IJCNC 06
BER ANALYSIS FOR DOWNLINK MIMO -NOMA SYSTEMS OVER RAYLEIGH FADING CHANNELS
Vu Tran Hoang Son1, 2 and Dang Le Khoa1,2
1VNUHCM – University of Science, Ho Chi Minh City, Vietnam
2Vietnam National University, Ho, Chi Minh City, Vietnam
ABSTRACT
The Multiple-input multiple-output (MIMO) technique combined with non-orthogonal multiple access (NOMA) has been considered to enhance total system performance. This paper studies the bit error rate of two-user power-domain NOMA systems using successive interference cancellation receivers, with zero-forcing equalization over quasi-static Rayleigh fading channels. Successive interference cancellation technique at NOMA receivers has been the popular research topic due to its simple implementation, despite its vulnerability to error propagation. Closed-form expressions are derived for downlink NOMA in single-input single-output and uncorrelated quasi-static MIMO Rayleigh fading channel. Analytical results are consolidated with Monte Carlo simulation.
KEYWORDS
Bit error rate, Multiple-input multiple-output, non-orthogonal multiple access.
- INTRODUCTION
Recent communication systems aim to meet the high capacity requirements. Non-orthogonal multiple access (NOMA) is not only available in conventional 4G, recommended in 5G and future 6G due to many outstanding benefits [1, 2]. NOMA can be divided into two main categories as power-domain NOMA and code-domain NOMA. Successive interference cancellation (SIC) is well-known in power-domain NOMA systems for its simple implementation, although it has low performance compared to other detection techniques such as using log-likelihood ratios[3], or machine learning[4, 5]. There have been many studies in the probability of outage[6], power allocation[7], system capacity [8], bit error rate (BER)[9-13], showing that NOMA is superior to conventional orthogonal multiple access[14]. NOMA can be integrated with multiple input, multiple output(MIMO), which can result in a notable increase in capacity[15], or even combined with deep neural network and beam forming [16]. To the best of the authors’ knowledge, there is no approach to BER expressions when changing between multiuser superposition transmission (MUST) categories in 3GPP LTE Release 13 [17, 18] to generate NOMA signals. The main contributions of this paper are:
1) Closed-form BER expressions for NOMA in two-user scenario with quadrature phase shift keying(QPSK) modulation over quasi-static single-input single-output (SISO) Rayleigh fading channels are investigated.
2) Under certain conditions, BER expressions perfectly suit the MIMO case. This is verified via Monte Carlo simulation.
3) When Rayleigh channel has multiple taps, simulations barely fit analytical results due to the limited response of zero-forcing(ZF) equalization. Because of this, via simulations, authors have combined the conventional systems with orthogonal frequency division multiplexing (OFDM) to reduce inter-symbol interference (ISI), regardless of non-linearities.
From this section, the paper is organized as follows. Section 2 presents and compares with related work in the same field. Section 3 introduces the system model and the corresponding parameters. Based on preexisting papers, Section 4 analyzes BER in MUST category 1. Section 5 proceeded to MUST category 2 with a different approach, giving unified results when applying in MUST category 1. Section 6 considered the effect of MIMO in NOMA systems, under certain constraints, compared to SISO. All expressions are verified in Section 7 via simulations, and conclusions along with future works are drawn in Section 8.
2. RELATED WORK
BER is one of the key factors to evaluate MIMO-NOMA system performance. This section will consider related work that analyzes BER in the NOMA system. In [9], BER expressions of uplink NOMA with SIC receivers has been derived over Additive White Gaussian Noise(AWGN) channels. In [10], F. Kara has developed BER expressions for downlink NOMA over Rayleigh fading channels with two users: far user (FU) using binary phase shift keying (BPSK), and near user (NU) using QPSK. All expressions are followed by simulations. With significant effort, T. Assaf et al. have introduced analytical BER through Nakagami-m fading channels in scenarios of two and three users with QPSK modulation in [11], and through AWGN channels with general M-QAM modulation[13].The authors in [12] investigated BER in QPSK-modulated NOMA users on the AWGN channel and verified by software defined radio platforms. Similar research in recent papers shows that NOMA signals are generated using only MUST type 1 and are limited in SISO systems. Moreover, in the following years, applications of MIMO, or even massive MIMO (m-MIMO), will be in new generation mobile networks. Our research is to find out the BER analysis approach united in both MUST type 1 and type 2 in SISO systems, propose a comparison with MIMO in Rayleigh fading channels, using Monte Carlo simulations to validate the results.
3. SYSTEM MODEL
3.1. Downlink NOMAsystems
Consider downlink SISO-NOMA system with two user’s equipment (UEs) and a base station (BS) as depicted in Figure 1.

