IJCNC 08
AN EFFICIENT MACHINE LEARNING OPTIMIZATION MODEL FOR ROUTE ESTABLISHMENT MECHANISM IN IOT ENVIRONMENT
Kishore Golla1 and S. PallamSetty2
1Research Scholar, Dept. of CSE, Andhra University, Visakhapatnam, Andhra Pradesh, India
2Dept. of CSE, Andhra University, Visakhapatnam, Andhra Pradesh, India
ABSTRACT
Internet of Things (IoT) provides interconnection of various wireless communication devices, which offers both ubiquitous accessibility of devices and in-built intelligence capacity. IoT offers interaction with devices and provides sufficient capability advantages of networking and socialization with consideration of intermediate devices. RPL (Routing Protocol for low-power and Lossy Networks) is an attractive model for effective routing techniques in the wireless medium. The increase in demand for wireless systems in terms of energy, reliability, stability, and scale routing IPv6 over 6L0WPAN is being adopted. This research developed an optimized machine learning model (WOABC) routing protocol for route establishment in IoT networks. The constructed RPL routing protocol incorporates an optimization approach for the identification of the best and worst routes in the network. The proposed WOABC evaluates the routing path for data transmission between nodes through optimization techniques for effective route establishment. The optimization of routes is performed with whale optimization techniques. The developed whale optimization technique is incorporated in machine learning networks. Also, the proposed WOABC utilizes an optimization membership function for the identification of the optimal path in the network. The performance of the proposed WOABC is compared with existing techniques such as RPL and Speed – IoT. The comparative analysis showed that the performance of the proposed WOABC is ~3% increased throughput. The performance of the proposed WOABC is significant compared with the existing RPL routing protocol.
KEYWORDS
RPL, Optimization, Route establishment, Optimization, Whale Optimization
1. INTRODUCTION
In recent years, Wireless Sensor communication and the Internet of Things (IoT) have shown tremendous growth and development. As IoT have been active leverages in the Internet part of everyday life [1]. The evaluation of technological advancement is subjected to certain features and significant applications to improve the functionality of the network. The efficient system design needs to concentrate on certain system-specific applications [2]. In a wireless network environment, IPv6 exhibits an attractive model due to its significant configuration in terms of mobility, address space, capabilities, and security. The several objects are interconnected based on the single unit order performance characteristics. The IPv6 network characteristics are based on translation, end-to-end encryption, scalability, and neighbour discovery for the construction of anIoT based network [3]. Within IoT networks, different devices are embedded for processing resources, power consumption, and minimal memory utilization. Generally, those networks are referred to as Low Power and Lossy Network (LLNs). However, those applications are not effective for certain instances, such as Transmission Control Protocol (TCP) and HTTP (HyperText Transfer Protocol) based applications [4 – 6]. Traditionally, those LLNs are described based on the estimation of network outage links, data loss, path loss, multipath interference, channel fading, and so on [7–8]. The development of the IoT network is enabled with LLNs through viable domains based on consideration of experiments to achieve an efficient solution. However, the network LLNs are based on the consideration of RPL routing for the momentum of desired data communication without any characteristics of mobility environment [9].
The characteristics of LLN are based on the power-constrained nodes and border routers concerning gateways. In this scenario, there is no communication between nodes and the router, with border router data transmission is performed with intermediate nodes [10 – 12]. Those network characteristics are maintained with network routing protocol design. In this scenario, the routing protocol is considered a crucial factor as it is actively involved in information transmission from one to another router in an IoT network. Based on this, Internet Engineering Task Force (IETF) established a routing protocol design for IoT networks defined as RPL routing [13]. It enables users to adopt the desired routing mechanism as developed in existing literature with the provision of minimal threshold weights with the implementation of a spanningtree between each node and a single path established between paths. Through data overloading of nodes energy is inefficient for LLNs and power reduction is estimated quickly. To overcome the challenges of the network multipath routing scheme is considered a promising tool for efficient route recovery and reliability of packet replication in the identification of optimal path [14 & 15]. With the implementation of Directed self-assembly (DSA), the unlicensed spectrum of IoT devices is opportunistically involved in the utilization of unused channels for the licensed spectrum of primary users (PU). In a recent scenario, the solution obtained from DSA is based on proposed and pursued demand in the network for applications such as commercial network [2], Vehicular Ad-hoc Network (VANET), smart grid, and smart communications [5]. The availability of spectrum is based on consideration of space and variance of time for the election of the best available channels in the given IoT pair. This is achieved using Device-to-Device communications (D2D) [6 & 7], where the route for data for transmission is using multiple hops. With the incorporation of a multi-hop routing environment quality of service (QoS) of the network needs to be estimated based on consideration of end-to-end route in the network for estimation of the best channel for each hop.
In the conventional IoT environment, multi-hop D2D is considered as the primary challenge in the environment for DSA based dedicated spectrum utilization characteristics those are: a) utilization of spatial-temporal a=spectrum awareness scheme for identification of unused or underused channels based on consideration of route location with the estimation of the end-to-end route, b) protection of the primary transmission of the licensed channel due to interference secondary IoT communication, and c) ensured power control IoT communication medium for maintenance of efficient energy preservation scheme of IoT devices. Based on this, several routing protocols are constructed those are LSR [8], and OSPF [9]. Additionally, the conventional traditional routing protocols are derived those are DSR and RPL which are effectively applied in DSA based IoT communications.
The conventional cognitive radio [10] comprises of DSA network those couples the devices for sensing and performance of availability of optimized local spectrum. Those techniques are effective for device-level spectrum based on the incorporation of techniques that are considered with time and power overhead of the constrained IoT environment. As an effective communication medium, the Federal communications commission (FCC) constructed a dedicated spectrum sensor for Environmental Sensing Capability (ESC) to detect the presence of primary and secondary access in IoT [11 & 12]. The advancement of the ESC-driven environment is based on estimation of ideal spectrum reference for estimation of accurate and visualization of up-to-date spectrum availability of IoT with geographical region [13 – 16]. With multi-channel routing scheme is based on spectrum map aided multi-channel for IoT communication in terms of a) identification of end-to-end routes through the estimation of hops and identification of best channel with hopping and b) suggested optimization-based transmission power is based on consideration of each hop to safeguard incumbents for deriving energy efficiency of the network.
