IJCNC 06
A Cooperative Approach to Extend Cellular Coverage via D2D Architecture based on OLSR Protocol
Youssef Lmoumen1, Yassine Ruichek1 and Raja Touahni2
1CIAD, University Bourgogne FrancheComté, UTBM, France
2LASTID, University IbnTofail, Kénitra, Morocco
ABSTRACT
The access part of all cellular network’s generation suffers from common concerns related to dead spots (zones that are not covered by the network) and hot spots (zones where the number of users is higher compared to network resources). During the last decade, lots of research proposals have tried to overcome cellular problems through multi-hop D2D architecture, which is a new paradigm allowing the direct communication between devices in cellular network to enhance network performances and improve user QoS. In this paper, we propose a multi-hop D2D architecture based on the OLSR protocol to extend cellular coverage. Cell-OLSR, which is the proposed adaptation of OLSR for our architecture, allows the exchange of cellular parameters between nodes to choose the best proxy device to forward data to the cellular base station (BS).
KEYWORDS
Ad hoc, Cellular, D2D, OLSR& Coverage.
1. INTRODUCTION
Cellular networks have known an important evolution in the last three decades. From 1rst and 2nd generations for basic voice services to 3rd and 4th generations for content and data services then 5G for mMTC, eMBB and uRLLC services, cellular networks constitute a mandatory communication technology nowadays. Yet, like all radio communications, the access area in all cellular networks suffers from a multitude of problems that can affect the end-user services. In fact, dead spots are a major drawback in such networks. In this type of zones, the received signal is very weak due to obstacles hindering wave propagation such as shadowing, interference and multipaths… Cellular customers in these areas (lift, tunnel, network edges, etc.) cannot benefit from telecommunications services. Another problem in cellular networks is hot spots. In such zones, the number of cellular clients is very high in comparison to network resources. This can have an impact on customer services, particularly data services that require high end-to-end throughput.
To cope with these kinds of problems, telecommunications operators must deploy more infrastructures and ensure sufficient network resources in order to guarantee a good quality of service to the end customer. In fact, microcells and pico-cells can be deployed in zones suffering from weak signals and a lack of cellular resources. However, the cost of this operation is very high since it includes the planning cost, the energy cost, the maintenance cost, the frequency licenses cost, etc. D2D communication is identified as a motivating alternative to overcome the main weaknesses of the access area of cellular networks with lower cost [1]. In this communication mode, a mobile can create ad hoc links with nearby mobiles to reach the cellular base station [2]. D2D communication can be achieved in licensed frequencies or free frequencies. This communication can be handled by the base station as it can be distributed without the utilization of a centralized entity. The development of D2D technology, with all the projected performances and enhancements, necessitates new routing protocols or the reworking of ad hoc protocols to establish the routing decisions and select the suitable mobile, in order to link the ad hoc and the cellular zones. In this paper, we propose a distributed multi-hop D2D architecture based on the Optimized Link State Routing Protocol [3](OLSR) in unlicensed frequencies, permitting the extension of the cellular coverage. The new Cell-OLSR allows the exchange of cellular parameters between D2D nodes in order to find out the best node to ensure the interface with a cellular network. The proposed adaptation was built following two approaches that have been evaluated and compared using the OMNET ++ simulator[4].
The rest of the paper is organized as follows. In section 2 we will present a review of multi-hop D2D architectures with related routing schemes. Section 3 will be dedicated to describing the proposed architecture to extend cellular coverage and the principle of Cell-OLSR protocol with its two approaches, and the proposed selection mode algorithm. In section 4, we compare the performances of both approaches in terms of added overhead. We propose, in the same section, implementation of Cell-OLSR on OLSR_ETX version then compare the performances with AODV and DSR protocols which constitute the base of many D2D proposals. Section 5 concludes the paper and highlights some future perspectives.
2. RELATED WORKS
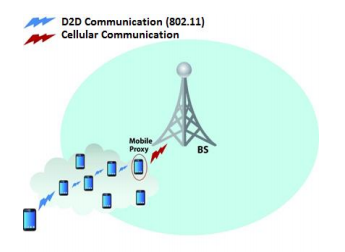
Multi-hop D2D communication is the direct communication between two mobiles or between a base station and a mobile through one or more relays in order to improve cellular performances especially those related to data end to end throughput [17], [18] (figure 1). This communication can be accomplished either in licensed frequencies, in free frequencies ISM (industrial, scientific and medical) or in hybrid bands. Relays in multi-hop D2D architecture can be either mobile or fixed relays.