Figure 1. Downlink SISO-NOMA system
BS will generate NOMA signals using MUST cat.1 or MUST cat.2 [17, 18]. Based on Figure 1,
the generated signal Xsc can be expressed as

SIC process will be conducted at NU. NU will estimate FU’s symbols and use SIC to eliminate
interference by subtracting FU’s symbols from the received signal, then NU decodes its own
symbols. On the other hand, FU does not need to apply SIC, instead detect its symbols by
considering others as noise.
3.2. MIMO-NOMA system
One of the techniques in MIMO is spatial division multiplexing (SDM), which takes advantage of
the multipath channel to enhance system capacity without increasing the bandwidth. Figure 2
presents a downlink MIMO-NOMA system using SDM 2×2.

Figure 2. Downlink MIMO-NOMA system
Because the UEs are identical, we will investigate a general MIMO SDM 2×2 case as Figure 3.
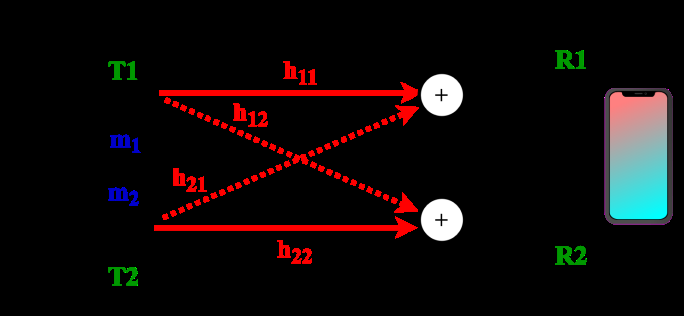
Figure 3. MIMO SDM 2×2 system
If the spacing between the transmitting and receiving antennas is large enough, the scattering
characteristics will be uncorrelated, so each path is independent. Under these conditions, the
desired signal from the target transmitting antenna can be detected by treating other transmitted
signals as interferences. This is called linear signal detection. We will concentrate on the
technique that nullifies the interference, zero-forcing method. From Figure 3, the received signal
matrix can be expressed as [21]


From (3.5), n and expnj is different by a phase shift, however, n is circularly symmetric
so n and expnj have the same probability distribution. This is one of the key factors to
form the composite reference constellation discussed later in Section 4 and Section 0.
4. BER IN MUST CATEGORY 1
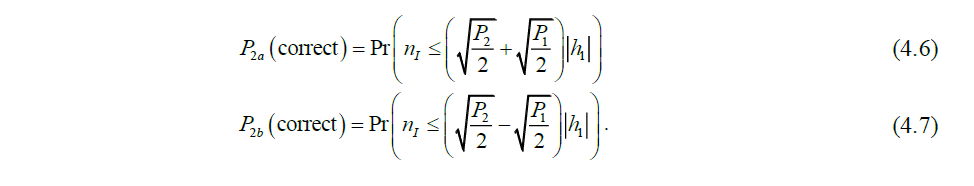
Based on (3.5), Figure 4shows the reference constellation to detect signals at each UE when using
MUST category 1. Red bits denote FU’s bits, and black bits are NU’s bits. The order of bits is
ascending, where the most significant bit is leftmost and is stated as the first bit.

Figure 4. Reference constellation at the receiver when using MUST cat.1
4.1. BER of Far User
As seen in Figure 4, the first bit of UE2, which relies only on the in-phase component, will be
detected erroneously when one of these following cases occurs.

Considering the second bit of UE2, which depends only on the quadrature component of the
signal, we see that the error cases are identical to (4.1) and (4.2). Assume the prior probability of
0’s and 1’s bit is equal, so the prior probability of each symbol is also equal. The symmetry
between in-phase and quadrature components of the symbol allows us to investigate only one of
them. Therefore, the variance of considered AWGN now is only half of the total noise, e.g.,

