IJCNC 02
AODVMO: A SECURITY ROUTING PROTOCOL USING ONE-TIME PASSWORD AUTHENTICATION MECHANISM BASED ON MOBILE AGENT
Huy D. Le1, Ngoc T. Luong2* and Tam V. Nguyen3
1Faculty of Information Technology, Ha Noi University of Business and Technology, Viet Nam
2Faculty of Mathematics and Informatics Teacher Education, Dong Thap University, Viet Nam
3Graduate University of Sciences and Technology, Vietnam Academy of Science and Technology, Viet Nam
ABSTRACT
Ad hoc On-demand Distance Vector (AODV) routing protocols is one of the most popular reactive protocol used for Mobile Ad hoc Network and is a target of many Denial-of-Service attack types. In this article, we propose a solution for Initialization and Providing the OTP based on Mobile Agent (IPOM). We also propose a Security Routing Protocol using One-Time Password Authentication Mechanism based on Mobile Agent (AODVMO) by extending the original AODV protocol and integrating IPOM solution. Analysis results confirm that AODVMO can prevent almost current routing protocol attack types, such as Blackhole / Sinkhole, Grayhole, Whirlwind, and Wormhole types. Using NS2, we evaluate the packet overhead for providing OTP, the security performance on random waypoint network topology under Blackhole attacks and the effect of security mechanism to the original protocol. Simulation results show that the proposed solution works well, the performance of AODVMO is good under Blackhole attacks, and slightly reduced when integrating the security mechanism in scenarios without attacks.
KEYWORDS
AODV, AODVMO, One-Time Password, Security routing protocol
1. INTRODUCTION
A Mobile Ad hoc Network (MANET[1][2][3]) is a collection of wireless mobile devices. The topology of the network can change unpredictably and frequently because of nodes exiting or joining. A node can act as a host and a router at the same time. The data transfer from a source node to a destination node can be routed by the means of mediate nodes. Denial of service (DoS) attacks aim to deny a user of a service or a resource he/she would normally expect to receive. Routing services at the network layer is one of the goals of DoS [4], such as Sinkhole[5], Grayhole [6], Flooding [7], and Whirlwind [8], Wormhole[9], and Blackhole [10] under DoS attacks. The AODV routing protocols is one of the most popular reactive protocol used for Mobile Ad hoc Network and is target of all attack types. There have been several publications to improve security for AODV protocol. The first approach is to create an intrusion detection system (IDSs[11][12]) IDSs depend on each attack form to detect, prevent so the security efficiency is limited, and announced solutions cannot be detected with an absolute successful rate and easily be overlooked if the Hackers change behavior when attacking. The next approach is to apply digital signature or hash functions, typically SAODV [13] and ARAN [14]. Their advantage is high security, but routing cost is too much, and it is difficult to apply in practice due to the limited processing capacity of mobile devices.
Another approach is to use OTP (One-Time Password) authentication mechanism in discovering routes because of its good security and low routing cost. OTP is password used in one time, widely applied by researchers in security sector such as LTE network [15], ATM transaction [16]. OTP is created using hash function f(x) (using SHAx or MDx), OTPk is created from OTPk-1. Two typical protocols are H(AODV) [17] and OTP_AODV [18] with the advantage of good security and reasonable routing cost. However, H(AODV) does not support an automatic OTP creation mechanism, OTP_AODV overcomes this disadvantage but it requires many ideal hypothetical conditions. This article describes AODVMO, an improved routing protocol from AODV, It has improved the limitation of protocol H(AODV) and OTP_AODV by supporting a solution for initialization and providing the OTP based on Mobile Agent. In this paper, the main contributions are as follows:
- Proposed a solution for initialization and providing the OTP based on Mobile Agent;
- Descripted a Security Routing Protocol using One-Time Password Authentication Mechanism based on Mobile Agent;
- Analyzed security performance for almost current routing protocol attack types;
- Evaluated the effectiveness and the performance of the proposed solution for high-speed mobility MANET under Blackhole attacks.
The remainder of this article is structured as follows Section 2 shows research works published related to the detection and prevention of the routing protocol attacks; Section 3 shows an OTP creating solution automatically, OTP authentication mechanism, and secure routing protocol AODVMO; Section 4 analyses security capability of the AODVMO protocol under all routing protocol attack types; Finally, conclusions and future works.