In the two last decades, a lot of works focused on developing multi-hop D2D communications, which are known as multi-hop cellular networks (MCN). Table I presents some of the related works that have discussed the D2D communications through different nomenclatures. The analysis of these architectures is performed in [19]. Other D2D architectures were proposed in [20].
Among the main classification factors of multi-hop D2D architectures, we can cite:
Frequency bands: is the main design factor in D2D communication classification. Indeed, there are 3 possible methods to communicate in D2D architecture. The first one is to use licensed bands in both relaying zone and last hop link between the last mobile and base station. In this case, channel assignment procedures should be used in relaying part [21]. It is possible also to assign different frequencies in relaying and cellular parts. The issue with this option is the high cost to own frequency licenses. The second mode is to use ISM band in both cellular and relay parts. In this case, the BS is like an AP (Access Point) in WLAN (Wireless Local Area Network). The major concern with this design is the small coverage permitted by this kind of frequencies. The third mode is to associate licensed and free frequencies. In fact, the licensed frequencies can be used in the cellular area and ISM bands in the ad-hoc zone [22]. The main challenge with this architecture is to design an appropriate routing protocol.
Figure 1. D2D communication architecture
Table 1. Comparison of D2D architectures
The Number of interfaces: New smartphones can establish simultaneous communications using different radio interfaces (Cellular, Wi-Fi, Bluetooth…). In D2D communication, we can find communication using a unique interface, cellular or WLAN. We can also find cases using both interfaces
Charging and rewarding: this factor is one of the most challenging parameters in D2D communications [23]. It allows making the design of a charging way to bill the client initiating the first request of communication. It also permits proposing a rewarding mechanism for relaying mobiles that contribute to the architecture.
Relay Nature: either mobile or fixed relays can be used in D2D architecture [5], [6]. Mobile relays present difficulties to handle mobility inside the architecture. Fixed ones necessitate high cost for deployment and maintenance.
Routing approach: as mentioned, routing is one of the main design aspects in D2D communication especially when free bands are adopted. We can talk about distributed routing in which mobiles try to discover the best routing path to forwarding data [14], or centralized routing in which the BS or/and another fixed equipment manage the routes between mobiles [15]. There is also network-assisted routing. In this mode, devices can make decisions autonomously, however their decisions are based on the measurements provided by the network [16]
3. MULTI-HOP D2D ARCHITECTURE
In this section, we introduce our proposed multi-hop D2D architecture to extend cellular coverage. Then, we develop the principle of the Cell-OLSR protocol with its two approaches.
3.1. Proposed architecture
We propose a multi-hop D2D communication in ISM bands using 802.11 standard and proactive routing with a modified version of OLSR protocol.
As shown in figure 2, a user out of cellular coverage can communicate with BS through a set of other mobiles using 802.11 standards. The Cell-OLSR protocol allows the exchange of cellular parameters between mobiles in order to designate the best proxy to forward data to a cellular network.
Table 2 summarizes the characteristics of our method following the classification factors discussed in section 2.
We propose different approaches to OLSR protocol adaptation and we indicate the use cases of each approach. Our proxy choice metrics will be essentially the quality of the cellular signal received from the BS, the type of cellular access technology, and the capability of the node to be elected as proxy according to its battery level and its load.
Table 2. Proposed architecture parameters
Figure 2. Proposed multi-hop D2D architecture
3.2. Cell-OLSR
Cell-OLSR is an adaptation of the OLSR protocol that ensures the exchange of cellular parameters between nodes to choose the best proxy. The proactive nature of the OLSR protocol will allow us to insert and broadcast cellular parameters, and then each node will constitute a database containing cellular information of other nodes in the network.
Cellular parameters that will be exchanged between nodes are:
- The cellular access technology
- The received signal strength from the base station
- Node capability to be elected as a proxy
In order to spread these parameters in the ad hoc network, we apply two approaches to OLSR packets.
3.2.1. First approach: Cell-OLSR1
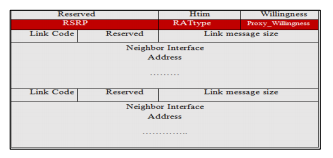
The first approach is to build a new control message that will be encapsulated in the OLSR header. Like the TC and MID messages, this message will be generated by each node in the network and propagated through the MPRs nodes only. We call the new message CP (Cellular Parameters). Figure 3 shows the format of this message.