In the case of quasi-static Rayleigh channel, using [10, 20, 22] with (4.4), the average BER
expression of UE2 is defined as
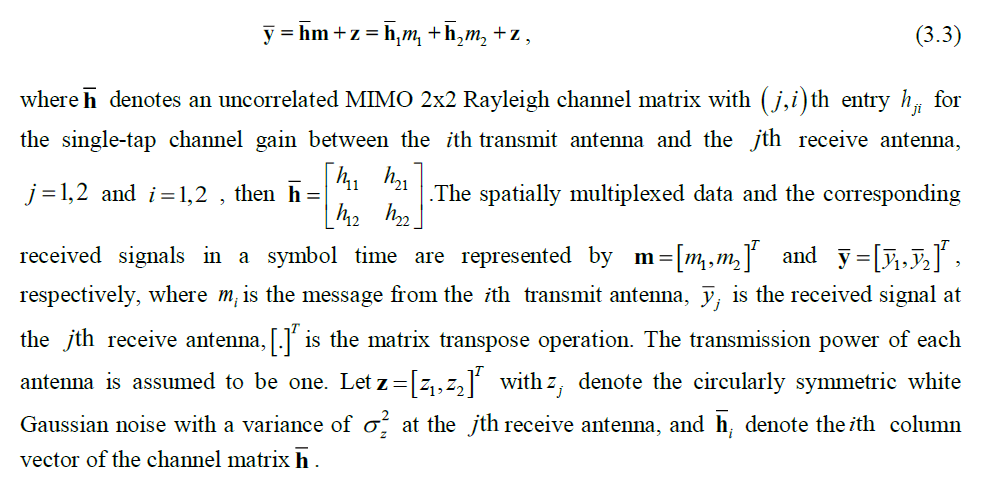
4.2. BER of Near User
Based on [10-13], this section proposes an approach to derive BER of NU. Due to the SIC
process, NU detection must be considered under the condition of FU detection. On the other
hand, in Figure 4, if the second bit of FU is in error, it has no effect on the decision of NU first
bit. Hence, there are two situations: The FU first bit is error-free and in error.
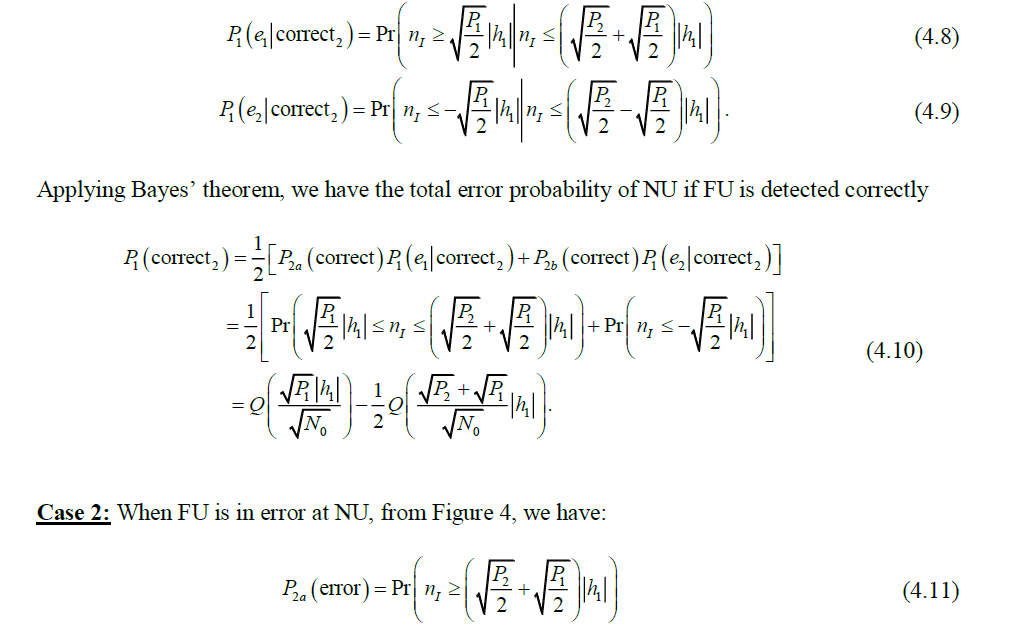
Case 1: When FU is error-free at NU, from Figure 4, yields:
After SIC process, the reference constellation for NU is given in Figure 5 [12, 13]
Figure 5. Reference constellation for NU after SIC when FU is error-free
From (4.6), (4.7) and 5, the error probabilities of NU are conditional probabilities as

Assume that the first bit of UE2 being transmitted is 0’ but detected as 1’, after the SIC process,
the reference constellation of NU is given in Figure 6.