This paper developed an optimization-based machine learning algorithm for route establishment in an IoT environment. The developed algorithm involved in the construction of whale optimization algorithm for classification of optimal path those estimated through optimization of the path in the network. The constructed network performance is evaluated based on the consideration of the optimal path in the network. The performance characteristics of the proposed WOABC are computed based on the evaluation of the routing path in the network. Simulation analysis stated that the proposed WOABC is comparatively examined based on the estimation of network parameters. The proposed algorithm is categorized as follows: section II presented a related work associated with IoT network followed by the performance of proposed WOABC in section III. In section, IV presented optimization algorithm performance is presented. In section V routing establishment between nodes is presented for IoT and in section VI simulation results are presented. Finally, in section VII overall conclusion obtained from the analysis is presented along with future enhancement.
2. RELATED WORKS
In recent years, RPL exhibits effective performance integrated with IPv6 Routing protocol for IoT environment. The major concepts in these days are optimal path finding, security and mobility management [17-20]. In [21&22] proposed a geographical-based RPL routing scheme for IoT networks to minimize the number of transmission links. Also, it is observed that developed geographical RPL routing effectively minimizes the number of multicast paths. In [23 & 24] constructed an IoT network with multicast and multi-path routing for multimedia and fault tolerance communication. In [28] proposed a comprehensive framework for channel assignment and efficient routing scheme for multi-hop scenario for IoT network. In those works, Primary Users (PU) is provided with minimal channel value rather than statistically designed secondary channels. In [26] constructed an efficient spectrum sharing technique for secondary networks. The constructed spectrum sharing integrates Mixed Integer Non – Linear Programming (MINLP) with the formulation of the objective function with spectrum reuse factor to improve the throughput of the network. In [25] developed a graph structure-based network topology for network route selection with a single transceiver IoT network. In [27] constructed an RPL routing protocol for the distributed environment for routing, scheduling, and power control.
In [30] developed a metric-based RPL secondary network for minimization of switching delay exists between a band of frequencies and back-off delay. In [35] constructed a Spectrum Aware Mesh Routing (SAMER) for effective utilization of long- and short-term utilization of spectrum. The developed SAMER utilizes available spectrum blocks effectively utilization of available spectrum without elimination of spectral conditions. In [29] constructed a link stability model for the establishment of route connectivity through Laplacian spectrum model-based graphs. In [32-34] presented a stable route-oriented routing protocol for route maintenance at an acceptable cost. In [31] designed a SEARCH RPL routing protocol for geographical IoT networks based on forwarding principles. At present, spectrum-aware IoT networks are evolved for numerous wireless applications. Among those, IoT that utilizes an unlicensed spectrum is notable. In [38] constructed a learning-based spectrum algorithm for IoT network for maximizing the throughput of the network. In [39] presented an FM spectrum for IoT-enabled low-power short-range communication environment. Through evaluation of existing works, it is identified that IoT network with D2D communication provides a significant delivery scheme based on DSA for the management of IoT. However, existing techniques are primarily optimal path schemes and decrease the overall secondary channel bandwidth.
3. WOABC ROUTING PROTOCOL IN RPL
RPL routing protocol is best among the reactive routing protocols and it is adaptable for several conditions such as small memory-based network, dynamic conditions, network utilization. Also, it supports the Low power Lossy Networks (LLNs) is a better way to communicate unicast routes to the destination which is better than other reactive routing protocols in terms of end-to-end delay, network throughput, message success rate, and network overhead. In general, on the demand condition, the RPL protocol will start working with the routing algorithm. That activation of the routing algorithm is processed using two phases, which are route discovery and control phase. In the control phase during the process of communication between the source and the destination routes are created. Secondly in the route discovery phase, a new route selection process is done after neglecting the link failures. The core concept of the RPL protocol is discussed below.
- At the initial condition, the Hello Message is transmitted by all the nodes to understand the neighbor details.
- Then RREQ message is transmitted to the source node is got the details about the path and the destination. By using the help of the hop nodes, the message will reach the destination. Randomly in all the paths, the messages are transmitted. Maximum the paths with a smaller number of hop nodes are finalized as the best path for data transmission.
- After receiving the route request message, the destination will acknowledge the RREP message to the source node.
- There is also a possibility for link failure during this message transmission period. That time ERR message is notified to the other nodes in the path. After verifying zero error in the path the routing path is selected.
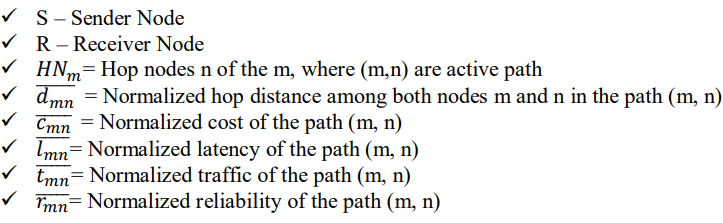
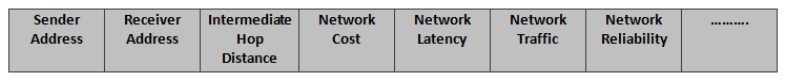
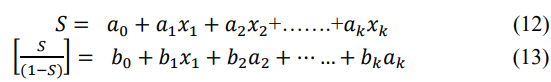
To increase the performance of the RPL protocol in terms of cost, distance, traffic, latency, and network reliability multi-objective function is added to the RPL protocol which leads to the creation of the WOABC (Multi-Objective RPL) routing model. Commonly, the RPL protocol calculates the hop count to select the routing path. This is the best way to find the path and also to provide higher bandwidth with low message drop. Some other parameters are also needed to get considered to develop networks which are sensor node energy, link reliability, and trustworthy routing. Moreover, we have to concentrate on minimizing routing overhead as well as route maintenance. To execute multiple routing in routing protocol WOABC protocol has been developed. The Variables used in this protocol for analysis are given below.