2. RELATED RESEARCHES
There have been some published research works related to increasing the security level of routing protocols based on authentication, integrity, and non-repudiation mechanisms. They used digital signatures or digital signatures, one-way hashing, considered in [19]. First, the authors[13] proposed an improved AODV named SAODV that uses a digital signature-based authentication, integrity and non-repudiation mechanism, which can prevent various types of attacks by protecting the routing change(hop count – HC)) and sequence number (SN)of the route discovery package. However, the disadvantage of SAODV is that it only supports end-to-end certification without step-by-step certification, so the intermediate node cannot confirm the packet from the previous node. Since SAODV has no key management mechanism, malicious nodes can bypass the security wall by using a fake key. Second, the authors [14] recommended the Authentication Routing protocol for Ad hoc Networks (ARAN). Unlike SAODV, ARAN’s route control packets are signed and certified hop-by-hop. ARAN has added a public key management mechanism, so a malicious node cannot bypass the security wall by using a fake key. ARAN’s RDP and REP architectures do not have HCs available to determine routing costs; this means that ARAN cannot realize the transmission cost from source to destination nodes, ARAN assumes that the first REP packet received is the one arriving on the route with the best routing cost.
Specially, we focus on security solutions using the OTP authentication mechanism. The H(AODV)[17] protocol developed from AODV by using the OTP authentication mechanism, hash function MD5 [20] is used to create OTP. During discovering route, OTP is attached with RREQ and RREP route control packet that allows the intermediate node to authenticate hop-by-hop previous node. By designing scenarios and simulating on NS3, the author has shown that the H protocol (AODV) is almost equivalent to AODV with the evaluation parameters being packet transmission rate and communication cost. This shows that security solutions have little effect on original protocol, and overcome the weaknesses of digital signature-based research. However, the mechanism for generating OTP for nodes has not been presented; the data of the “Hash Table” is designed as a whole to be accessible to all nodes. It can be seen that this is a limitation because the mobile network nodes are distributed, how to securely share the “Hash Table” is a challenge, besides, the author has not experimented in the network topology, there are malicious buttons to evaluate the effectiveness. The OTP creation mechanism is shown in[21], but proposal of separate security channel for providing the keys, this is very difficult because MANET network does not support infrastructure. The OTP_AODV protocol is proposed to overcome these weaknesses. The strength of the proposed OTP generation mechanism in the OTP_AODV protocol is that it does not require a separate communication channel, but requires many assumptions. It requires that each node in the network have a digital certificate and be authenticated by a trusted authority this condition is ideal. In addition, if the source node S (or other intermediate node) transmits the ADD_MSG packet at the same time as the RREQ packet to all neighboring nodes (Ai), so Ai can authenticate OTP of S to verify security. The ADD_MSGS packet (IDA, OTP S ,A ) contains address of neighbor node (1hop) of S and OTPk of S and A nodes. If node S has n neighbor nodes, ADD_MSG packet is sent n times, which greatly increases communication overhead. In particular, in a mobile network environment with high speed, this authentication method will be affected resulting in low efficiency. The reason is that node S relies on HELLO packet to determine the existence of neighboring nodes, HELLO packet is sent periodically, so neighbor nodes do not receive corresponding ADD_MSG packet to confirm OTP.
3. PROPOSED SECURITY PROTOCOL
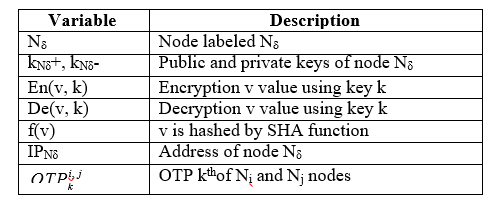
This section presents OTP creation mechanism based on Mobile Agent (MA [22]) and AODVMO protocol uses OTP authentication mechanism. The article uses some symbols as described in Table 1.
Table 1. Description of symbols
3.1. One-Time Password
Supposing that we need to create OTP for both nodes Ni and Nj, with MAX as number of OTPs in following steps:
Step 1: Node Ni and Nj use one key Y that it is created randomly and shared to each other.
Step 2: Node Ni creates and saves OTPs from 1 to MAX.
Step 3: Node Nj creates and saves CK test keys from 0 to MAX-1.
Figure 1. Description of OTP Authentication Mechanism
3.2. IPOM Solution
The OTP creation stage must be completed before nodes participate in route discovery process. As shown in introduction, the characteristic of MANET network is all nodes moving randomly, each node can be neighbor of any node. Therefore, each node shall have OTP with n-1 other nodes. OTP creation algorithm in Section 3.1 shows that any two nodes share Y key to each other to create OTP, this is challenge because MANET network does not have infrastructure so it does not support safety channel. Solution of the article is to use MA to share Y key to nodes which need to create OTP and CK. Similar to [18], the article assumes that each node has one public key (k+) and one secret key(k-) based on RSA cryptosystem [23]. The key of each node is used to authenticate during OTP creation.
3.2.1. Proposed New Agents
A Mobile agent is an entity with basic properties such as: processing, intelligence and mobile forms. For MANET, agent is shown in form of packets for transmitting or collecting information from other nodes in the network [24]. In recent years, there have been some research involving the use of MA to improve routing efficiency for AODV, typical is MAR-AODV [25]. In addition, an improvement from AODV is to use security agents (Security MA – SMA) to detect flooding attack is SMA2AODV published in [26]. In this article, to create OTP, we propose some new agents with processing, intelligence and mobile capacity as described in Table 2. Common characteristic of agents (except MAT) is mobility to perform appropriate processing for each function. Two OTPR and CKR agents are mobile in form of single direction, OTPP, CKP and OTPU agents are mobile in form of broadcast. In addition, they are intelligent by identifying correctly address of receive node, ability of security Y key.