Figure 6. Reference constellation for NU after SIC when FU is erroneously detected
From (4.11), (4.12) and Figure 6, the error probability of NU when FU is in error consists of
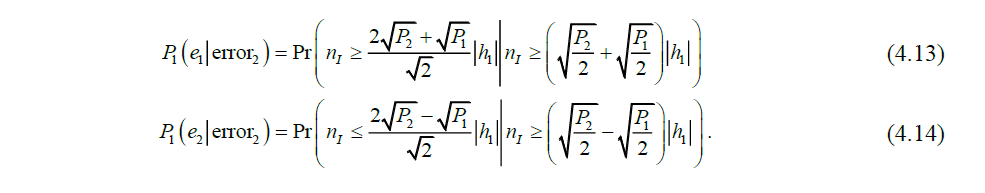
In a similar way to (4.10), the total error probability of NU when FU is erroneously detected is
obtained as

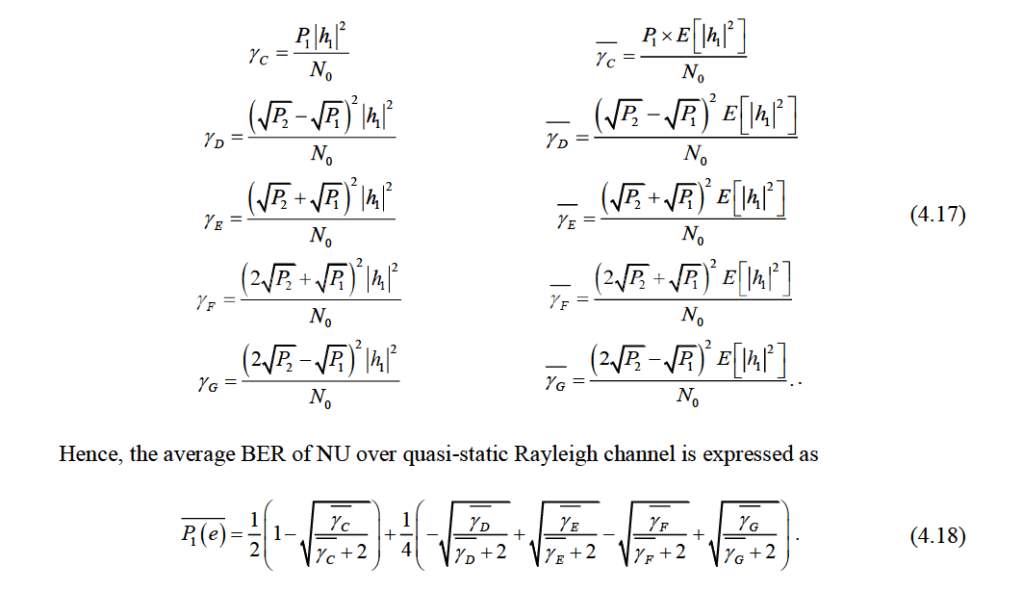
From (4.10) and (4.15), the total error probability of NU is followed by

Define some notations
5. BER IN MUST CATEGORY 2
Figure 7 shows the reference constellation to detect signals at each UE when using MUST
category 2. Red bits denote FU’s bits, and black bits are NU’s bits. The order of bits is ascending,
where the most significant bit is leftmost and is stated as the first bit. Gray-coded mapping is
conserved for adjacent symbols.