3.1.1. WOABC Packet Formatting
As mentioned earlier in the RPL protocol, the hello packets are broadcasted from the sender to the entire nodes. Then the RREQ message is sent to all the nodes to analyze the path. All these processes are updated in the routing table. The major information of the packet header to get transmitted is distance, cost, latency, traffic, and network reliability. After receiving the RREQ message the receiver node returns the RREP to the sender node via the selected shortest path. The RREQ and RREP are explained in the following Figure 1.
Figure 01. WOABC Packet Format
In WOABC protocol, the RREQ message is sent by the sender to all the nodes which are in the coverage area of the sender with a definite receiver node. Path P consists of an objective function 0. Initially, the RREQ is received by the neighbor node if that node is not the receiver node, then it is transmitted to the next node in the path. The intermediate nodes maintain the objective function which calculates the partial routes based on the next-hop node presented in the queue of the routing table. This process is used to analyze the topology changes as well as the best neighbor node selection and link failure detection. Immediately after receiving the RREQ message, the receiver node transmits the RREP message to the sender node after the creation of the routes.
4. OPTIMIZATION LOGIC METHOD
This research involved the estimation of the optimal path in the IoT network for the establishment of a route. This multipath optimization is involved in the estimation of multipath in the environment. The main part involved in whale optimization is based on encircling prey those are stated as follows:
Encircling prey
Whales are presented in the prey location and involved in the encircling capability of the IoT node. Due to the existence of search space in an unknown location-targeted prey is evaluated by the agent as stated in equations (1) and (2):
In the above equation (1), the present iteration is represented as 𝑡, coefficient of vector is denoted as 𝐶 and 𝐴⃗. Vector best position is represented as 𝑋⃗ 𝑏𝑒𝑠𝑡 and position vector is denoted as 𝑋 of ants.
The path of the network us defined as X involved in estimation of vector position. This vector can be measured using is presented in equations (3) and (4),
The parameter 𝑟⃗ represented the random vector of [0,1]. In the above equation a decrease linearly concerning iteration count. Based on this consideration exploration phase is evaluated.
4.1. Proposed Multi-Path Optimization (Probability Whale Optimization Approach)
The routing in IoT is involved in the estimation of an available path from the source to the destination node. The performance of network is based on consideration of the probability of nodes for the estimation of routing decision for estimation of the probabilistic value of the network and it is computed using the equation (5)
Upon the significant establishment of routes successful connection is denoted as 1 and no successful connection is represented as 0. The probability of transmitting each packet is stated as p. The estimation probability of node for routing is examined based on the information available within the spectrum of radio communication environment. The average path of the IoT communication is represented as in equation (6)
Where 2σ indicates the variance of IoT communication path and β − y provides the mean of data transmission in IoT communication. The effective path for communication of information in IoT network is estimated using equation (7),
In this number of nodes, the packet transmitted, and other factors are presented. The equation (7) is computed based on the node energy level with consideration of 𝜌 energy level, 𝑑 distance between nodes and 𝛾 denoted the hopping count in the network
4.2. Mathematical Derivation of Machine learning for optimal path
This paper developed a sigmoidal-based classification technique for improving optimal path in a system specifically for IoT networks. The proposed approach integrates both Adaboost and regression classifier for improving optimal path in IoT. Logistics regression is involved in the conversion of mismatched data into either 0’s or 1’s to improve the accuracy of the classifier. In the case of the AdaBoost scheme, it eliminates all unwanted data from the network. To withstand continuity in the network this research uses the sigmoidal approach for the elimination of limitations associated with the classifier. The general steps involved in the proposed sigmoidal AdaBoost regression classifier are presented as follows:
The proposed WOABC is based on the integration of machine learning algorithms and an optimization approach. To identify the effective routing path of the network proposed WOABC utilizes AdaBoost classifier with a regression model is presented. The developed model involved the estimation of weak path identification using weal learner. Through the training process, a strong classifier performs binary classification with the estimation of network parameters. With the implementation of the weak learner, AdaBoost improves the estimation of the optimal path in the network. The algorithm performance of WOABC is based on a decision tree with estimation at various levels. The estimation of the optimal path in the network is computed through the AdaBoost model presented in equation (8)
The developed WOABC involved the estimation of machine learning for multiclass performance for the estimation of the logistic function. The characteristics of network optimal path are network is computed as in equation (9)
This paper aimed to construct an effective route establishment in the IoT network with an RPL routing scheme. With the computation of AdaBoost classifier integrated with a regression model for estimation of the optimal path in the network those are presented in equation (10) as follows:
In equation (10), the term 𝑦 denoted the linear equation of the output variables, 𝑥 represented the input variable assigned and 𝜔 𝑇 was involved in the estimation of the weak classifiers in the model. The above equation provides the linear equation relationship between the estimated optimal path of the network. The estimated sigmoidal equation is computed in equation (11)
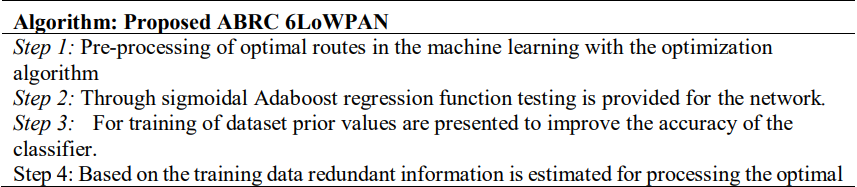
The network characteristics probability of network is computed through the equation (12) and (13)
The probability of variable is computed based on the taking log on both sides as stated in equation (14)
The exponential characteristics of the variable for estimation of the optimal path in the network is computed with equation (15)
The combination of equations (14) and (15) provides the equation of (16)
The optimal path estimation of the IoT route is developed using sigmoidal function estimation with a machine learning-based classifier. Using maximum likelihood estimation property the values are computed as in equation (17)
The application of the simplified form of equation as presented in equation (18)
The likelihood estimation of the equation variables are presented as in equation (19)
The estimation of negative values of the variables for estimation of the optimal path in the network is stated as in equation (20)
Based on the above equation, 𝑆 = (𝑎0 + 𝑎1𝑥1 + 𝑎2𝑥2 + ⋯ … + 𝑎𝑘𝑥𝑘) ∑ 𝑆𝑖
Hence, the final derivation for achieving optimal path in the IoT network is computed as in equation (21)
5. ROUTE ESTABLISHMENT WITH WOABC
In an IoT network, route assignment provides significant potential interference with the optimization of the route assigned for the sensor. Globally, the optimization-based approach is an effective tool for effective channel utilization. Based on this, we proposed a WOABC for route establishment in IoT devices. The developed WOABC incorporates an optimization approach for the estimation of the efficient path for data transmission in the network. The network uses CICIDS – 19 dataset for attack detection and classification.