Figure 3. CP message format
RSRP (Reference Signals Received Power) represents the power of the signal received from the base station. The RSRP field is double-byte. RATtype (Radio Acess Type) represents the type of communication technology (3G,4G,5G). The RAType field is single-byte. Proxy_Willingness defines the capability of the node to be chosen as a proxy. This field is coded on 1 byte.
The CP message will be generated by each node of the network, but will only be forwarded by the MPRs. Upon receipt of the CP message, the node will update a cellular database that contains tuples with the following fields:
- C_main_addr : the main address of the origin node of the CP message
- C_RAT : Cellular technology to which the originating node of the CP message is connected
- C_RSRP : received signal strength, from the base station, of the origin node of the message CP
- C_Will_P : Capability of the node to be elected as a proxy
- C_Time :validity time of the CP message.
The update process is as follows:
Algorithm1:the update process
For each received CP message
Ifthe sender is not a symmetric neighbor, the message is ignored.
Else, if it exists a tuple where:C_main_addr=originator address
Then modify other parameters:
C_RAT = RAType
C_RSRP = RSRP
C_Will_P = Proxy_Willingness
C_time =current time + validity time
Else, if no tuple exists with previous condition, then create new tuple with parameters:
C_RAT = RAType
C_main_addr = originator address
C_RSRP = RSRP
C_Will_P = Proxy_Willingness
C_time =current time + validity time
The exchange of the CP message in the network will allow each node to maintain a table with the cellular information about the other nodes.
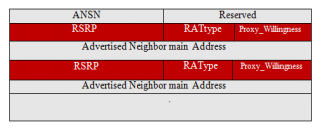
3.2.2. Second approach: Cell-OLSR2
In the second approach, we propose to use the HELLO and TC messages to insert the RSRP, RAType and proxy_willingness parameters. Indeed, a header will be added to the HELLO message to inform the cellular parameters of the sending node. For TC message, these parameters will be filled in for each neighboring node of the MPR, sending the message.
Figures 4 and 5show the format of HELLO and TC messages before adding the cellular parameters.
Figure 4. Format of hello message
Figure 5. format of TC message
After adding the cellular parameters. The HELLO and TC message structures become as illustrated in Figures 6 and 7.
Each node will inform their neighbors about his cellular parameters in the Cell-HELLO message. Upon receipt of the Cell-HELLO message, the node will update the neighbor set that contains tuples with the following fields:
- N_neighbor_main_addr: The main address of the neighbor
- N_status: The status of the neighbor
- N_willingness: The node’s willingness to carry traffic on behalf of other nodes
- N_RAT : Cellular technology of the neighbor
- N_RSRP : received signal strength, from the base station, of the neighbor
- N_Will_P : Capability of the neighbor to be elected as a proxy
Beyond the neighbors, cellular parameters are exchanged via Cell-TC message. Upon receipt of the Cell-HELLO message, the node will update the neighbor set that contains tuples with the following fields:
- T_dest_addr : Address of destination node
- T_last_addr : Addressof last node before destination ( typically is an MPR of T_dest_addr)
- T_seq :Sequencenumber.
- T_RAT : Cellular technologie of destination node
- T_RSRP : Received signal strength, from the base station,of T_dest_addr node
- T_Will_P : Capability of T_dest_addr to be elected as proxy
- T_time :specifies the time at which this tuple expires and must be removed
Figure 6. format of cell-HELLO message
Figure 7. format of cell-TC message
The population and update of the neighbor set and topology set follow the specifications of OLSR [3].
3.2.3. proxy_willingness parameter
Like the Willingness parameter of the OLSR protocol, the proxy willingness parameter translates the ability of a mobile to be chosen as a proxy between the ad hoc network and the cellular network. Unlike the willigness parameter, which only considers the state of the battery to set the willingness value, the proxy_willingness parameter adds the constraint of the load on a mobile to limit the number of mobiles that can be served by a proxy. Indeed, the load makes possible to control the number of mobiles with whom the mobile proxy shares its cellular resources.
The metric defining the proxy_willingness parameter is therefore a function of the battery and the load supported by the proxy mobile according to the following equation.