Figure 7. Reference constellation at the receiver when using MUST cat.2
5.1. BER of Far User
For MUST cat.2, from Figure 7, mapping rules for FU’s bits remains unchanged comparing to
MUST cat.1. Therefore, BER expressions of UE2 in this case are identical to (4.3) and (4.5).
5.2. BER of Near User
In this section, authors proposed another approach to analyze BER of NU, different from Section
4.2 and [10-13]. For UE1, error probabilities depend on the last two bits of a symbol. As a result
of constellation symmetry and equal prior probabilities, the third and fourth bits are the same in
error probabilities. The third bit is in error when one of these cases happens
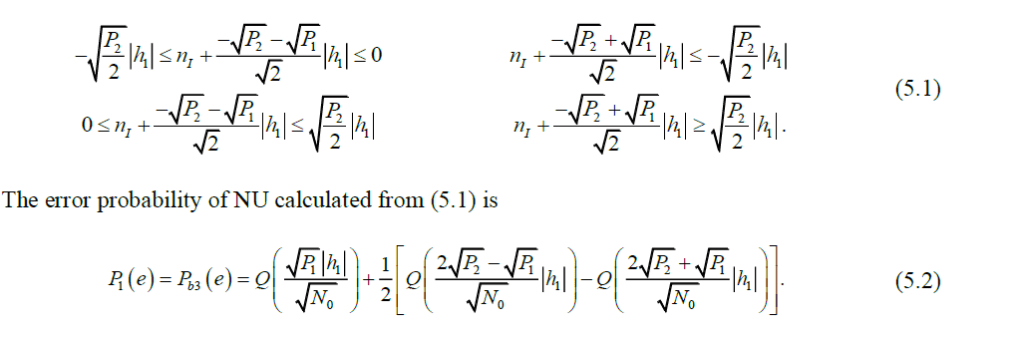
And the average BER expression of NU over the quasistatic Rayleigh channel is given by (5.3),
with notation in (4.17)
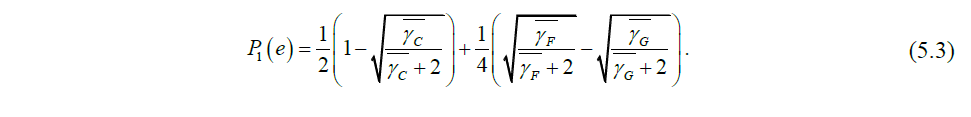
If we use the above approach for MUST cat.1, UE1 BER expressions obtain the same result as
(4.16) and (4.18)[12, 13]. Compare (4.16) and (5.2) or (4.18) and (5.3), a BER expression of
MUST cat.2 has only three out of five components of MUST cat.1, hopefully leading to lower
BER.
6. BER IN MIMO-NOMA
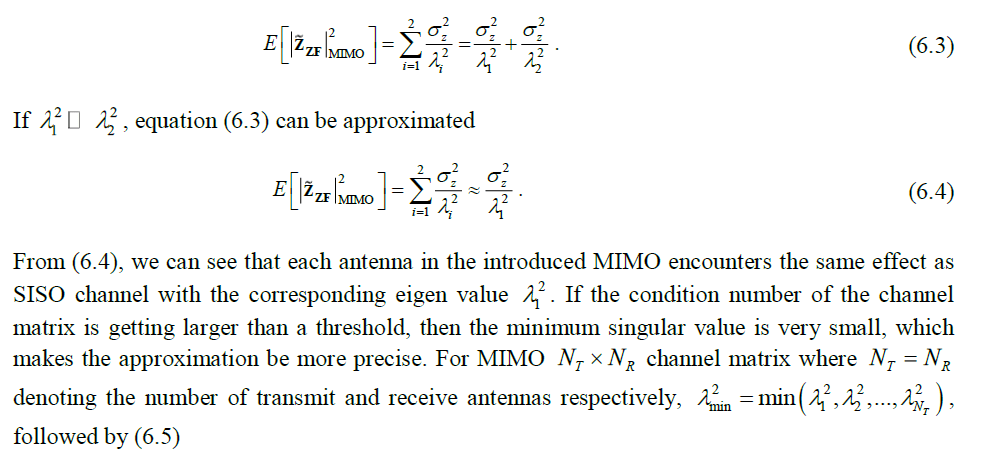
As derived in Section 3.2, we have the equalized signal, more specifically expressed as[19, 21]
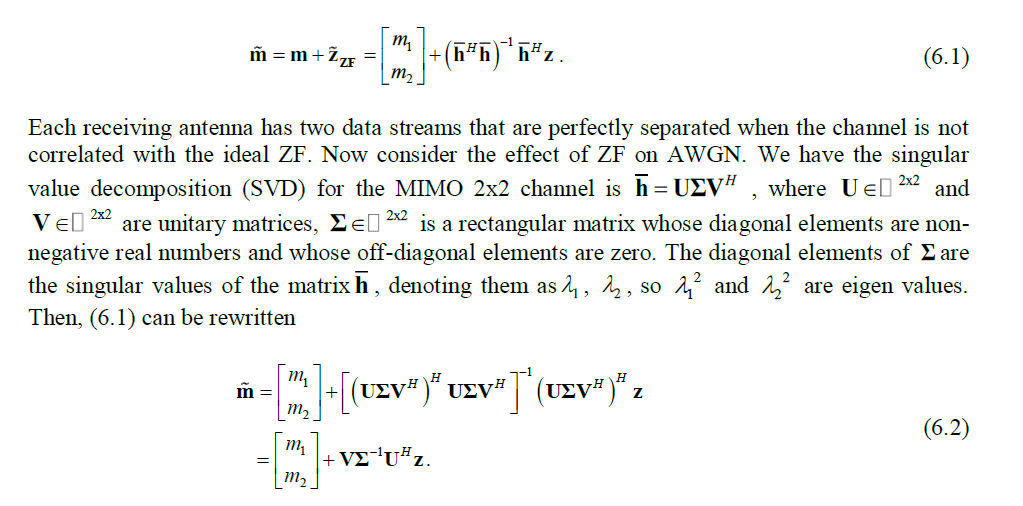
From (6.2), for uncorrelated MIMO channels, eigenvectors are linearly independent leading to
their singular values are non-zero and non-repeated, the expected value of noise power at fixed
eigen values is given as [21]