5.1. Route maintenance
In an IoT environment, route maintenance is accomplished with a conventional wireless network approach. Within the environment, cache routing is adopted for the non-existence of temporal variation within the available channel. In the case of the SpEED-IoT environment, route maintenance is adopted with present spectrum utilization. Within IoT devices cache of routes are minimizes overhead and latency protection of data for sensing IoT devices that are guaranteed protection of data. In this, sensors are completely relying on the routing cache. In sensor, environment cache is connected using devices that are located in the edges based on consideration of domain. These routes are connected at the devices located on the edge for estimation of inter-domain routes also it contains inter-domain subset routes. The cache routes are negligible based on the mapping spectrum.
5.2. Mobility in RPL
Within 6LoWPAN and RPL integrated with IETF IPv6 protocol involved in the generation of routes between nodes. RPL is designed based on the consideration of stable topology of network for effective management of mobility and flow of traffic between node towards stationary gateway [36 & 37]. In the IoT environment idea is related to the consideration of different tools, protocols, hardware, OS, and interoperability of nodes to receive information from each node. In the case of fixed-mobile nodes interoperability between nodes need to be estimated [38]. Thus, conventional RPL or 6LoWPAN concentrated on the increase in delays, overheads, latency, and high packet loss. Within IoT network distributes mobility management is necessary for applications for the establishment of better connectivity of the network. To examine the reachability of nodes it is necessary to examine the characteristics of the network link. It is effectively involved in the estimation of reachability and properties of links in the network. Through the external process concerning time parent selection phase is estimated and computed [39]. The handoff process is based on the conversion of one point of connection to another. This involved the selection of preferred parents for the further communication process. The network characteristics are based on consideration of two types such as hard hand-off and soft hand-off strategies. In this scenario, the parent access point and mobile nodes are computed through the activation of a new network connection. In the case of a soft handoff, a strategy link is established between transmission of nodes and parent for construction of connection with deactivation scenario [40].
Table 1. Characteristics of RPL routing
5.3. Best Route Selection
In the routing mechanism, data packets need to be transmitted between mobile nodes to the root node as a router it is transmitted towards the mobile leaf node. The performance of the network is based on consideration of end-to-end delay in the network influenced by the selection of parents at hand-off time. The data transfer is between nodes is based on the least ranking of the access point for selected optimization of mobile nodes. In network mode, data packets are transmitted with minimal hopping of root nodes. In this scenario, data is transmitted for routers and leaf nodes in those mobile nodes need to be integrated for data of destination path with nearby access points. In the case of RPL routing, packets are routed through the solitary root of nodes. It involved in ease of utilization of random routers in the communication medium when those nodes are non-root. Those communications between the nodes are stated as P2P communication which enables routers for identification path through some routers based on reactive mechanism. The proposed WOABC routing approach involved a similar process for DAG message transmission.
The object packets information is based on the Directed Acyclic Graph (DAG) and dissemination of packet through trickle algorithms with the production of Destination Oriented Directed Acyclic Graph (DODAG) with arbitrary root to destination. The identification of the root or estimated random root towards the estimation of destination without affecting the handoff performance of the network is very important. This is based on consideration of attributes for complete routers for information with the estimation of destination. This involved in estimation and computation of neighbor node access points for effective analysis of information. A detailed explanation of the proposed WOABC is presented in the following section.
5.4. Route Establishment with WOABC
The constructed IoT network is estimated based on consideration of varying network scenarios such as small, medium, high, and very high. The establishment of a network is based on an adaption of memory, utilization of the network, and dynamic conditions of the network. Also, it involved in the estimation of unicast routes of data from source to destination based on LLNs with effective performance characteristics of the routing protocol to achieve characteristics performance of reduced overhead and delay. Additionally, it concentrated on the estimation of improving network performance through an increase in PDR and throughput. As a routing protocol, the routing process is based on consideration of on-demand and adopted in two phases such as control and discovery phases. In the first phase, the route for effective data transmission is created for data transmission between source to destination. In the second phase, it is estimated based on the threshold level with consideration of route or link failure, the establishment of the route for data transmission between nodes from source to destination. The message data utilized in the RPL routing protocol utilized for processing control packets those messages are Route Requests (RouteRQs), Route Replies (RouteRPs), and Route Errors (RouteERRs). Figure 2 presented the deployed IoT environment is illustrated. It defines the coverage range of 100 meters with the deployment of nodes. In the simulation platform, the established connection of the nodes is presented. Based on the created cluster nodes establish the connection between nodes.
Figure 02. Deployed IoT network
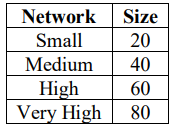
The deployment is based on consideration of small, medium, and high environments that adopt RPL routing. In table 2 presented the configuration of the network is illustrated.