Table 2. List of new Mobile Agents
Description:
- OTPP agent is structured similarly with RREQ packet of AODV protocol with two new attributes: KEY and IP, has function of sending Y key for Ni to create OTP. And, CKP agent is structured as the same OTPP agent, and allow to send Y key for Nj to create CK.
- OTPR agent is structured similarly with RREP packet in AODV protocol with new attribute as ACK, its function is send authentication to NOTP when Ni receives Y key to create OTPs. And, CKR agent is structured similarly with OTPR agent to send authentication when Nj receives Y key to create CK.
- OTPU agent is structured similarly with RREQ packet in AODV protocol with two new attributes are UDT and IP, allow Ni to send OTP reissue request.
- MAT agent only has processing function, used to check OTP issue. MTA is intelligent by identifying nodes which are not granted OTP, CK or OTP reissue to provide appropriate processing options.
3.2.2. OTP Creation Algorithm
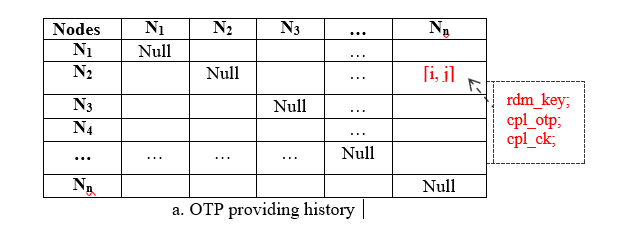
Assuming that network topology has n nodes, a trusted network node is NOTP used to manage public key and history of the OTP grant, NOTP does not participate in data packet routing to ensure security. History data of OTP grant is one matrix (DM) with structure as Figure 2a, public data (PK) as Figure 2b.
Figure 2. Description of Database at NOTP node
Each cell [i, j] of DM matric has three attributes including rdm_key, cpl_otp and cpl_ck. The rdm_key attribute saves Y key for Ni and Nj node; cpl_otp has value of 0, equal to Ni note without OTP successful creation, on the contrary 1, 2 show Ni node has created OTP; cpl_ck has value of 0, equal to Nj without CK successful creation, on the contrary is 1. Each cell PK[i] stores the public key of node Ni, PK updated by the administrator to ensure that only “friendly” network node can create OTP. The original state of the system is all non-OTP-creation nodes. Therefore, corresponding values of elements in cell [i, j] in DM matrix is generated default including Y key generated randomly and saved in rdm_key; cpl_otp and cpl_ck initialized to 0.
Step 1: OTP initialization
MAT agent operates at NOTP node and can access data of DM and PK. After a period (TI), MAT approves information in each cell [i, j] in DM matrix and performs:
- If there is OTP uninitialized Ni node (DM[i, j].cpl_otp = 0), MAT sends Y key to Ni by activating OTPP mobile agents to Ni with KEY and address of Nj node as described in (1). Where, KEY saves Y key, hashed and encrypted to ensure that only appropriate receive node can decrypt the information as in eqn 2.
- If there is Nj that does not receive Y key (DM[i, j].cpl_ck = 0), MAT sends Y key to Nj by activating CKP mobile agents to Nj with KEY and address of Ni node as described in (3). Where, KEY is hashed and encrypted to ensure that only appropriate receive node can decrypt the information as in eqn 4.
- If there is Ni that needs to re-initialize OTP (DM[i, j].cpl_otp = 2), MAT re-creates Y key and save in rdm_key field, assign cpl_otp = cpl_ck = 0 in cell [i, j] of DM matrix. At the same time, activate two OTPP and CKP agents to transfer Y key to two Ni and Nj nodes.
Step 2: Save OTP, CK and confirm success
After successfully creating CK, Nj shall activate CKR agents to move to node NOTP to confirm that Nj has successfully created CK as described in (9). Where, ACK is calculated by encrypting hash value of NOTP node address with secret key of Nj and public key of NOTP as eqn 10.
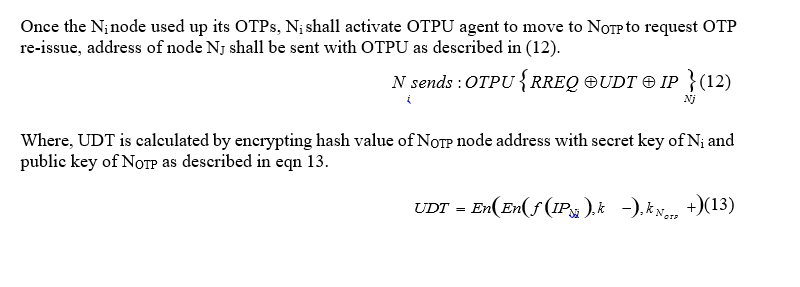
Step 3: OTP update request
When OTPU agent moves to NOTP, NOTP checks to ensure agent comes from Ni and send to NOTP by using secret key of NOTP and public key of Ni to decrypt UDT attributes as eqn 14. If decryption result of vl is the same with hash value of IPNj address, NOTP accepts OTP re-issue request from node Ni by assigning attribute cpl_otp = 2 in cell [i, j] of DM matrix. OTP re-initialization process for Ni is done as Step 1.