7. NUMERICAL AND SIMULATION RESULTS
In this section, the authors used Monte Carlo simulation over independent symbols to verify all
proposed expressions, under different power allocation ratios and MUST types corresponding to
the model in Figure 1 and Figure 2. Simulation parameters are specified in Table 1.
Table 1. Simulation parameters for single tap fading channels
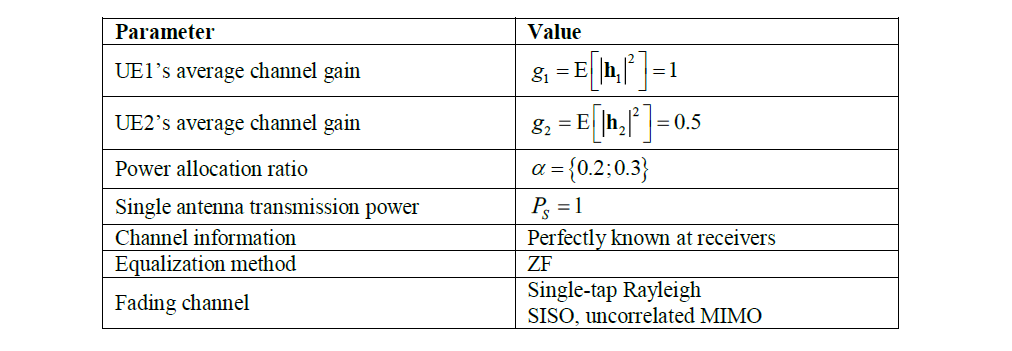


Figure 8. BER of two users in SISO-NOMA using MUST cat.1 with different power allocation ratios