Table 2. Network configuration
The RPL is routing for proposed WOABC is evaluated based on consideration of small, medium, high, and very high IoT environment as stated in table 2. The process of RPL routing process in the IoT environment is presented as follows:
i. Initially, for broadcasting of source node control packets are transmitted based on RouteRO.
ii. Upon reception of RouteRO, it transmits through the intermediate node and reaches the destination node.
iii. The complete fresh route is maintained in the optimal path based on the target with the estimation of the path.
iv. The transmission of RouteRP towards the destination node for transmission of a packet and reaches the source node with the determination of unicast node. Each node receives the RouteRO involved in the formation of a route. Based on unicast request RouteRP act and satisfies the requirement.
v. With an active router mechanism, the link status of nodes is monitored for the next hops. With the reception of RouteERRmessage transmitted between nodes with active routing detection. In this, the process trigger needs to be repeated with notification of RouteERR message for establishment of link status for hopping in the nodes for detection of network active route. Therefore, the network complexity needs to be minimized through the triggering process.
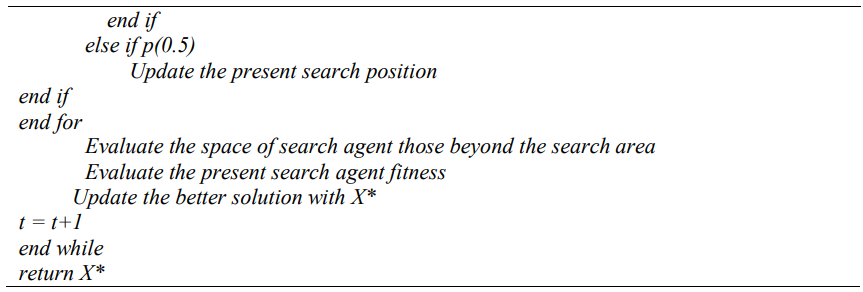
RPL routing process is effectively utilized in the effective solutions without modifying the delay, load, distance, cost, and reliability based on the consideration of routing metrics for effective decision making in the node using a multi-objective routing scheme. Conventionally, RPL protocol uses hopping count for selection of route and merge of routes in the network with provision of higher bandwidth with the limited dropping of data. It involved is based on the consideration of essential factors such as the energy of node and reliability for effective maintenance of routes. It involved effective maintenance of route and overhead of nodes. In this paper, we developed a WOABC routing protocol based on the routing of nodes with multiple routing techniques. In the algorithm, a, A, C, l, and p denoted angle of node, the position of nodes, hops, distance, and energy respectively. The algorithm involved in the construction of routes through WOABC is presented as follows:
6. SIMULATION AND ANALYSIS
6.1. Setup
The performance of the proposed WOABC is implemented using NS3 for the establishment of the route. Based on the proposed WOABC the performance is evaluated with existing SpEED – IoT and conventional RPL techniques. The performance of the proposed WOABC is comparatively evaluated with consideration of parameters such as Delivery Function (PDF), End to End Delay (E2E Delay), Network Power Consumption (NPC), and Network Energy Efficiency (NEE). In table 3 simulation setting for the proposed routing is presented.
Table 3. Simulation Setup
6.2. Parameters
The parameters are detailed as so to receive effective and trustworthy results for the proposed work. To find the results the process which is handled is collection, processing, and analyzing of the data to get the output of the separate mode or a group. The mathematical formula of those parameters is detailed below.
6.2.1. Packet Delivery Function
The packet delivery function is one among the network performance metric and is defined as the ratio between the number of the data packet sent and the number of the data packet received. The mathematical expression for packet delivery ratio is given in equation (22).
Where 𝑃𝑎𝑐𝑟𝑒𝑐𝑒𝑖𝑣𝑒𝑑 represents the number of packets received by the sink mode during the process of communication in the network and 𝑃𝑎𝑐𝑠𝑒𝑛𝑡 represents the whole packets generated by the sender modes.
6.2.2. End to End Delay of the Network
End-to-end delay is the essential parameter to calculate the network performance and to improve it. Hence it is referred to as the overall amount of difference between the delayed acceptance by the destination mode of each packet and the instant time when the data packet is transferred from the sensor mode. The mathematical representation for the evaluation of end-to-end delay is given in equation (23).
Where, 𝑇𝑟𝑒𝑐𝑒𝑖𝑣𝑒𝑑 represents the time taken for the sink to receive all the data sent by the source and the 𝑇𝑡𝑟𝑎𝑛𝑠𝑚𝑖𝑡𝑡𝑒𝑑 represents the time specified by the source node for the transmission of the data packets.
6.2.3. Network Energy Efficiency
The major parameter which is used to calculate the energy efficiency is the residual energy of the network. After the completion of the simulation, the energy consumption is calculated. In the network if consumed energy is minimal amount of residual energy is high which increases the overall network efficiency.