Example: In order to initialize OTP for N5 and N6, NOTP performs as below: First, MAT agent checks DM matrix and finds that N5 has not initialized OTP (DM[5, 6].cpl_otp = 0). MAT activates OTPP agent to broadcast to N5, KEY field value is calculated as in eqn 2. Next, N5 uses eqn 5 to encrypt KEY attribute and initialize OTP, at the same time active OTPR to unicast to NOTP to confirm that N5 has initialized OTP successfully, value of ACK field is calculated according to eqn 7. Finally, when OTPR agent moves to NOTP, NOTP saves in DM matrix in cell [5, 6] by assigning value of cpl_otp = 1, to record the successful initialization of OTP.
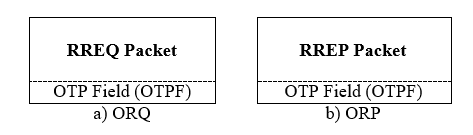
3.3. Security Discover Route Algorithm
The security discovery route algorithm of AODVMO is developed from AODV protocol in two phases: (1) Request Route; (2) Reply route. We use the route control packets as in AODV and modify them to satisfy our requirements. For example, the OTP route request packet(ORQ) is used for route discovery and the OTP route reply packet (ORP) is used for route reply. While most fields stay as they were in AODV, in addition, we add a new OTPF field as Figure 3, this attribute is used to authenticate OTP for security goals.
Figure 3. Description of Route Control Packet of AODVMO
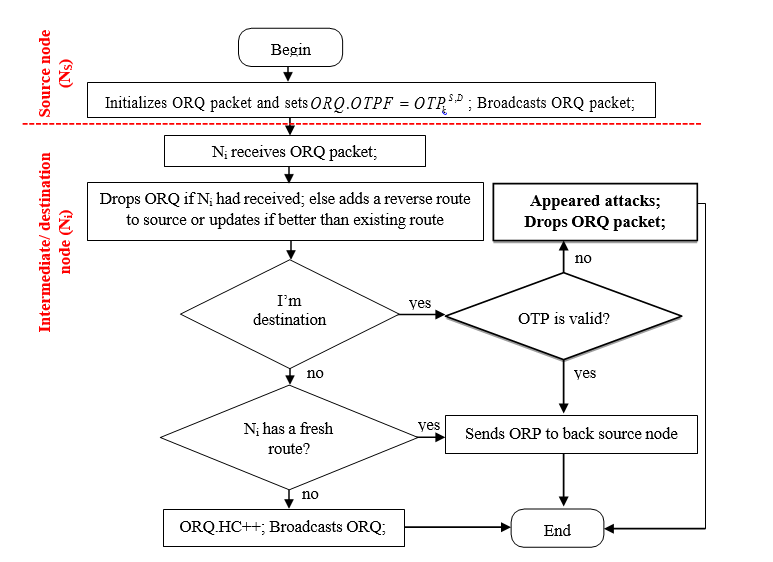
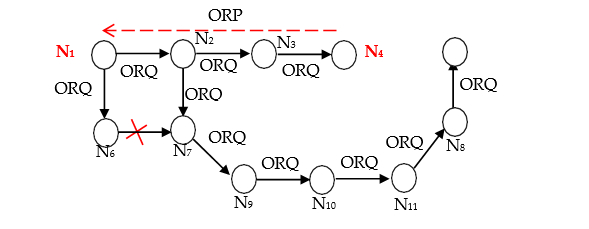
3.3.1. Broadcast Algorithm of ORQ Packet
Figure 4 describes broadcast algorithm of route request packet supporting end-to-end OTP authentication mechanism. Source node NS discovers a route to destination node ND by broadcasting ORQ to all neighbors. The ORQ packet is initialized with OTP of NS and ND (OTPS,D ) as description (15).
Figure 4. Route Request Algorithm
3.3.2. Unicast Algorithm of ORP Packet
Figure 5 describes algorithm of route reply packet supporting hop-by-hop OTP authentication mechanism. To reply route, destination node ND finds an entry in its Routing Table (RT) to determine next hop (NNH) to source. ORP packet is initialized with OTP of ND and NNH ( OTPD, NHm ) as (16).