Figure 9. BER of two users in MIMO-NOMA using MUST cat.2 with different power allocation ratios
Figure 10 shows the results when the SISO channel has multiple taps, we need to scale the
analytical expression SNR, but due to error in limited ZF equalization causing ISI, simulations
barely fit derived BER formulas. When the system is combined with OFDM (see Table 2 for
parameters), BER curves match the expressions due to ISI elimination in cyclic prefixes. It is
noteworthy that SNR must be scaled for OFDM signals.
Table 2. Simulation parameters for two-tap fading channels
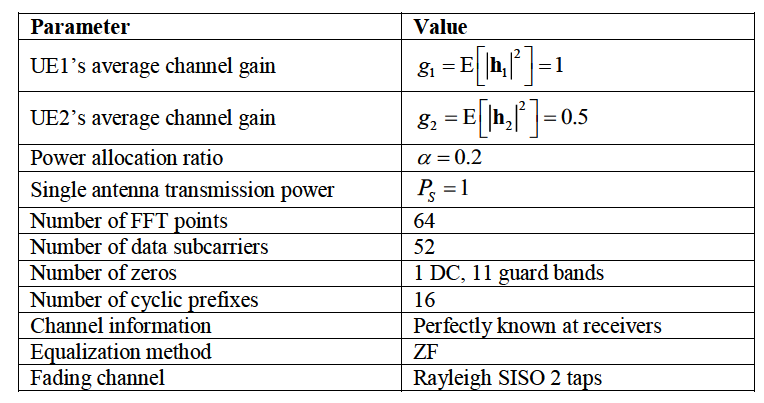
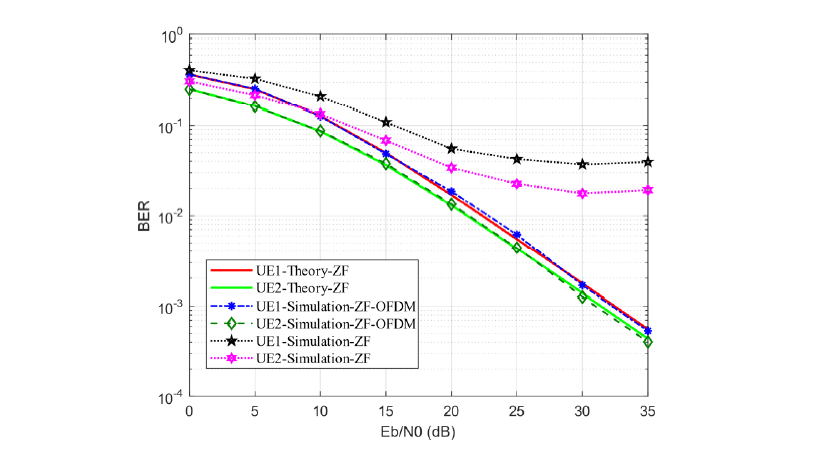
Figure 10. BER of two NOMA users in SISO-ZF-OFDM and SISO-ZF systems using MUST cat.1
8. CONCLUSION AND FUTURE WORK
This research has introduced BER expressions for downlink MIMO-NOMA-ZF systems using a SIC receiver, serving two users with QPSK modulation over an uncorrelated quasi-static Rayleigh channel. Simulation results are perfectly matched with analytical expressions, not only in different power allocation ratios but also MUST type 1 and 2 for signal generations. The results show that MUST type 2 has better performance than type 1 due to Gray-mapping rules, and when combined with OFDM, the system can minimize ISI, the simulations fit well with the proposed theory. An approach to compare the performance between SISO and MIMO in the NOMA system has also been clarified.
When the channel is bad or there is no need for high data rate, we can consider using diversity instead, such as space-time coding, or develop a machine-learning detection system to ensure integrity. Future work can be conducted for higher modulation orders, antenna beam forming, optimal power allocation, MMSE or different equalization techniques, increasing the number of users, having non-linear effects, and over correlated channel models.
CONFLICT OF INTEREST
The authors declare no conflict of interest.
ACKNOWLEDGMENT
This research is funded by Vietnam National University HoChiMinh City (VNU-HCM) under grant numberC2019-18-32.
REFERENCES
[1] Y. Liu, Z. Qin, M. Elkashlan, Z. Ding, A. Nallanathan, and L. Hanzo, “Nonorthogonal Multiple Access for 5G and Beyond,” Proceedings of the IEEE, vol. 105, no. 12, pp. 2347-2381, 2017, doi: 10.1109/JPROC.2017.2768666.
[2] Y. Liu, W. Yi, Z. Ding, X. Liu, O. Dobre, and N. Al-Dhahir, Application of NOMA in 6G Networks: Future Vision and Research Opportunities for Next Generation Multiple Access. 2021.
[3] K. Dang, H. Ngo, and N. Nguyen, “Performance of non-orthogonal multiple access downlink system using the Log-Likelihood ratio,” Science and Technology Development Journal – Natural Sciences, vol. 4, no. 3, pp. 621-632, 2020, doi: 10.32508/stdjns.v4i3.662.
[4] Narengerile and J. Thompson, “Deep Learning for Signal Detection in Non-Orthogonal Multiple Access Wireless Systems,” in 2019 UK/ China Emerging Technologies (UCET), 21-22 Aug. 2019 2019, pp. 1-4, doi: 10.1109/UCET.2019.8881888.
[5] J. M. Kang, I. M. Kim, and C. J. Chun, “Deep Learning-Based MIMO-NOMA With Imperfect SIC Decoding,” IEEE Systems Journal, vol. 14, no. 3, pp. 3414-3417, 2020, doi: 10.1109/JSYST.2019.2937463.
[6] A. Agarwal, R. Chaurasiya, S. Rai, and A. K. Jagannatham, “Outage Probability Analysis for NOMA Downlink and Uplink Communication Systems With Generalized Fading Channels,” IEEE Access, vol. 8, pp. 220461-220481, 2020, doi: 10.1109/ACCESS.2020.3042993.
[7] J. A. Oviedo and H. R. Sadjadpour, “A Fair Power Allocation Approach to NOMA in Multiuser SISO Systems,” IEEE Transactions on Vehicular Technology, vol. 66, no. 9, pp. 7974-7985, 2017, doi: 10.1109/TVT.2017.2689000.