M = αB + βL
M is a metric that sets the value of the proxy_willigness parameter. B represents the state of the battery. L represents the charge on the proxy mobile, or the number of served mobiles. α and ß are weights related to the battery and the load, and will define the importance of each metric in the choice of the proxy 0 ≤ α, ß ≤1 and α + ß = 1.
3.2.4. Communication algorithm
After exchanging cellular parameters in the network using the Cell-OLSR protocol, each node will build a database on each of the other nodes containing the cellular parameters. This database will be used to select the most appropriate proxy mobile to communicate with the base station. Indeed, depending on its coverage status, a mobile can communicate with the BS either directly or by using relays through D2D communication. The coverage extension algorithm is illustrated in figure 8:
Figure 8. Communication algorithm using Cell-OLSR protocol
Before sending the data to the base station, the mobile verifies the value of the RSRP received from the BS. If this value is greater than a predefined threshold, the mobile sends its data flow directly to the base station using the cellular interface. If the RSRP value is lower than the threshold, the mobile initiates the search process of the proxy a mobile based on the information collected following the exchange of the Cell-OLSR protocol. The mobile checks in its base the mobile connected to the base station with the desired technology having the greatest value of the RSRP among the nodes of the ad hoc network and predisposed to be elected as mobile proxy. If the mobile is found, the data will be sent via the OLSR protocol using the 802.11 standards. Otherwise, direct transmission via the cell link is envisaged.
The value of WILLINGNESSref depends on the coverage conditions. For example if we suppose M between 0 and 1 (0 for bad proxy and 1 for good proxy), we can define Mref=0,3 when the coverage conditions are bad, to have the maximum number of potential proxy’s. When the coverage condition is OK, we can define Mref=0,7 for example to push mobiles to choose
the direct link.
4. PERFORMANCE EVALUATION
In order to evaluate the two proposed approaches of the Cell-OLSR protocol, we suggest a comparison between both approaches and the OLSR native version. Through these simulations we demonstrate the most optimal approach, especially regarding the overhead rate added to the network. The overhead is defined as the number of all the routing control packets that each node sends in order to know the network and establish and maintain the routes. This metric is used to measure the efficiency of the routing protocol. An additional overhead can have impacts on the network bandwidth and the power consumption.
4.1. Simulation environment
We use INET framework [24] of OMNET++ simulator. Simulation parameters are shown in Table 3.
We assign random values of cellular parameters to simulation nodes. We measure the added overhead in both approaches. For cell-OLSR1, we evaluate the overhead for different values of CP interval. The number of nodes describes the range of the coverage extension allowed by D2D part. As 802.11 standards allows communication range with highest throughput between 20m and 40m in indoor environment. Therefore, with 5 nodes a minimum extension of 100m can be reached towards the base station, while with 15 nodes, the extension can reach up to 600m extension. This extension range should be sufficient in urban environment to reach the BS. We choose random mobility with speed between 0mps and 5mps for walking cases in urban area.
Table 3. Simulation parameters
4.2. Simulation Results
The comparison results of the added overhead of Cell-OLSR and OLSR are shown in figure 9. We can see from results that Cell-OLSR1 generates more overhead comparing to Cell-OLSR2 and OLSR especially when the interval time of CP message equals to 2ms (up to 50% of supplementary overhead against 14% only for Cell-OLSR2). The result is normal since a new message with its header is generated in Cell-OLSR2 approach. The overhead increase in the Cell-OLSR2 is due to inserted cellular parameters in control messages (2 bytes for RSRP, 1 byte for RAType and 1 byte for proxy_Willingness).
Figure 9. Routing overhead comparison for different intervals of CP message
The Cell-OLSR1 approach allows the exchange of RSRP, RAType and Proxy_Willingness information. However, adding a new messages has two major drawbacks on protocol performance:
- Additional overhead: Generation and exchange of additional control message can degrade network performance, especially bandwidth and energy.
- Additional processing is necessary to ensure the good management of the new message and its processing.
Cell-OLSR2 version remains an optimal choice for the diffusion of cellular parameters while preserving OLSR performance in terms of generated overhead. However, the need to broadcast other cellular parameters for the different access technologies, in order to guarantee a more optimal and finer choice of the proxy mobile, requires grouping these parameters in a separate control message. This would in particular make possible the setting of an eigenvalue for the CP message sending interval and possibly define particular rules for updating the cellular parameters on the CP database. Among these rules we can mention:
- Generate and send a CP messages when a RAT change is performed.