Assuming thatNj is preceding node which sent or forwarded ORP packet. When receiving ORP packet from Nj, intermediate node Ni process ORP packet as follow:
node participates in discovering route and end the algorithm;
- If Ni is source node, Ni adds a new entry to ND into its RT, successful discover route; in contrast, Ni finds next hop NNH in its RT to forward ORP to source. If found a route to NS then Ni
re-updates value of OTPF field by OTPi,NH before forwarding ORP to source through next hop n NNH; in contrast, ORP packet is dropped and end the algorithm.
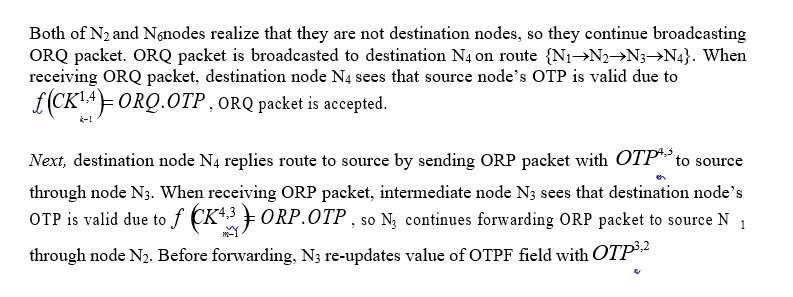
3.3.3. An Example of the Algorithm
Figure 6 describes source node (N1) to discover route to destination (N4) by using AODVMO routing protocol. First, source node N1 broadcasts ORQ packet to its neighbors including N2 and N6. ORQ packet is initialized with OTP1,4
Figure 6. Description of Route Discovery Process for AODVMO
4. SECURITY CAPABILITY EVALUATION
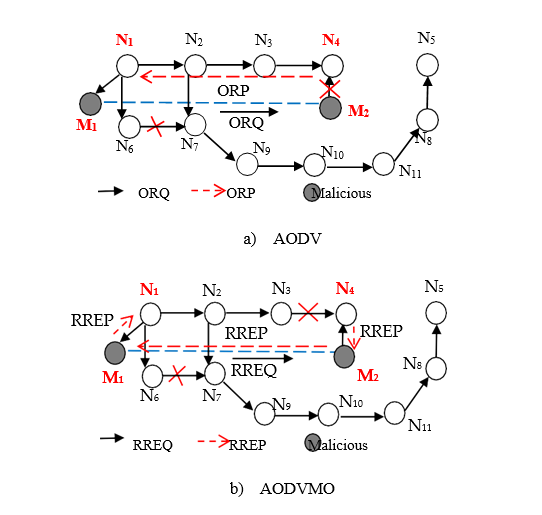
Similar to the author [18], the article analyzes the security capability of the AODVMO protocol when being attacked by Blackhole and Wormhole. In addition, other forms of attacks such as Grayhole, Flooding, and Whirlwind are also analyzed in this section.
4.1. The Security Capability of AODVMO
First, the article analyzes the ability to detect attacks of the Blackhole, Sinkhole, Grayhole and Whirlwind. The characteristics of these attack forms have been analyzed, all summarized in Table 3 in [8].
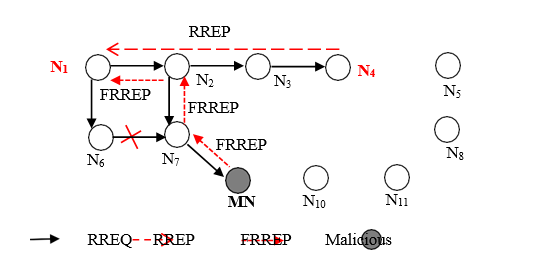
a) AODV
b) AODVMO
Figure 7. Description of Blackhole, Grayhole and Whirlwind Detection
Network topology (Figure 7.a) describes source node N1 discovering the route to destination node N4 with the AODV protocol. When receiving RREQ packet, the malicious node MN sends a fake reply route packet (FRREP) to N1 on the path {MN®N7® N2®N1}. In addition, destination node N4 also sends the RREP packet to the source on path {N4®N3®N2®N1}. Node N2 sees that there are two paths to the destination because of N2. The corresponding route of FRREP packet are more “fresh” because the value of the destination sequence number (DSN) of FRREP packet is larger than the RREP packet. The result is N1 discovering route to destination N4 on the path of {N1® N2®N7®MN}, the malicious node MN appears in the discovered route. In contrast, AODVMO can detect these types of attacks successfully through the description in Figure 7.b. When receiving the fake reply route packet (FORP), node N7 checks and finds that the OTP’s value of the FORP packet is invalid. This is because the NM and N7 have not initialized OTP and CK from node NOTP. Therefore, FORP packet is dropped, node N7 does not set up route through node MN, attack fails.