[8] Q. Sun, S. Han, I. C, and Z. Pan, “On the Ergodic Capacity of MIMO NOMA Systems,” IEEE Wireless Communications Letters, vol. 4, no. 4, pp. 405-408, 2015, doi: 10.1109/LWC.2015.2426709.
[9] X. Wang, F. Labeau, and L. Mei, “Closed-Form BER Expressions of QPSK Constellation for Uplink Non-Orthogonal Multiple Access,” IEEE Communications Letters, vol. 21, no. 10, pp. 2242-2245, 2017, doi: 10.1109/LCOMM.2017.2720583.
[10] F. Kara and H. Kaya, “BER performances of downlink and uplink NOMA in the presence of SIC errors over fading channels,” IET Communications, vol. 12, no. 15, pp. 1834-1844, 2018, doi: 10.1049/iet-com.2018.5278.
[11] T. Assaf, A. Al-Dweik, M. E. Moursi, and H. Zeineldin, “Exact BER Performance Analysis for Downlink NOMA Systems Over Nakagami-m Fading Channels,” IEEE Access, vol. 7, pp. 134539-134555, 2019, doi: 10.1109/ACCESS.2019.2942113.
[12] J. Garnier, A. Fabre, H. Farès, and R. Bonnefoi, “On the Performance of QPSK Modulation Over Downlink NOMA: From Error Probability Derivation to SDR-Based Validation,” IEEE Access, vol. 8, pp. 66495-66507, 2020, doi: 10.1109/ACCESS.2020.2983299.
[13] T. Assaf, A. J. Al-Dweik, M. S. E. Moursi, H. Zeineldin, and M. Al-Jarrah, “Exact Bit Error-Rate Analysis of Two-User NOMA Using QAM With Arbitrary Modulation Orders,” IEEE Communications Letters, vol. 24, no. 12, pp. 2705-2709, 2020, doi: 10.1109/LCOMM.2020.3020161.
[14] Y. Saito, Y. Kishiyama, A. Benjebbour, T. Nakamura, A. Li, and K. Higuchi, “Non-Orthogonal Multiple Access (NOMA) for Cellular Future Radio Access,” in 2013 IEEE 77th Vehicular Technology Conference (VTC Spring), 2-5 June 2013 2013, pp. 1-5, doi: 10.1109/VTCSpring.2013.6692652.
[15] E. Stergiou, C. Angelis, and S. Margariti, “Evaluation Methodology of MIMO Networks Performance over Rayleigh Fading,” International journal of Computer Networks & Communications, vol. 12, pp. 37-52, 01/31 2020, doi: 10.5121/ijcnc.2020.12103.
[16] M. Aljumaily and H. Li, “Mobility Speed Effect and Neural Network Optimization for Deep MIMO Beamforming in mmWave Networks,” International Journal of Computer Networks and Communications, vol. 12, pp. 1-14, 11/24 2020, doi: 10.5121/ijcnc.2020.12601.
[17] 3GPP. “Study on Downlink Multiuser Superposition Transmission (MUST) for LTE.” https://itectec.com/archive/3gpp-specification-tr-36-859/ (accessed 2021).
[18] G. Americas, Wireless Technology Evolution Towards 5G: 3GPP Release 13 to Release 15 and beyond. 2017.
[19] A. Goldsmith, Wireless Communications. Cambridge University Press, 2005.
[20] M. K. Simon and M.-S. Alouini, Digital Communication over Fading Channels, Second ed. John Wiley & Sons, Inc., 2004.
[21] Y. S. Cho, J. Kim, W. Y. Yang, and C. G. Kang, MIMO‐OFDM Wireless Communications with MATLAB. John Wiley & Sons (Asia) Pte Ltd, 2010.
[22] I. S. Gradshteyn and I. M. Ryzhik, D. Zwillinger and V. Moll, Eds. Table of Integrals, Series, and Products, Eighth ed. 2014.
AUTHORS

Vu Tran Hoang Son received a B.S. degree in Electronics and Telecommunications, minor in Telecommunications and Networks, from the University of Science, Vietnam National University, HoChiMinh City (VNU-HCM).
He is focusing on new-generation mobile networks and wireless communications.

Dang Le Khoa graduated B.E. and Ph.D. in Radio Physics and Electronics from University of Science, Vietnam National University, HoChiMinhCity (VNU-HCM). He is the head of the Telecommunications and Networks Department, University of Science, VNU-HCM. His current research interests are in the areas of wireless communications and digital signal processing for telecommunication.