- Generate and send CP message according to variations in the quality of the received signal from the BS. Trigger the generation of the CP message according to the value of Proxy_Willingness to update information in other nodes
The Advantages and disadvantages of each approach are summarized in Table 4.
Table 4. Comparison of Cell-OLSR approaches
4.3. Application to OLSR-ETX
One common advantage of both approaches of Cell-OLSR is the implementation flexibility in different OLSR extensions. Indeed, various OLSR versions were proposed in the literature to deal with different problems like security [25], energy consumption [26] and QoS [27].
In this section, we propose to apply the Cell-OLSR2 approach (approach with less overhead) on the OLSR_ETX [28] version available on the OMET ++ INET and INETMANET frameworks, and carry out a comparison with the AODV and DSR protocols as well as Cell-OLSR2 variant. The AODV and DSR protocols formed the basis of several proposals in the D2D domain [29],
[30].
The OLSR_ETX (Expected Transmission Count) version uses the quality of the link between two nodes in the network instead of the number of hops, in the original version, to calculate the route.
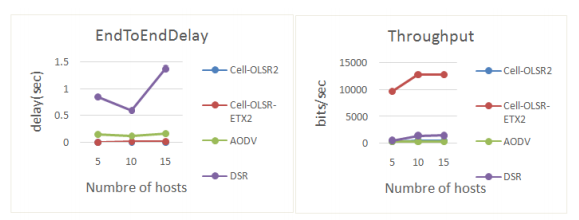
We call the new version of OLSR_ETX with the cell-OLSR approach, Cell-OLSR-ETX2. This version is compared to AODV, DSR and Cell-OLSR2 in terms of throughput and E2E delay which are two fundamental KPIs in D2D architecture.
We use the same parameters defined in table 3, with a simulation time of 500s and a simulation area of 1500m×1500m.
The simulation results are shown in Figure 10.
Figure 10. Comparison of E2E delay and throughput
We note through these results that the Cell-OLSR-ETX2 and Cell-OLSR2 protocols perform best in comparison with AODV and DSR in terms of E2E delay. Indeed, the OLSR protocol does not need much time in the route discovery mechanism. Routes are always available in advance on routing tables because of its proactive nature, resulting in lower end-to-end delays. ETX metric-based routing allows Cell-OLSR-ETX2 to achieve good throughput performance compared to other protocols as shown in Figure 10.
Through this study, we have demonstrated the flexibility of implementation of our Cell-OLSR concept on the ETX variant of OLSR. Admittedly, this variant may be a better alternative for our D2D architecture given the presented performances.
5. CONCLUSION
The Cell-OLSR approach may constitute a good alternative to solve the problems of the access part of cellular networks by broadcasting the parameters exchanged between the mobile and the base station. Several algorithms can combine the different parameters to highlight the most optimal proxy node. In this paper, we presented our D2D architecture to address the issue of cellular coverage. We presented our design of the Cell-OLSR protocol with two possible implementation approaches. We tested and compared both approaches to propose the scope of each of them. We then implemented Cell-OLSR second approach on the OLSR-ETX variant to demonstrate the flexibility of the concept. We performed a series of comparative simulations with the AODV and DSR protocols to demonstrate the performance of this OLSR variant.
Our Approach may constitute a good alternative to enhance cellular performances especially in terms of coverage extension through D2D architecture. Nevertheless, other aspects need to be considered in such architecture especially regarding security and power consumption in relay
and proxy nodes.
Finally, as future works, we note that our approach can be the subject of further studies to optimize the performance of the cellular network, including the problem of cell overload. Indeed, the D2D communication in the ISM bands can be exploited to route the mobile traffic from a loaded cell to a cell with more radio resources. The Cell-OLSR protocol can include other parameters that can help to achieve this routing in the most optimal way.
CONFLICTS OF INTEREST
The authors declare no conflict of interest.
ACKNOWLEDGEMENTS
We would like to thank everyone who helped make this work a reality! Special thanks to Nadia El Kamel and Yousssef Frist (University IbnTofail) for their support in simulation environment.