Next, the article analyzes the ability to detect Wormhole attacks. Wormhole attacks can be performed through a private link or by using a packaging mechanism. This attack type is served for the purpose of eavesdropping, data analysis. Network topology in Figure 8.a appears a link between two malicious nodes M1 and M2. When source node N1 discovers route to destination node N4, RREQ packet through M1 and M2 to destination N4 on path {N1®M1®M2 ®N4}. N4 cancels RREQ packet from N3 because of receiving earlier from M2. Destination node N4 replies route on the path of {N4®M2®M1®N1}. The result is source node N1 setting up destination according to path {N1®M1®M2®N4}, this route containing two malicious nodes M1 and M2. In contrast, AODVMO can detect Wormhole attack form successfully through description in Network topology Figure 8.b, when receiving ORQ from M2, N4 checks and finds that OTP value of ORP packet is invalid. The reason is because node M2 and N4 have not been provided OTP from NOTP.
Figure 8. Description of Wormhole Detection
Finally, in Flooding attack uses RREQ packet, the malicious nodes broadcasts RREQ packet with high frequency [26]. As a result, creating packet broadcast, affecting to processing process of nodes and increasing communication overhead. Similarly, Hacker can attack AODVMO protocol by using ORQ packet. Because AODVMO only supports end-to-end authentication mechanism for ORQ packet, so intermediate node can not detect that MN node broadcasting ORQ packet is illegal. Therefore, AODVMO is not efficient against Flooding attacks.
4.2. The Characteristics of AODVMO
The characteristics of AODVMO and several related researches are summarized in Table 3.
Table 3. Comparison of AODV and related researches
4.2. Simulation Results
The article uses NS-2.35 [27] to evaluate the limitations and security efficiency of proposed solution, simulation screen as show in Figure 9. Evaluation metrics such as: (1) Overhead packets for providing OTP; (2) Packet delivery ratio; (3) Route discovery delay, average route length and End-to-End delay time.
Figure 9. NS2 Simulation Screen
The simulation area was a rectangular region with a size of 1000 x 1000 m2, which was chosen to ensure that there existed multiple hops within the network. We use 802.11 MAC layer, 50 normal nodes move with 10m/s maximum speeds under Random Waypoint model [28], 3000 seconds for simulation. Each scenario has 10 pairs of communicating nodes, the source sending out constant bit rate (CBR) traffic with packet sizes of 512bytes at a rate of 2 packets per second, all data source is started the second of 2000 and the following data source is 10 seconds apart, FIFO queue type, two prime numbers p=29 and q=31, are used to make keys in RSA, details of parameters in Table 4.
Table 4. Simulation parameters
First, the article evaluates number of OTPP, CKP, OTPR, CKR and OTPU packets, overhead for OTP re-initialization. With a constant of MAX = 50 or 100 equal to each node generates 50 or 100 OTP when receiving key. The simulation result in Figure 10 shows that the number of overhead packets to initialize OTP depends on parameter MAX. With MAX = 50, the number of overhead packets is 1,058,392.0 packets 11,473.0 packets higher than MAX = 100 is. The reason is when setting MAX = 50, the nodes require more OTP than MAX = 100, so the number of wasted packets is higher.
Figure 10. Packet Overhead for Providing OTP
Next, the article evaluates the security efficiency of AODVMO protocol by setting a malicious node standing on position (400, 400) and performs Blackhole (BH) attack, described in [30]. The evaluating parameter is the packet delivery ratio to the destination (PDR) as eqn 17, n is the number of the data packets delivery to the destination; m is the number of the data packets sent.
The simulation result in Figure 11 shows that the AODV protocol is severely damaged when attacked by Blackhole, PDR reached 86.16% in normal topology and 15.24% when attacked, reducing 70.92%. In contrast, the security mechanism has efficiency, so the PDR of AODVMO protocol is only affected slightly, reduce 1.73% in comparison to normal topology is 80.92%. However, the security mechanism affected to the PDR of original protocol, when compared to AODV, AODVMO was 5.24% lower when simulated in normal (NM) topology. This can be improved if the MAX parameter is given the larger setup but will affect the security efficiency.
Figure 11. Packet Delivery Ratio
The simulation result in Figure 12 shows that the security mechanism of AODVMO affected to the performance of the original AODV protocol. After 3000s for simulation times, ART of AODVMO is 0.209s, increased 0.031s, and ARL of AODVMO is 3.228hops, increased 0.282hops, and ETE of AODVMO is 0.821, increased 0.378s when compare to AODV.
a) Average of times for route discovery
b) Average of route length
c) End-to-End delay
Figure 12. ART, ARL and ETE
5. CONCLUSION
In this article, we proposed an IPOMsolutionfor initialization and providing the OTP based on Mobile Agent and a security routing protocol AODVMO. The OTP initialization mechanism in IPOM based on mobile agent topology. AODVMO has many advantages compared to some published studies such as: no need secure channel or require nodes with Digital Certificate that was confirmed by a competent authority. The improved security discover route algorithm in AODVMO allows end-to-end authentication ORQ packet and hop-by-hop authentication of ORP packet during discovering route process for security checks. The AODVMO protocol developed from AODV can effectively detect some types of network attacks such as Blackhole, Grayhole, Wormhole and Whirlwind. The simulation results under Blackhole attack shown that proposed solution has worked well with PDR being improved very well. In addition, inscenarios without attacks, the efficiency of discover route of the AODVMO protocol is affected slightly, It improved the limitations of security solutions based on Digital Signature.