7. RESULTS AND DISCUSSION
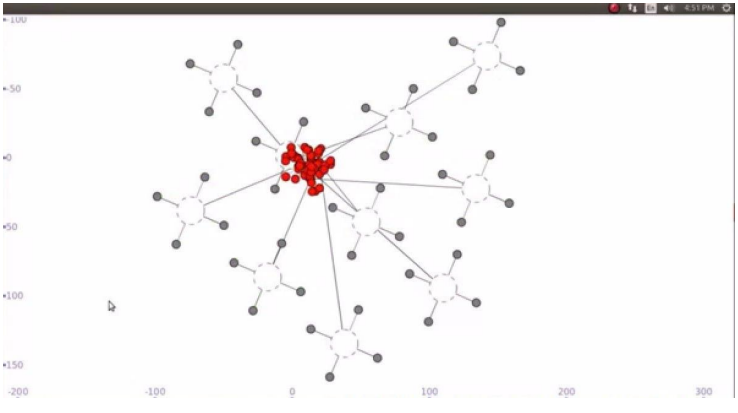
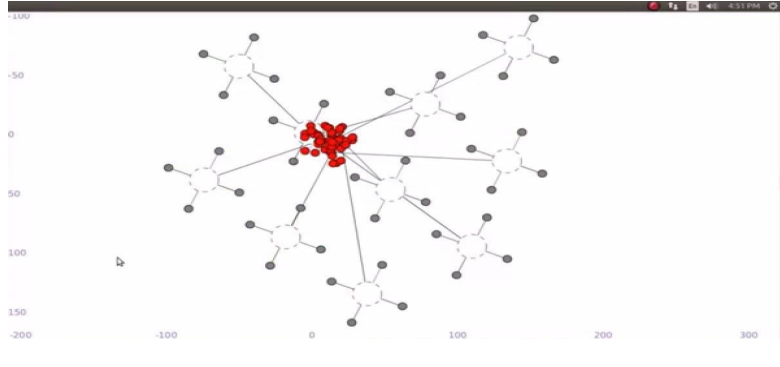
This section detailed the results and analysis of both the earlier methods and our research work which includes the analysis of packet delivery function, end to end delay, energy consumption, and energy efficiency. The PDF is the ratio between the numbers of packets received by the destination node to the number of packet sent by the sender mode. In figure 3illustrated the coverage is of the node through this optimization estimate the Expected Transmission Count (ETX) and Energy consumption level. The ETX defines the number of in-between nodes required for the transmission of information from source to destination.
Figure 03. Data Transmission Route
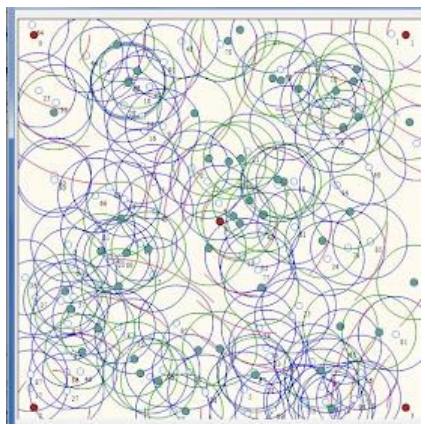
During the process, the ecological factors significantly affect the performance measurement due to unwanted events which leads to the ETX improper calculation that increases the packet loss in the network. Some other parameter that increases the packet loss is heavy traffic during the process of communication between the source and the destination. The established route in the IoT network is presented in figure 4.
Figure 04. Established Route in IoT
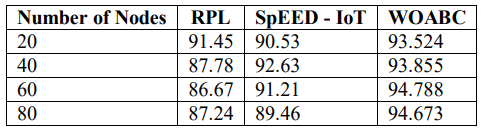
The performance of the proposed WOABC is comparatively examined with conventional RPL and SpEED – IoT. In table 4, the packet delivery function of the network is shown.
Table 4. Comparison of Packet delivery Function (%)
Figure 05. Comparison of PDF
The above figure 5represents the graphical comparison of the proposed model with the earlier works in terms of PDF where the x-axis represents the number of modes in the network and the y-axis represents the packet delivery function in percentage. The time interval taken for PDF calculation is 20, 40, 60, and 80 nodes. During the beginning of the simulation, the learning automata are mainly used to secure ETX from the environmental factor. This process greatly increases the PDF which leads to improving the overall QoS of the network as stated in table 5.
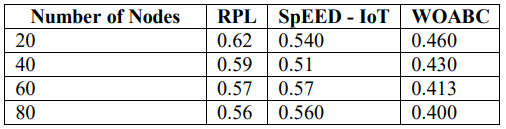
Table 5. Comparison of End – to End Delay (in sec)
The graphical representation of the E2E delay calculation is shown in Figure 6 where the x-axis represents the number of modes in the network and the y-axis represents the delay values. From these results, it’s understood that our proposed model produces great results in terms of PDF and E2E delay.
Figure 06. Comparison of End_to_End Delay
Network power consumption is defined as that energy utilized during the process of communication in the network. The graphical comparison of the proposed (WOABC) with (RPL) and (SpEED – IoT) is shown in Figure 7and the values are given in table 6. The network power consumption (NPC) is calculated in node sizes of 20, 40, 60, and 80. During the beginning of this process, the ecological system is observed using the learning automata to improve the performance of ETX. Currently, the network is ready to face the improbabilities in it. The process greatly helps to reduce the power consumption in the network compared with the earlier models. The other factor which reduces power consumption is reducing network overhead by neglecting the additional load during communication using whale optimization. From the graph and the value table, it’s proven that our proposed model plays well when compared with the earlier works.
Table 6. Comparison of Network Power Consumption (Mbit/J)
Figure 07. Comparison of NPC
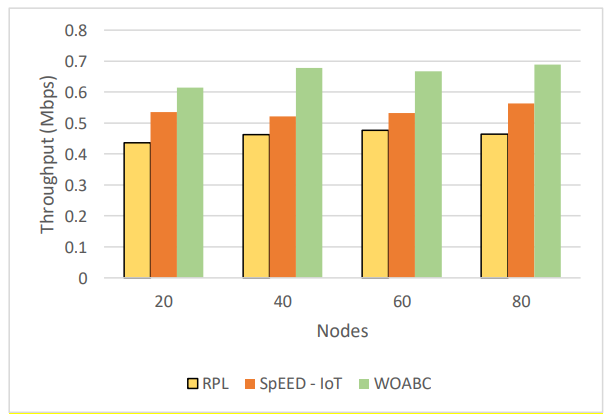
Throughput is represented as the successful transmission of information from the source to the destination node. Table 7 presented the comparison of throughout between RPL, SpEED – IoT and WOABC. Similarly, the comparative examination of the developed WOABC with conventional technique is comparatively illustrated in figure 8.
