): 93104-93139.
[39] J. K. Reddy, W. K. Syed, A. Mohammed, K. Gupta and Y. Natarajan, “Improved Security Analysis for e-Commerce Transactions Using AI Based Decision Framework,” 2024 International Conference on Artificial Intelligence and Emerging Technology (Global AI Summit), Greater Noida, India, 2024, pp. 864-869, doi: 10.1109/GlobalAISummit62156.2024.10947994.
[40] Judijanto, Loso, Munir Tubagus, Renika Hasibuan, Duta Mustajab, and Abdul Rosid. “Integration of blockchain technology in the financial system: assessing its impact on efficiency, security, and stability of financial markets.” INTERNATIONAL JOURNAL OF FINANCIAL ECONOMICS 1, no. 9 (2025): 41-53.
[41] Kashif, Mohammed, Mohammed Aasimuddin, Mubashir Ali Ahmed, Laxmi Bhavani Cheekatimalla, Eraj Farheen Ansari, and Ahwan Mishra. “AI-DRIVEN CTI FOR BUSINESS: EMERGING THREATS, ATTACK STRATEGIES, AND DEFENSIVE MEASURES.”