However, the end-to-end authentication of the ORQ packet has the limitation that the intermediate node cannot authenticate the ORQ packet from its predecessor, so AODVMO cannot detect a Flooding attack. In addition, security for data stored in nodes is also a challenge that needsto be solved in subsequent studies.
CONFLICT OF INTEREST
The authors declare no conflict of interest.
AUTHOR CONTRIBUTIONS
All authors conducted the research; Le Duc Huy, Luong Thai Ngoc and Nguyen Van Tam conducted the experiments in the laboratory. Le Duc Huy, Luong Thai Ngoc and Nguyen Van Tam wrote the paper; all authors had approved the final version.
ACKNOWLEDGMENTS
This research is supported by the project SPD2021.01.26, The Dong Thap University, Vietnam.
REFERENCES
- H. Jeroen, M. Ingrid, D. Bart, and D. Piet, “An overview of Mobile Ad hoc Networks: Applications and challenges,” Journal of the Communications Network, vol. 3, no. 3, pp. 60–66, 2004, doi: 10.1109/MPRV.2009.2.
- D. K. Sharma and N. Goenka, “An effective control of Hello process for routing protocol in MANETS,” International Journal of Computer Networks & Communications, vol. 13, no. 5, pp. 37–56, 2021.
- G. K. Pallai, M. Sankaran, and A. K. Rath, “Self-Pruning based Probabilistic Approach to Minimize Redundancy Overhead for Performance Improvement in MANET,” International Journal of Computer Networks & Communications, vol. 12, no. 3, pp. 1–20, 2021.
- R. Di Pietro, S. Guarino, N. V. Verde, and J. Domingo-Ferrer, “Security in Wireless Ad-hoc Networks
- – A survey,” Computer Communications, vol. 51, pp. 1–20, 2014, doi: 10.1016/j.comcom.2014.06.003.
- E. C. H. Ngai, J. Liu, and M. R. Lyu, “An efficient intruder detection algorithm against sinkhole attacks in wireless sensor networks,” Computer Communications, vol. 30, pp. 2353–2364, 2007, doi: 10.1016/j.comcom.2007.04.025.
- A. Dhaka, A. Nandal, and R. S. Dhaka, “Gray and Black Hole Attack Identification Using Control Packets in MANETs,” Procedia Computer Science, vol. 54, pp. 83–91, 2015, doi: https://doi.org/10.1016/j.procs.2015.06.010.
- N. T. Luong, T. T. Vo, and D. Hoang, “FAPRP: A Machine Learning Approach to Flooding Attacks Prevention Routing Protocol in Mobile Ad Hoc Networks,” Wireless Communications and Mobile Computing, 2019, doi: 10.1155/2019/6869307.
- L. Thai-Ngoc and V. Thanh-Tu, “Whirlwind: A new method to attack Routing Protocol in Mobile Ad hoc Network,” International Journal of Network Security, vol. 19, no. 5, pp. 832–838, 2017.
- T. T. Vo, N. T. Luong, and D. Hoang, “MLAMAN: a novel multi-level authentication model and protocol for preventing wormhole attack in mobile ad hoc network,” Wireless Networks, vol. 25, no. 7, pp. 4115–4132, 2019, doi: 10.1007/s11276-018-1734-z.
- M.-Y. Su, “Prevention of selective black hole attacks on mobile ad hoc networks through intrusion detection systems,” Computer Communications, vol. 34, no. 1, pp. 107–117, 2011, doi: 10.1016/j.comcom.2010.08.007.
- R. Mitchell and I.-R. Chen, “A survey of intrusion detection in wireless network applications,”
Computer Communications, vol. 42, 2014, doi: 10.1016/j.comcom.2014.01.012.
- F. H. Tseng, L. Chou, and H. C. Chao, “A survey of black hole attacks in wireless mobile ad hoc networks,” Human-centric Computing and Information Sciences, vol. 1, no. 1, p. 4, 2011, doi: 10.1186/2192-1962-1-4.
- M. G. Zapata, “Secure ad hoc on-demand distance vector routing,” ACM SIGMOBILE Mobile Computing and Communications Review, 2002, doi: 10.1145/581291.581312.
- K. Sanzgiri, B. Dahill, B. N. Levine, C. Shields, and E. M. Belding-Royer, “A Secure Routing Protocol for Ad Hoc Networks,” in Proceedings of the 10th IEEE 2196 International Conference on Network Protocols, IEEE Computer Society, Washington DC, USA, 2002, pp. 78–89, doi: 10.1007/s11276-004-4744-y.
- S. Holtmanns and I. Oliver, “SMS and one-time-password interception in LTE networks,” in IEEE International Conference on Communications, 2017, pp. 1–6, doi: 10.1109/ICC.2017.7997246.