Table 7. Comparison of Throughput (Mbps)
Figure 08. Comparison of Throughput
The comparative examination of throughput expressed that the proposed WOABC exhibits higher performance than the other technique. The throughput of RPL and SpEED – IoT is minimal that the proposed WOABC.
8. CONCLUSION
Nowadays the technology of IoT is greatly integrated with smart cities to create a well-developed community. This paper presented a soft computing based RPL routing protocol for route establishment in the IoT environment. The proposed WOABC utilizes the optimization membership function for estimation of the route in the IoT network for the identification of the optimal path. The performance of the proposed WOABC is comparatively examined with SpEED – IoT and RPL techniques. The performance of WOABC is significant in terms of throughput, energy consumption, delay, and PDF rather than the conventional RPL and SpEED – IoT. In the future, this work will be improved with the integration of security algorithms for the IoT environment. The security approach can be adopted based on the cryptographic process for achieving data confidentiality.
CONFLICTS OF INTEREST
The author declares no conflict of interest.
REFERENCES
[1] Zaidan, A. A., &Zaidan, B. B. (2020). A review on the intelligent process for smart home applications based on IoT: coherent taxonomy, motivation, open challenges, and recommendations. Artificial Intelligence Review, 53(1), 141-165.
[2] Bhatnagar, S., &Kumra, R. (2020). Understanding consumer motivation to share IoT products data. Journal of Indian Business Research.
[3] Zhukovskiy, Y., Batueva, D., Buldysko, A., &Shabalov, M. (2019, October). Motivation towards energy saving by means of IoT personal energy manager platform. In Journal of Physics: Conference Series (Vol. 1333, No. 6, p. 062033). IOP Publishing.
[4] Krishna, B. S., &Gnanasekaran, T. (2017, February). A systematic study of optimal pathissues in Internet-of-Things (IoT). In 2017 International Conference on I-SMAC (IoT in Social, Mobile, Analytics and Cloud)(I-SMAC) (pp. 107-111). IEEE.
[5] Morgner, P., &Benenson, Z. (2018). Exploring optimal patheconomics in IoT standardization efforts. arXiv preprint arXiv:1810.12035.
[6] Lamaazi, H., &Benamar, N. (2017, June). RPL enhancement using a new objective function based on combined metrics. In 2017 13th international wireless communications and mobile computing conference (IWCMC) (pp. 1459-1464). IEEE.
[7] Perazzo, P., Vallati, C., Arena, A., Anastasi, G., & Dini, G. (2017, September). An implementation and evaluation of the optimal pathfeatures of RPL. In International Conference on Ad-Hoc Networks and Wireless (pp. 63-76). Springer, Cham.
[8] Wallgren, L., Raza, S., & Voigt, T. (2013). Routing attacks and countermeasures in the RPL-based internet of things. International Journal of Distributed Sensor Networks, 9(8), 794326.
[9] Verma, A., & Ranga, V. (2020). Optimal pathof RPL based 6LoWPAN Networks in the Internet of Things: A Review. IEEE Sensors Journal, 20(11), 5666-5690.
[10] Manikannan, K., & Nagarajan, V. (2020). Optimized mobility management for RPL/6LoWPAN based IoT network architecture using the firefly algorithm. Microprocessors and Microsystems, 77, 103193.
[11] Brachman, A. (2013). RPL objective function impact on LLNs topology and performance. In Internet of things, smart spaces, and next generation networking (pp. 340-351). Springer, Berlin, Heidelberg.
[12] Gaddour, O., Koubaa, A., Chaudhry, S., Tezeghdanti, M., Chaari, R., & Abid, M. (2012, March). Simulation and performance evaluation of DAG construction with RPL. In Third international conference on communications and networking (pp. 1-8). IEEE.
[13] Xie, H., Zhang, G., Su, D., Wang, P., & Zeng, F. (2014, June). Performance evaluation of RPL routing protocol in 6lowpan. In 2014 IEEE 5th International Conference on Software Engineering and Service Science (pp. 625-628). IEEE.
[14] Le, A., Loo, J., Luo, Y., &Lasebae, A. (2011, October). Specification-based for securing RPL from topology attacks. In 2011 IFIP Wireless Days (WD) (pp. 1-3). IEEE.
[15] Perrey, H., Landsmann, M., Ugus, O., Schmidt, T. C., &Wählisch, M. (2013). TRAIL: Topology authentication in RPL. arXiv preprint arXiv:1312.0984.
[16] Landsmann, M., Wahlisch, M., & Schmidt, T. C. (2013, April). Topology authentication in RPL. In 2013 IEEE Conference on Computer Communications Workshops (INFOCOM WKSHPS) (pp. 73-74). IEEE.
[17] Gaddour, O., &Koubâa, A. (2012). RPL in a nutshell: A survey. Computer Networks, 56(14), 3163-3178.
[18] Ma, G., Li, X., Pei, Q., & Li, Z. (2017, October). Aoptimal pathrouting protocol for Internet of Things based on RPL. In 2017 International Conference on Networking and Network Applications (NaNA) (pp. 209-213). IEEE.
[19] El Korbi, I., Brahim, M. B., Adjih, C., &Saidane, L. A. (2012, November). Mobility enhanced RPL for wireless sensor networks. In 2012 Third international conference on the network of the future (NOF) (pp. 1-8). IEEE.
[20] Mayzaud, A., Sehgal, A., Badonnel, R., Chrisment, I., &Schönwälder, J. (2014, June). A study of RPL DODAG version attacks. In IFIP international conference on autonomous infrastructure, management and optimal path(pp. 92-104). Springer, Berlin, Heidelberg.
[21] Fotouhi, H., Moreira, D., Alves, M., &Yomsi, P. M. (2017). mRPL+: A mobility management framework in RPL/6LoWPAN. Computer Communications, 104, 34-54.
[22] Cobarzan, C., Montavont, J., & Noel, T. (2014, June). Analysis and performance evaluation of RPL under mobility. In 2014 IEEE symposium on computers and communications (ISCC) (pp. 1-6). IEEE.