REFERENCES
[1] LIN, Xingqin, ANDREWS, Jeffrey G., GHOSH, Amitabha, et al. An overview of 3GPP device-todevice proximity services. IEEE Communications Magazine, 2014, vol. 52, no 4, p. 40-48.
[2] BABUN, Leonardo, YÜREKLI, Ali Ihsan, et GÜVENÇ, Ismail. Multi-hop and D2D communications for extending coverage in public safety scenarios. In : 2015 IEEE 40th local computer networks conference workshops (LCN Workshops). IEEE, 2015. p. 912-919.
[3] CLAUSEN, Thomas, JACQUET, Philippe, ADJIH, Cédric, et al.“Optimized link state routing protocol (OLSR)”. inria-00471712, version 1, 2003.
[4] VARGA, Andráset HORNIG, Rudolf. “An overview of the OMNeT++ simulation environment”. In: Proceedings of the 1st international conference on Simulation tools and techniques for communications, networks and systems & workshops. ICST (Institute for Computer Sciences, SocialInformatics and Telecommunications Engineering). p. 60, 2008
[5] Y.-D. Lin and Y.-C. Hsu, “Multihop cellular: A new architecture for wireless communications,” in Proc. of IEEE INFOCOM, 2000, vol. 3, pp. 1273-1282.
[6] H. Wu, C. Qiao, S. De, and O. K. Tonguz, “Integrated Cellular and Ad-Hoc Relay Systems: iCAR,” IEEE J. Sel. Areas Commun., vol. 19, no. 10, pp. 2105-2115, Oct. 2001.
[7] G. N. Aggelou and R. Tafazolli,” On the relaying capability of next-generation GSM cellular networks,” IEEE Personal Communications, vol. 8, no.1, pp. 40–47, 2001.
[8] N. B. Salem, L. Buttyán, J.-P. Hubaux and M. Jakobsson, “A charging and rewarding scheme for packet forwarding in multi-hop cellular networks,” in Proc. of the 4th ACM Int. Symp. on Mobile Ad Hoc Networking &Computing,2003, pp. 13-24.
[9] H. Luo, R. Ramjee, P. Sinha, L. Li and S. Lu, “UCAN: A unified cellular and ad hoc network architecture,” in Proc. of the 9th Annual Int. Conf. on Mobile Computing and Networking, 2003, pp. 353-367.
[10] Y.-J. Choi, J. H. Jun and S. Bahk, “Profit-based routing for multihope coverage extension in wireless networks,” Wireless Personal Communications, vol. 42, no. 4, pp. 465-478, 2007.
[11] B. Carbunar, I. Ioannidis and C. NitaRotaru, “JANUS: Towards robust and malicious resilient routing in hybrid wireless networks,” in Proc. of the 3rd ACM Workshop on Wireless Security, 2004, pp. 11– 20.
[12] B. S. Manoj, R. Ananthapadmanabha, and C. S. R. Murthy, “Multi-hop cellular networks: Architecture and protocols for best-effort and real-time communication,” Journal of Parallel and Distributed Computing.,vol. 65, no. 6, pp. 767-791, June 2005.
[13] Third Generation Partnership Project (3GPP), Technical Specification Group Radio Access Network, Opportunity Driven Multiple Access (ODMA), Sophia Antipolis, Valbbonne (3G TR 25.924 Version 1.0.0), 1999.
[14] B. Coll-Perales and J. Gozalvez, “Contextual optimization of location-based routing protocols for multi-hop cellular networks using mobile relays,” Telecommunication Systems, pp. 1572-9451, April 2015.
[15] F. S. Shaikh and R. Wismuller, “Centralized Adaptive Routing in Multihop Cellular D2D Communications,” presented at the 2nd Int. Conf. on Computer and Communication Systems (ICCCS), 2017.
[16] Z. Li and H. Shen, “An efficient routing protocol to increase the com- munication reliability of multihop cellular networks,” in Proc. IEEE Mil. Commun. Conf. (MILCOM), San Diego, CA, USA, 2008, pp. 1–7
[17] J. Gui and K. Zhou, “Cellular throughput optimization by game-based power adjustment and outband D2D communication,” EURASIP J. Wireless Commun. Netw., vol. 2018,no.1, pp. 254, Oct. 2018.
[18] M. Ni and J. Pan, “Throughput analysis for downlink resource reusing D2D communications in cellular networks,” in Proc. IEEE Global Communications Conf., Dec. 2017, pp. 1-7.