- M. Karovaliya, S. Karedia, S. Oza, and D. R. Kalbande, “Enhanced security for ATM machine with OTP and facial recognition features,” in Procedia Computer Science, 2015, vol. 45, pp. 390–396, doi: 10.1016/j.procs.2015.03.166.
- C. Lee, “A Study on Effective Hash Routing in MANET,” Advanced Science and Technology Letters, vol. 95, pp. 47–54, 2015, doi: http://dx.doi.org/10.14257/astl.2015.95.10.
- A. B. C. Douss, R. Abassi, and S. G. El Fatmi, “A Novel Secure Ad hoc Routing Protocol Using One Time Password,” in International Conference on Advanced Logistics and Transport, 2014, pp. 41–46.
- J. Von Mulert, I. Welch, and W. K. G. Seah, “Security threats and solutions in MANETs: A case study using AODV and SAODV,” Journal of Network and Computer Applications, vol. 35, no. 4, pp. 1249–1259, 2012, doi: 10.1016/j.jnca.2012.01.019.
- C.-S. Lee, “A Study on MD5 Security Routing based on MANET,” The Journal of the Korea institute of electronic communication sciences, vol. 7, no. 4, pp. 797–803, 2012.
- H. Zhu, Z. Yan, L. Haiyang, and L. Lin, “A Novel Biometrics-based One-Time Commitment Authenticated Key Agreement Scheme with Privacy Protection for Mobile Network,” International Journal of Network Security, vol. 18, no. 2, pp. 209–216, 2016.
- J. Cao and S. K. Das, Mobile Agents in Networking and Distributed Computing. John Wiley and Sons, 2012.
- W. Diffie, W. Diffie, and M. E. Hellman, “New Directions in Cryptography,” IEEE Transactions on Information Theory, vol. 22, no. 6, pp. 644–654, 1976, doi: 10.1109/TIT.1976.1055638.
- V. D. Quy, N. D. Han, and N. T. Ban, “A_WCETT: A High-Performance Routing Protocol based on Mobile Agent for Mobile ad hoc Networks in 5G,” Journal of Search, Development and Application on Information & Communication Technology, vol. 17, no. 31, pp. 14–21, 2017.
- C. T. Cuong, V. T. Tu, and N. T. Hai, “MAR-AODV: Innovative Routing Algorithm in MANET Based on Mobile Agent,” in IEEE WAINA (Spain), 2013, pp. 62–66.
- V. Thanh-Tu and L. Thai-Ngoc, “SMA2AODV: Routing Protocol Reduces the Harm of Flooding Attacks in Mobile Ad Hoc Network,” Journal of Communications, vol. 12, no. 7, pp. 371–378, 2017.
- T. Issariyakul and E. Hossain, “Introduction to Network Simulator NS2,” Springer, pp. 1–438, 2009, doi: 10.1007/978-0-387-71760-9.
- J. Yoon, M. Liu, and B. Noble, “Random waypoint considered harmful,” IEEE INFOCOM 2003, vol. 2, pp. 1–11, 2003, doi: 10.1109/INFCOM.2003.1208967.
- P. Jones, “US secure hash algorithm 1 (SHA1),” RFC 3174 (Informational), pp. 1–22, 2001, doi: 10.17487/rfc3174.
- R. R. Chandan and P. K. Mishra, “Consensus routing and environmental discrete trust based secure AODV in MANETs,” International Journal of Computer Networks and Communications, 2020, doi: 10.5121/ijcnc.2020.12301.
AUTHORS
Huy D. Le was born in Bac Ninh province, Vietnam in 1990. He received a B.E. degree in Information Technology from Hanoi University of Business and Technology, 2012, and M.A. degree in Computer Science from the Thai Nguyen University Of Information And Communication Technology, 2015. He is currently studying for his Ph.D. at the Graduate University of Sciences and Technology; Vietnam Academy of Science and Technology. His research interests include computer networks, and security mobile ad hoc networks
Ngoc T. Luong is working in the Faculty of Mathematics and Informatics Teacher Education, Dong Thap University. He received aB.E. degree in Computer Science from Dong Thap University in 2007, M.A. degree in Computer Science from Hue University of Sciences in 2014 and Ph.D. degree in Computer Science from Hue University of Sciences in 2020. His fields of interest are analysis and evaluation of network performance, security wireless Mobile Ad hoc Networks
Tam V. Nguyen was born in Vinh Phuc province, Vietnam in 1947. He graduated from CVUT University, Praha, Czechoslovakia in 1971. He successfully defended his Ph.D.at VUMS Computer Research Institute, Praha, Czechoslovakia in 1977. He was appointed as Associate Professor of Informatics in 1996. Currently, he works Graduate University of Sciences and Technology; Vietnam Academy of Science and Technology. His research interests include Network Technology, Network Performance, and Security.