[23] Kharrufa, H., Al-Kashoash, H., Al-Nidawi, Y., Mosquera, M. Q., & Kemp, A. H. (2017, February). Dynamic RPL for multi-hop routing in IoT applications. In 2017 13th Annual Conference on wireless on-demand network systems and services (WONS) (pp. 100-103). IEEE.
[24] Somaa, F., El Korbi, I., Adjih, C., &Saidane, L. A. (2016, September). A modified RPL for wireless sensor networks with Bayesian inference mobility prediction. In 2016 international wireless communications and mobile computing conference (IWCMC) (pp. 690-695). IEEE.
[25] Bouaziz, M., Rachedi, A., Belghith, A., Berbineau, M., & Al-Ahmadi, S. (2019). EMA-RPL: Energy and mobility aware routing for the Internet of Mobile Things. Future Generation Computer Systems, 97, 247-258.
[26] Hoghooghi, S., &Javidan, R. (2020). Proposing a new method for improving RPL to support mobility in the Internet of things. IET Networks, 9(2), 48-55.
[27] Kharrufa, H., Al-Kashoash, H., & Kemp, A. H. (2018). A game theoretic optimization of RPL for mobile Internet of Things applications. IEEE Sensors Journal, 18(6), 2520-2530.
[28] Rabet, I., Selvaraju, S. P., Fotouhi, H., Adeli, M. H., Vahabi, M., Balador, A., … & Alves, M. (2021). Pushing IoT Mobility Management to the Edge: Granting RPL Accurate Localization and Routing. In World Forum on the Internet of Things WF-IoT, 22 Jul 2021, Louisiana, United States.
[29] Aneja, S., Mittal, S., & Sharma, D. Mobility Management Routing Protocol for Optimized QoS: A Review Study.
[30] Ancillotti, E., Vallati, C., Bruno, R., &Mingozzi, E. (2017). A reinforcement learning-based link quality estimation strategy for RPL and its impact on topology management. Computer Communications, 112, 1-13.
[31] Saleem, A., Afzal, M. K., Ateeq, M., Kim, S. W., &Zikria, Y. B. (2020). Intelligent learning automata-based objective function in RPL for IoT. Sustainable Cities and Society, 59, 102234.
[32] Xiao, W., Liu, J., Jiang, N., & Shi, H. (2014, November). An optimization of the object function for routing protocol of low-power and lossy networks. In The 2014 2nd International Conference on Systems and Informatics (ICSAI 2014) (pp. 515-519). IEEE.
[33] Safaei, B., Salehi, A. A. M., Monazzah, A. M. H., &Ejlali, A. (2019). Effects of RPL objective functions on the primitive characteristics of mobile and static IoT infrastructures. Microprocessors and Microsystems, 69, 79-91.
[34] Sousa, N., Sobral, J. V., Rodrigues, J. J., Rabêlo, R. A., &Solic, P. (2017, July). ERAOF: A new RPL protocol objective function for Internet of Things applications. In 2017 2nd International Multidisciplinary Conference on Computer and Energy Science (SpliTech) (pp. 1-5). IEEE.
[35] Qasem, M., Altawssi, H., Yassien, M. B., & Al-Dubai, A. (2015, October). Performance evaluation of RPL objective functions. In 2015 IEEE International Conference on Computer and Information Technology; Ubiquitous Computing and Communications; Dependable, Autonomic and Secure Computing; Pervasive Intelligence and Computing (pp. 1606-1613). IEEE.
[36] Kharrufa, H. D. Y. (2018). Data Routing for Mobile Internet of Things Applications (Doctoral dissertation, University of Leeds).
[37] Nurmio, J., Nigussie, E., &Poellabauer, C. (2015, October). Equalizing energy distribution in sensor nodes through optimization of RPL. In 2015 IEEE International Conference on Computer and Information Technology; Ubiquitous Computing and Communications; Dependable, Autonomic and Secure Computing; Pervasive Intelligence and Computing (pp. 83-91). IEEE.
[38] Alvi, S. A., Shah, G. A., & Mahmood, W. (2015, April). Energy efficient green routing protocol for internet of multimedia things. In 2015 IEEE tenth international conference on intelligent sensors, sensor networks and information processing (ISSNIP) (pp. 1-6). IEEE.
[39] Sharkawy, B., Khattab, A., &Elsayed, K. M. (2014, March). Fault-tolerant RPL through context awareness. In 2014 IEEE World Forum on Internet of Things (WF-IoT) (pp. 437-441). IEEE.
[40] Banh, M., Mac, H., Nguyen, N., Phung, K. H., Thanh, N. H., &Steenhaut, K. (2015, October). Performance evaluation of multiple RPL routing tree instances for Internet of Things applications. In 2015 International Conference on Advanced Technologies for Communications (ATC) (pp. 206-211). IEEE.
AUTHORS
Mr. Kishore Golla received his UG degree in Computer Science and Engineering from Gudlavalleru Engineering College, Gudlavalleru, Andhra Pradesh. He received his PG degree in Computer Science and Technologies with Artificial Intelligence and robotics from Andhra University, Visakhapatnam. He is doing research in Andhra University under the supervision of Prof. S. Pallam Shetty. He has qualified GATE, UGC-NET and CSIR-NET. His area of interests is Internet of Things (IoT), Wireless Sensor Networks, Machine learning and Artificial Intelligence.
Mr S. Pallam Shetty was born in 1961. He received his UG, PG and Ph.D. degrees in Computer Science from Andhra University; Visakhapatnam. He has 31 years of teaching experience and presently he is working as a Professor in the Department of Computer Science and Systems Engineering of AU College of Engineering, Andhra University. He has guided 32 Ph.D.’s. He has guided more than 250 M. Tech projects. He has been the member for many expert committees, member in Board of Studies for various colleges and universities. He visited Berkley University, USA.