[19] Youssef LMOUMEN, Yassine RUICHEK, Raja TOUAHNI. ”Multi-Hop Communications inside Cellular Networks: A Survey and Analysis”. International Journal of Electrical and Electronic Engineering & Telecommunications (IJEETC). vol.8, no.6, September 2019.
[20] FarrukhSalimShaikh, Roland Wismüller. Routing in Multi-hop Cellular Device-to-Device (D2D) Networks: A Survey. IEEE Communications Surveys & Tutorials. P2622 – 2657. 15 June 2018
[21] R. Wang, J. Zhang, S. H. Song, K. B. Letaief, “Optimal QoS-aware channel assignment in D2D communications with partial CSI”, IEEE Trans. Wireless Commun., vol. 15, pp. 7594-7609, Nov. 2016.
[22] LMOUMEN, Youssef, RUICHEK, Yassine, et TOUAHNI, Raja. Experimental evaluation of LTE throughput using D2D multi-hop communications. In : 2019 International Conference on Wireless Technologies, Embedded and Intelligent Systems (WITS). IEEE, 2019. p. 1-6.
[23] SHEN, Qingguo, SHAO, Wenjuan, et FU, Xiao. D2D Relay Incenting and Charging Modes That Are Commercially Compatible With B2D Services. IEEE Access, 2019, vol. 7, p. 36446-36458.
[24] MÉSZÁROS, Levente, VARGA, Andras, et KIRSCHE, Michael. INET Framework. In : Recent Advances in Network Simulation. Springer, Cham, 2019. p. 55-106.
[25] BHUVANESWARI, R. et RAMACHANDRAN, R. Denial of service attack solution in OLSR based manet by varying number of fictitious nodes. Cluster Computing, 2018, p. 1-11.
[26] JAIN, Rachna et KASHYAP, Indu. Energy-Based Improved MPR Selection in OLSR Routing Protocol. In : Data Management, Analytics and Innovation. Springer, Singapore, 2020. p. 583-599.
[27] JAIN, Rachna et KASHYAP, Indu. AnQoS Aware Link Defined OLSR (LD-OLSR) Routing Protocol for MANETS. Wireless Personal Communications, 2019, p. 1-14.
[28] KAKADE, Surabhi et KHANAGOUDAR, Partugouda. ‘’Performance Analysis of OLSR to Consider Link Quality of OLSR-ETX/MD/ML in Wireless Mesh Networks’’. In :2017 2nd International Conference on Computational Systems and Information Technology for Sustainable Solution (CSITSS). p. 1-10, IEEE, 2017
[29] F.S. Shaikh and R. Wismüller, “Interference-conscious routing in multihop D2D communications,” in Proc. 2nd Int. Conf. Comput.Commun.Syst.(ICCCS),2017,pp.146–151.
[30] C. Tata and M. Kadoch, “Multipath routing algorithm for device- to-device communications for public safety over LTE heterogeneous networks,” in Proc. 1st Int. Conf. Inf. Commun. Technol. DisasterManag. (ICT-DM), 2014, pp.1–7.
AUTHORS

Youssef Lmoumen received the Ph.D. degree in engineering science from University Bourgogne Franche Comté, France in 2019. He received his engineering degree in computer science from National Institute of Posts and the Telecommunications, Morocco in 2010. He was working in Telecommunication field for nine years. His current research interests include machine learning applications and wireless communications, specifically, D2D networks, cellular networks, wireless ad-hoc networks and IoT networks.

Yassine Ruichek received the Ph.D. degree in control and computer engineering and the Habilitation à Diriger des Recherches (HDR) degree in physic science from the University of Lille, France, in 1997 and 2005, respectively. Since 2007, he has been a full professor with the University of Technology of Belfort-Montbéliard. His research interests are concerned with multisensory data fusion with applications to the intelligent transportation systems.

Raja Touahni received the doctorat 3ème cycle in microelectronics from the Paul Sabatier University, Toulouse , France, in September 1986 and Ph.D. degree in field of data analysis from the IbnTofaïl University, Kenitra in 2001. Currently, she is a professor of higher education at the Physics Department, the Faculty of Sciences. She is a member of LASTID Laboratory (Telecommunications Systems and Decision Engineering) and the Head of the research team in data processing and decision engineering. Currents interests include image processing, data analysis, telecommunications and E-learning.